

The sudden emergence of a critical vulnerability within the cPanel administrative interface has sent shockwaves through the global hosting ecosystem, exposing thousands of servers to unauthorized control. This authentication bypass, identified as CVE-2026-41940, represents a pivotal shift in the
Assessing the Security Crisis of End-of-Life Networking Hardware The security of home and small business networks often hinges on a single point of failure, but recent investigations into legacy TP-Link hardware have revealed a troubling surge in cyberattack attempts targeting high-severity
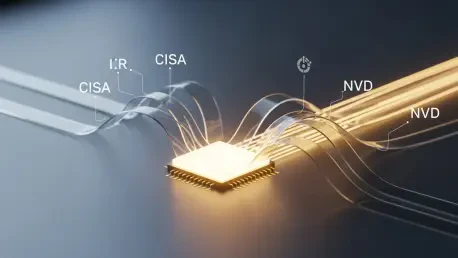
Modern cybersecurity operations centers are currently grappling with an unprecedented surge in vulnerability reports that often leave analysts paralyzed by a constant stream of low-priority alerts. This chronic inefficiency stems from a fragmented intelligence landscape where professionals must

The modern landscape of national security is no longer defined by the visible deployment of hardware but by the silent, rhythmic pulse of malicious code embedded within the very systems that sustain civilian life. As societies lean more heavily on digital interconnectivity, the primary battleground

Rupert Marais is a leading voice in the cybersecurity landscape, specializing in the intricate layers of endpoint security and the strategic defense of complex network architectures. With a career dedicated to staying ahead of emerging threats, Rupert brings a sharp, analytical perspective to the

The digital finance landscape is currently navigating a period of profound transformation where the convenience of instantaneous transactions is increasingly being undermined by a catastrophic wave of highly sophisticated cybercrime. As financial systems transition toward a borderless, always-on

A lab robot that obediently fetches parts could just as easily fetch the wrong ones—or ignore safety rails entirely—if an attacker can steer its brain from afar through a network message disguised as “policy data.” That unsettling scenario moved from theory to practice with CVE-2026-25874, a

Kendra Haines sat down with Rupert Marais, our in-house Security specialist renowned for endpoint and device security, cybersecurity strategies, and hardened network management under fire. With campaigns like UAT-4356’s ArcaneDoor in the news and Firestarter proving it can outlive reboots, firmware

Why Passwords Finally Lost Their Last Safe Harbor Passwords are still the soft underbelly of enterprise access, bleeding breaches through reuse, phishing, and silent credential theft on unmanaged Windows PCs, and the lingering dependence on text secrets has turned shared and personal devices into
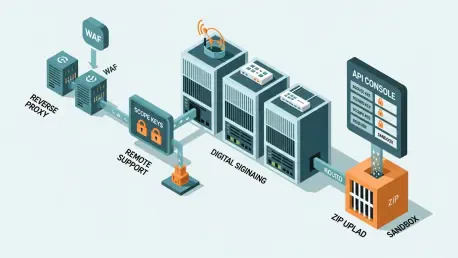
Rupert Marais has spent years hardening endpoints, corralling unruly networks, and steering incident response through late‑night crises. In this conversation, he unpacks how four newly exploited flaws across SimpleHelp, Samsung MagicINFO 9 Server, and D-Link DIR-823X bend patching priorities, force
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy