Modern software engineering relies on a fragile web of trust where a single automated update can silently compromise millions of enterprise systems within seconds of publication. The software supply chain represents a significant advancement in the global developer ecosystem, enabling rapid deployment through automated pipelines and shared package repositories. This review explores the evolution of the technology, its key features, performance metrics, and the impact it has had on various applications, specifically focusing on the recent “Mini Shai-Hulud” campaign. The purpose of this review is to provide a thorough understanding of the technology, its current capabilities, and its potential future development in the face of increasingly sophisticated security breaches.
Introduction to Software Supply Chain Infrastructure
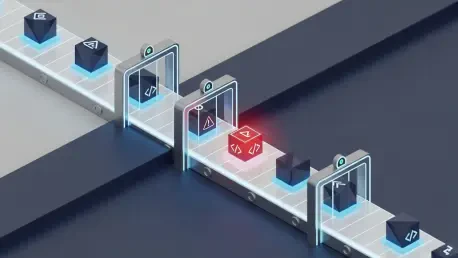
The backbone of modern development is built upon automated CI/CD pipelines and central package managers like npm and PyPI. These systems allow developers to integrate complex functionalities by importing pre-built modules, essentially creating a massive, interconnected web of trusted code. This infrastructure is governed by the principle of efficient distribution, where a single developer’s contribution can be propagated to millions of machines almost instantaneously.
This relevance is magnified in the broader technological landscape, where millions of weekly downloads drive modern enterprise software development and cloud-native architectures. As companies shift toward microservices and serverless functions, the reliance on third-party dependencies becomes absolute. However, this same efficiency creates a systemic vulnerability where the compromise of a single repository can trigger a cascading failure across the global digital economy.
Technical Mechanisms of the Mini Shai-Hulud Breach
Pipeline Hijacking: The OIDC Token Extraction
The “Pwn Request” pattern represents a sophisticated evolution in repository exploitation, moving away from simple credential theft toward architectural manipulation. By leveraging the pull_request_target workflow in GitHub Actions, attackers were able to execute malicious code within a privileged context. This specific workflow is designed to facilitate contributions from forks, but if misconfigured, it provides a bridge for unauthorized code to interact with internal secrets.
Furthermore, the campaign utilized GitHub Actions cache poisoning to ensure the persistence of their malicious scripts across different runner sessions. This allowed for the extraction of OpenID Connect (OIDC) tokens directly from the runner memory. Because these tokens represent short-lived, identity-based credentials, they bypassed traditional static secret scanning, granting the attackers the ability to impersonate the legitimate build process and gain authorized access to cloud resources.
Attestation Integrity: The SLSA Framework Performance
The most alarming aspect of this breach was the subversion of the SLSA Build Level 3 provenance framework. Traditionally, this standard serves as a guarantee that an artifact was built in a secure, verifiable environment and has not been tampered with since its creation. However, the Mini Shai-Hulud campaign proved that even a legitimate build pipeline can produce malicious artifacts if the input or the build environment itself is hijacked.
This highlights a critical performance gap in current signature verification methods. When the build server itself is compromised, the resulting signature is technically valid and trusted by security tools. Consequently, organizations relying solely on provenance attestations were left vulnerable, as their systems accepted the signed malware as authentic, authorized code, exposing the limitations of static integrity checks in dynamic attack scenarios.
Emerging Trends in Automated Threat Patterns
A significant shift is occurring toward “living off the pipeline” attacks, where adversaries no longer need to maintain their own infrastructure. Instead, they use the victim’s own CI/CD tools to compile malware, sign it, and distribute it. This trend minimizes the attacker’s footprint and makes detection nearly impossible for legacy antivirus solutions that prioritize scanning for known external signatures rather than internal pipeline anomalies.
Moreover, the use of dead drops via legitimate APIs has become a preferred method for bypassing network egress filtering. By using the GitHub API or the Session messenger network to transmit stolen data, attackers hide their traffic within the noise of standard developer activity. This tactic ensures that data exfiltration remains undetected by traditional firewalls, as the destination appears to be a trusted, everyday service used by the development team.
Real-World Applications and Sector Impact
The real-world applications of these affected technologies span across various high-stakes industries, including finance, healthcare, and artificial intelligence research. Popular frameworks like TanStack are fundamental to the user interfaces of modern web applications, while Mistral AI and OpenSearch power the backend of data-intensive enterprise tools. A compromise at this level means that the very tools used to manage and search sensitive data are turned against the user.
Notable implementations in AI artifacts and React components have demonstrated how easily a hijacked package can lead to large-scale data exfiltration. If a compromised version of a routing library is integrated into a banking application, every user interaction and credential entered could be harvested. This systemic risk is not theoretical; it represents a direct threat to the integrity of enterprise-level tools that handle trillions of dollars in transactions and massive volumes of proprietary data.
Challenges in Securing Modern Release Workflows
One of the primary challenges in securing these workflows is the sheer difficulty of detecting heavily obfuscated payloads within massive codebases. The Mini Shai-Hulud malware utilized a 2.3MB payload that was designed to stay dormant or hidden among thousands of lines of legitimate dependency code. Detecting such sophisticated intrusions requires more than just static analysis; it necessitates deep, behavior-based runtime monitoring that can identify unusual file system or network activity.
Furthermore, the limitations of static provenance attestations mean that security cannot be a one-time check during the build phase. Current development efforts are moving toward more restrictive GitHub Action permissions and mandatory credential rotation, but these measures often introduce friction into the developer experience. Balancing the need for rapid delivery with the necessity of rigorous, ongoing security checks remains the most significant technical hurdle for the industry.
Future Outlook for Supply Chain Resilience
The industry is clearly heading toward a transition to zero-trust build environments, where no component is trusted by default, regardless of its origin or signature. This will likely involve the implementation of ephemeral build runners that are destroyed after every task, alongside mandatory hardware-based security keys for all pipeline modifications. Such a shift would significantly increase the cost and complexity for attackers attempting to gain a persistent foothold.
Future developments will likely focus on breakthroughs in automated anomaly detection powered by specialized machine learning models that monitor pipeline behavior in real time. While mandatory credential rotation policies may initially impact developer productivity, their long-term effect will be a more resilient ecosystem. As these technologies mature, the goal is to create a self-healing supply chain where unauthorized changes are automatically flagged and reverted before they reach production.
Summary of Findings and Industry Assessment
The findings from the review underscored the critical vulnerabilities inherent in the automated global developer ecosystem. The TeamPCP campaign demonstrated that even highly regarded frameworks and security standards like SLSA could be bypassed through creative pipeline hijacking. This incident confirmed that the current reliance on static trust models was insufficient for defending against adversaries who operated from within authorized environments.
The overall assessment of the technology suggested that while CI/CD pipelines remained essential for modern software delivery, their security architecture required a fundamental redesign. The industry moved toward adopting runtime monitoring and zero-trust principles to mitigate the risks exposed by these sophisticated attacks. Ultimately, the breach served as a catalyst for a new era of supply chain resilience, forcing organizations to prioritize integrity over pure deployment speed.