The coordinated dismantling of the Tycoon 2FA infrastructure has fundamentally altered the global threat landscape, proving that digital criminal networks are often more resilient than the laws designed to contain them. While the seizure of over three hundred domains was a victory for international law enforcement, it inadvertently triggered a massive migration of threat actors toward more sophisticated, decentralized methods of account takeover. This transition marks the end of an era dominated by a single provider and the beginning of a fragmented, highly adaptive market where automation and OAuth exploitation define the new standard of cybercrime.
The Architecture of Modern Cybercrime and the Phishing-as-a-Service Dominance
The industrialization of credential theft has transformed from a cottage industry into a streamlined corporate model known as Phishing-as-a-Service. This ecosystem allows even low-level threat actors to deploy advanced technical attacks by renting ready-made infrastructure. These platforms provide everything from deceptive landing pages to automated data exfiltration modules, lowering the barrier to entry for global cybercrime. By centralizing the technical burden, providers ensure that their clients can focus entirely on social engineering and victim acquisition.
At the height of its influence, Tycoon 2FA served as the primary engine for this automated theft, defining the Multi-Factor Authentication bypass era. The platform specialized in Adversary-in-the-Middle technology, which functions by inserting a malicious proxy between a victim and a legitimate service. This allows attackers to capture not just passwords, but also live session cookies in real time. Because these cookies represent an already authenticated state, their theft renders traditional secondary security measures like SMS codes or push notifications completely ineffective.
The global impact of this technology was quantified when a multi-national enforcement operation seized 330 domains associated with Tycoon’s backend. While this collaborative effort successfully disrupted the primary workflow of thousands of affiliates, the modular nature of the software meant that the underlying code survived. The seizure provided a brief reprieve, but it also forced a technical evolution within the underground market as developers scrambled to insulate their new projects from similar centralized failures.
Market Redistribution and the Evolution of Adversarial Tactics
The Great Migration: How Competitors Absorbed the Tycoon Power Vacuum
The sudden collapse of a market leader rarely results in a permanent reduction of crime; instead, it triggers a rapid redistribution of resources. In the immediate aftermath of the Tycoon takedown, rival platforms like Mamba 2FA experienced a staggering 100% increase in attack volume. These competitors were positioned to absorb the displaced workforce, offering similar Adversary-in-the-Middle capabilities with improved evasion techniques. This “Hydra effect” demonstrates that as long as the demand for stolen credentials remains high, the infrastructure will simply reform under new branding.
Infrastructure resilience has become the primary selling point for alternative platforms such as EvilProxy and Sneaky 2FA. These services have integrated specialized technical artifacts and obfuscation methods that were previously unique to the Tycoon ecosystem. This code cross-pollination suggests that developers are sharing or selling modular components on dark web forums, leading to a homogenization of high-end phishing kits. Consequently, the tools used by small-scale actors today are frequently just as sophisticated as those once reserved for state-sponsored entities.
Statistical Trajectories and the Surge in OAuth-Based Exploitation
Quantifying the shift reveals a transition from a monolithic threat to a fragmented, multi-provider landscape. Prior to law enforcement intervention, the market saw approximately 9 million monthly attacks channeled through a few dominant kits. Current data indicates that while the total volume briefly dipped, it has rebounded into a more diverse array of smaller, harder-to-track campaigns. This fragmentation complicates the defensive task for security teams, as they must now defend against dozens of varying technical signatures rather than focusing on a single, well-known adversary.
Data-driven trends suggest that the traditional password is nearing its functional end as a security barrier. The evolution of credential theft is moving toward persistent account access through the exploitation of session tokens and OAuth permissions. Forecasting models indicate that as organizations implement more robust identity controls, threat actors will focus on stealing the “keys to the kingdom”—the long-lived tokens that allow them to remain logged in for weeks without re-authentication. This shift necessitates a complete overhaul of how identity is managed across enterprise environments.
Technical Barriers and the Complexity of Thwarting Decentralized Networks
Disrupting modular cybercrime infrastructure presents significant challenges because the components are often hosted across disparate, non-extradition jurisdictions. When a primary domain is seized, automated scripts can migrate the entire operation to a pre-configured backup server within minutes. This level of automation makes it nearly impossible for traditional legal frameworks to keep pace with the operational speed of modern phishers. The decentralized nature of these networks ensures that there is no single point of failure that can be targeted to end the threat permanently.
Detecting advanced evasion remains a primary hurdle for automated security software. Modern kits are designed to identify and block traffic originating from known security vendor IP ranges or virtual environments used for sandbox analysis. Furthermore, the integration of Tycoon-origin code into new, unidentified kits allows threat actors to hide their activities within a sea of seemingly unrelated traffic. Identifying these shared technical DNA markers requires deep forensic analysis that many smaller organizations simply cannot perform in real time.
Navigating the Regulatory Landscape and New Authentication Standards
Global compliance trends are currently adapting to the reality that traditional Multi-Factor Authentication is no longer a silver bullet. New security policies are beginning to mandate the use of phishing-resistant protocols to mitigate the risks inherent in the Phishing-as-a-Service model. Organizations that fail to adapt their authentication standards face not only increased risk of breach but also potential legal liabilities under emerging data protection laws. The push for FIDO2 and hardware-based security keys is gaining momentum as the only viable defense against sophisticated proxy-based attacks.
International takedowns provide a legal framework for domain seizure, but they often struggle to result in long-term prosecutions of the individuals behind the screens. Balancing the immediate need for disruption with the slow process of building a criminal case requires extensive cross-border cooperation. As these legal strategies evolve, the focus is shifting toward targeting the financial channels that allow Phishing-as-a-Service providers to monetize their platforms. By cutting off the flow of cryptocurrency, authorities hope to make the business model less sustainable for developers.
The Future of Account Takeover: Toward Device Code Phishing and EvilTokens
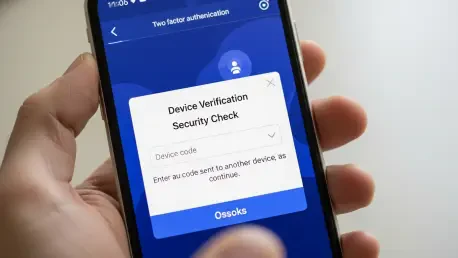
The emergence of EvilTokens represents the next stage in the evolution of identity exploitation. Device code phishing exploits legitimate authentication flows intended for smart TVs and other headless devices that lack a traditional browser. By tricking a user into entering a code on a legitimate verification page, the attacker can authorize their own malicious device to access the victim’s account. This method bypasses the entire password and Multi-Factor Authentication process by leveraging the inherent trust users have in official service portals.
Social engineering tactics have transitioned rapidly from simple email lures to complex, multi-stage interactions. Modern campaigns often use high-quality PDF lures that appear to be legitimate business documents but contain hidden triggers for OAuth authorization. This evolution exploits human-centric vulnerabilities, as even security-conscious users may feel safe interacting with a legitimate login page. The intersection of AI-driven content generation and these sophisticated technical flows has made it increasingly difficult for employees to distinguish between a valid request and a malicious intrusion.
Strategic Synthesis and Defensive Recommendations for a Fragmented Threat Landscape
The post-Tycoon era demonstrated that large-scale infrastructure disruption served as a catalyst for innovation rather than a total solution. Security researchers observed that while the dominant player was neutralized, the underlying demand for access drove a shift toward more resilient and diverse attack vectors. Organizations realized that relying on a single layer of protection was insufficient when facing an adversary that could pivot from session theft to device code exploitation in a matter of weeks.
Closing the security gap required a transition to phishing-resistant protocols that did not depend on the user’s ability to identify a fraudulent site. Investment priorities shifted toward focused detection and response strategies that prioritized the monitoring of session behavior and anomalous token usage. Defensive teams recognized that the battle had moved beyond the login screen and into the continuous validation of identity throughout the life of a session. These proactive measures represented the only effective way to counter the emerging wave of identity-centric attacks.