
Today we’re speaking with Rupert Marais, our in-house security specialist, about a recent and particularly insidious cyberattack. A state-sponsored group known as Lotus Blossom is believed to have hijacked the update mechanism of the widely-used text editor, Notepad++, to deploy a sophisticated new

The widespread migration to multi-cloud environments has created a significant paradox for modern enterprises, as the immense potential of cloud computing and AI is often curtailed by persistent and deep-seated security fears. This apprehension is particularly acute in highly regulated sectors such

Microsoft is fundamentally reshaping its ubiquitous operating system with a series of aggressive security updates that prioritize modern threat protection, a strategic pivot that is causing significant disruption for older systems and established enterprise environments. This bold initiative marks

A digital screen on a public bus flashes an arcane error message instead of its usual advertisements, a small disruption that technology experts and urban observers agree offers a surprisingly deep insight into the complex systems governing modern life. This single event, a screen displaying a

With us today is Rupert Marais, our in-house security specialist whose expertise in endpoint security and network management gives him a frontline view of the challenges facing corporate IT. We'll be delving into the increasingly chaotic world of Microsoft's patching cycle, exploring the real-world
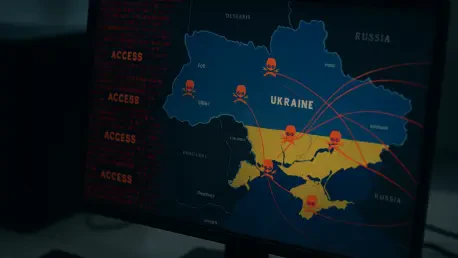
The digital battlefield has once again intensified as a notorious state-sponsored hacking group demonstrated alarming agility by turning a newly disclosed software flaw into a weapon against high-value government targets in less than twenty-four hours. This rapid exploitation marks a significant