
The familiar hum of an ATM dispensing cash has been subverted by a new breed of silent, digital heist that requires no stolen card, only malicious code specifically designed to hijack the machine’s core functions. ATM jackpotting malware represents a significant evolution in financial cybercrime,

The seemingly harmless search for a free software license or a helpful video tutorial is increasingly becoming the digital tripwire that unleashes sophisticated cyberattacks into unsuspecting networks. In a landscape where threat actors continuously refine their methods, recent investigations have

Today we’re joined by Rupert Marais, our in-house security specialist whose expertise in endpoint security and network management gives him a unique perspective on the evolving threat landscape. We'll be diving into two recent, yet starkly different, campaigns that targeted Cisco network
A security vulnerability from years past, long considered patched and resolved, has suddenly reappeared on the federal government’s list of urgent cyber threats, leaving system administrators and home users alike to question the stability of their defenses. The U.S. Cybersecurity and Infrastructure
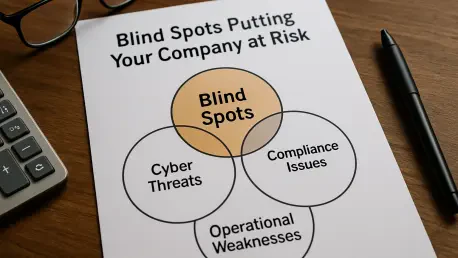
A security operations center attempting to defend a modern enterprise with only historical data is akin to a driver trying to navigate a high-speed collision course by looking exclusively in the rearview mirror. This backward-facing posture, common in many organizations, creates dangerous blind

In the fast-paced world of cybersecurity, staying ahead of threats is a constant battle. This month’s security updates from Microsoft are a stark reminder of that reality, with patches for 56 flaws, including one being actively exploited and two publicly known zero-days. To help us decipher the