
The rapid metamorphosis of the software development lifecycle has reached a point where the local workstation is no longer just a tool but an active, autonomous participant in the creation of its own architecture. This review examines the fundamental shift brought about by AI coding assistants,
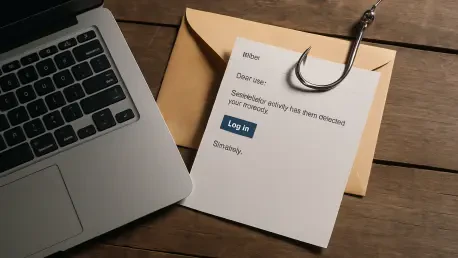
Senior-level professionals across the global technology sector are facing an increasingly sophisticated threat as cybercriminals refine their social engineering tactics to impersonate high-profile recruiters from Palo Alto Networks. This particular campaign, which has been meticulously tracked by

The modern enterprise perimeter has effectively dissolved, leaving security teams to wrestle with a sprawling ecosystem of remote devices that are as much a liability as they are an asset. At the heart of this struggle lies FortiClient Endpoint Management Solutions (EMS), a platform designed to

The subtle art of digital infiltration has shifted from loud, brute-force entries to a sophisticated game of hide-and-seek where the most dangerous code often masquerades as a harmless session identifier. While security teams traditionally focus their scrutiny on URL parameters and POST request
The traditional perimeter of corporate security has not just been breached; it has been fundamentally redefined by an adversary that never sleeps and learns at the speed of light. The landscape of cybersecurity is currently undergoing a seismic shift, driven by the rapid integration of artificial

Rupert Marais is a leading security specialist who has spent years mastering the intricate intersection of endpoint protection, network management, and large-scale cybersecurity strategy. With a deep focus on how emerging technologies can fortify enterprise environments, Rupert brings a wealth of