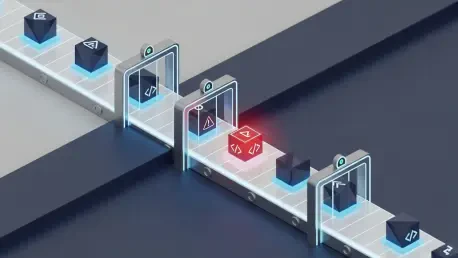
Modern software engineering relies on a fragile web of trust where a single automated update can silently compromise millions of enterprise systems within seconds of publication. The software supply chain represents a significant advancement in the global developer ecosystem, enabling rapid

The silent architecture of the Linux kernel has long relied on the inherent difficulty of timing-based attacks to maintain security, but the arrival of the Dirty Frag exploit completely dismantles this traditional defensive assumption. The discovery of Dirty Frag marks a departure from the finicky,

The pursuit of digital sovereignty through local artificial intelligence has inadvertently created a sprawling playground for sophisticated cyberattacks, exposing the very secrets that users intended to protect from the public cloud. As organizations shift toward local large language model (LLM)

The Growing Vulnerability of the Defenders: Contextualizing the Trellix Intrusion The sudden breach of a titan like Trellix reminds us that even the most fortified digital fortresses remain susceptible to the persistent ingenuity of modern threat actors. This intrusion strikes a profound chord of

The rapid discovery of targeted exploitations against enterprise infrastructure often forces cybersecurity teams into a high-stakes race where the margin for error is virtually nonexistent. Ivanti recently issued an urgent security warning regarding a high-severity vulnerability, designated as

The delicate balance between allowing users to execute custom scripts and maintaining the impenetrable integrity of a host server has never felt more precarious than it does in today’s interconnected cloud environment. Within the Node.js ecosystem, the vm2 library was once heralded as the