
The quiet efficiency with which a single malformed network packet can dismantle the perimeter of a global enterprise has never been more apparent than with the discovery of CVE-2026-0300. This guide serves to illuminate the dangers posed by this critical vulnerability while providing a roadmap for
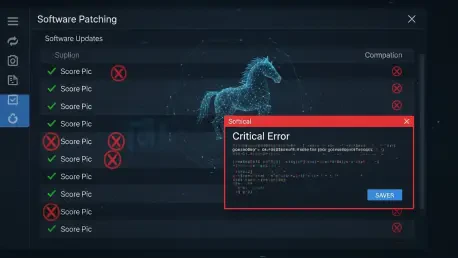
Supply Chain Integrity and the Daemon Tools Incident The modern digital landscape relies heavily on the trust between software developers and their users, a bond that is increasingly exploited through sophisticated supply chain attacks. When Disc Soft, the developer of the ubiquitous disk imaging

The subtle intersection of digital entertainment and state-sponsored espionage has reached a chilling new peak as unsuspecting users find their favorite gaming portals transformed into sophisticated tools for surveillance. This reality materialized through the compromise of sqgame[.]net, a niche

The current evolution of the global cyber threat landscape is characterized by a rapid dissolution of the traditional barriers that once separated standard enterprise system intrusions from specialized cryptocurrency theft operations. Historically, the digital underground was largely divided into

Kendra Haines sat down with Rupert Marais, our in-house Security specialist renowned for endpoint and device security, cybersecurity strategies, and hardened network management under fire. With campaigns like UAT-4356’s ArcaneDoor in the news and Firestarter proving it can outlive reboots, firmware

Home internet once felt as simple as plugging in a router, but overnight the buying rules changed when the nation’s top telecom regulator widened a ban to devices most people consider pocket essentials. The Federal Communications Commission has clarified that its month‑old prohibition on new