
Modern cybersecurity perimeters are disintegrating as the sheer volume of machine-driven interactions outpaces the ability of human administrators to govern access effectively. In a world where cloud workloads are spun up and deleted in seconds, traditional identity management has become a

The contemporary digital landscape is defined by an era where the most sophisticated perimeter defenses are frequently bypassed by individuals already residing within the trusted network of the enterprise. While cybersecurity budgets traditionally prioritize the mitigation of external hacking

The traditional model of smartphone insurance, which relied heavily on a policyholder filing a manual claim after a catastrophic hardware failure, has been completely upended by the integration of sophisticated machine learning algorithms. In the current landscape, the industry is transitioning
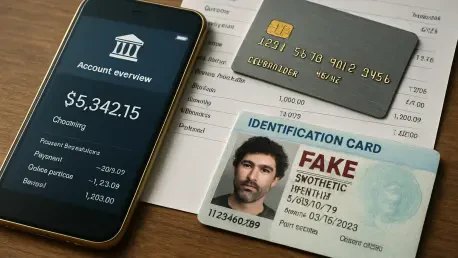
The quiet emergence of a phantom customer who possesses a valid social security number but has no physical existence represents one of the most sophisticated challenges facing the modern global financial ecosystem today. As digital banking platforms continue to prioritize seamless user experiences

A single phone call made with calculated precision can dismantle the most sophisticated cybersecurity defenses by exploiting the inherent trust found within human interaction. This specific vulnerability became the catalyst for the significant data breach at Charter Communications, illustrating

The digital architecture of the modern residence has transformed into a sophisticated hub where every appliance, from the thermostat to the refrigerator, relies on a single wireless gateway to function. This interconnectivity creates a seamless living experience but also exposes a massive attack