Supply Chain Integrity and the Daemon Tools Incident
The modern digital landscape relies heavily on the trust between software developers and their users, a bond that is increasingly exploited through sophisticated supply chain attacks. When Disc Soft, the developer of the ubiquitous disk imaging utility Daemon Tools, confirmed that its software had been compromised, it sent shockwaves through the cybersecurity community. This incident highlights the vulnerability of build environments and the devastating scale at which a single compromised installer can distribute malware globally. Understanding the timeline of this breach is essential for grasping the risks inherent in automated software updates and the rapid response required to mitigate large-scale infection attempts.
Chronological Timeline of the Supply Chain Attack
The compromise of Daemon Tools Lite followed a precise trajectory from the initial breach of the build infrastructure to the eventual cleanup and remediation by the developer.
April 8, 2024: The Initial Compromise of Version 12.5.1
Threat actors successfully infiltrated the Disc Soft infrastructure and tampered with the build environment. This allowed them to inject malicious code into the legitimate installation package for Daemon Tools Lite version 12.5.1. From this date forward, any user downloading the software from the official website unknowingly received a Trojanized version capable of establishing a backdoor on their system.
April to May 2024: Global Distribution and Infection Tracking
For nearly a month, the compromised installer remained available on the official distribution servers. Telemetry data later revealed several thousand infection attempts spanning across more than 100 countries. While the malware reached a vast number of systems, security researchers noted that further-stage payloads were selectively deployed, indicating a highly targeted operation rather than a broad, indiscriminate attack.
May 4, 2024: Discovery and Notification by Security Researchers
Cybersecurity firm Kaspersky identified the malicious behavior associated with the Daemon Tools installers. Upon confirming that the software was distributing malware, they notified Disc Soft. The analysis revealed that the campaign had a specific focus, with further-stage payloads appearing on machines belonging to government, manufacturing, and scientific organizations, as well as an educational institution in Russia.
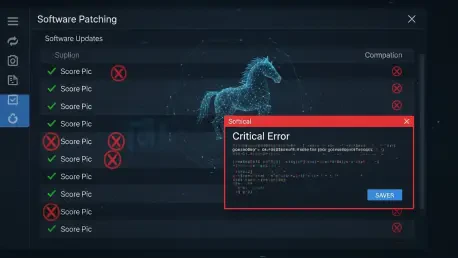
May 5, 2024: Rapid Remediation and Release of Version 12.6
Within 12 hours of receiving the notification, Disc Soft took decisive action to contain the breach. The developer isolated the affected systems within their infrastructure and removed the compromised version 12.5.1 from distribution. They subsequently released version 12.6, which was built from a verified, malware-free environment, to replace the Trojanized iteration and restore the safety of the software pipeline.
May 7, 2024: Public Disclosure and Security Audit Results
Disc Soft officially confirmed the unauthorized interference within their build infrastructure through a public statement. They detailed the steps taken to secure the release pipeline, including a comprehensive audit and the implementation of strengthened internal security controls. The developer urged all users who had downloaded the software during the window of compromise to uninstall the app and perform deep system scans to ensure no residual threats remained.
Turning Points and the Impact of Targeted Backdoors
The most significant turning point in this incident was the shift from a widespread distribution phase to a highly selective secondary infection phase. While thousands of users downloaded the Trojanized app, only a handful of specific organizations received the Quic RAT malware, a tool capable of process injection into legitimate system files like notepad.exe. This pattern suggests that the attackers were not interested in the general user base but were instead utilizing Daemon Tools as a delivery vehicle for cyber-espionage or “big-game hunting.” The speed at which Disc Soft responded—patching the app in under half a day—likely prevented a much larger scale of secondary infections, setting a benchmark for incident response in supply chain breaches.
Regional Variations and Technical Sophistication
Analysis of the victimology showed a diverse geographic spread, with heavy concentrations of infections in Russia, Brazil, Turkey, and various European nations. This distribution likely mirrors the global popularity of Daemon Tools rather than a specific regional targeting by the hackers. A common misconception in such breaches is that every infected user is at equal risk; however, as seen here, the attackers utilized advanced filtering to decide which victims warranted the deployment of more intrusive tools. The use of the Quic RAT demonstrates a level of technical sophistication aimed at evading traditional detection methods. For organizations, this event served as a reminder that even “trusted” utilities must be monitored for abnormal behavior, especially those with high-level system permissions. Organizations benefited from reviewing their endpoint detection logs for any suspicious activity originating from disk imaging tools. Future security strategies involved implementing more rigorous code-signing verifications and isolating administrative tools within air-gapped or restricted network segments to mitigate the impact of similar infrastructure compromises.