
Digital assistants have quietly transitioned from being simple voice-activated novelties into the primary custodians of our personal and professional lives, holding the keys to sensitive enterprise data and private identities. As these AI agents evolve into autonomous assistants, they are

The smart speaker that answers your questions and the robotic vacuum that cleans your floors have become unassuming data collectors, quietly transforming the convenience of modern living into a significant and often overlooked security liability. This research summary analyzes the escalating crisis

The discovery of a critical security vulnerability within the Grandstream GXP1600 series of Voice over Internet Protocol phones has sent ripples through the cybersecurity community, highlighting a significant oversight in how modern enterprises manage their hardware. This specific flaw, tracked as

Rupert Marais is a leading security specialist at the forefront of endpoint and device protection, focusing on the intricate vulnerabilities within mobile ecosystems and firmware integrity. With extensive experience in managing complex network threats and developing robust cybersecurity strategies,

The digital architecture of a modern enterprise now resembles a sprawling, interconnected web where a single vulnerability in a minor third-party plugin can trigger a catastrophic failure across a global network. As organizations continue to pivot toward decentralized, software-heavy environments,
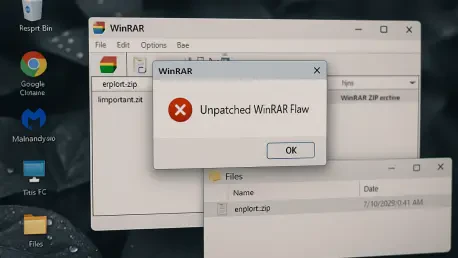
With us today is Rupert Marais, our in-house security specialist, whose expertise in endpoint security and cybersecurity strategies offers a critical perspective on today’s threats. We’re delving into a widespread vulnerability in a piece of software that many of us have used for decades: WinRAR.