
Market Context and Why It Matters Mailbox storms no longer signal mere annoyance; they now mask credential raids staged through cloud trust, browser add-ons, and scripts that look benign until they quietly seize the keys to the company. The surge in collaboration platforms and sanctioned cloud

Back-to-back meetings blur into a single rush when a trusted name on Telegram insists a quick Terminal paste will rescue a failing call, nudging macOS users to trade caution for speed at the exact moment a thief needs only one click. That is the opening the ClickFix technique exploits: it turns the

Why Passwords Finally Lost Their Last Safe Harbor Passwords are still the soft underbelly of enterprise access, bleeding breaches through reuse, phishing, and silent credential theft on unmanaged Windows PCs, and the lingering dependence on text secrets has turned shared and personal devices into

A phone call, a single sign-on prompt, a sprawling SaaS estate—then millions of customer records at risk, and the speed of that pivot from routine to crisis now defines the playbook for modern data theft in cloud-first businesses. Identity became the control plane; centralized SSO wired into

Lead Boardrooms celebrated lower exploit volumes only to learn that the quietest emails were opening the biggest doors across their networks. The surprise was not the return of phishing but its precision: polished messages in perfect prose, tailored to a role or project, arriving from services
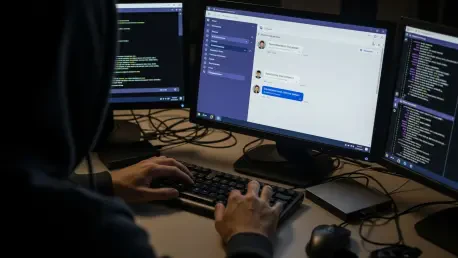
Corporate security perimeters are being bypassed by sophisticated threat actors who exploit the inherent trust users place in internal collaboration platforms like Microsoft Teams to execute social engineering schemes. This emerging trend involves hackers posing as technical support personnel to