While the flicker of a computer screen often signifies progress and connectivity, it now hides a silent, sophisticated heist that is currently siphoning the world’s most protected digital secrets into the hands of patient adversaries. This phenomenon is not marked by the loud sirens of a ransomware attack or the immediate chaos of a system shutdown. Instead, it is a quiet accumulation of encrypted data packets, gathered from secure servers and stored in vast, offshore repositories. The goal of these actors is not to break the encryption today, but to wait for the inevitable arrival of powerful quantum computers that will peel back current security layers like paper.
This strategic approach, known as the harvest-now, decrypt-later tactic, has transformed the cybersecurity landscape into a ticking clock. Even though the information remains unreadable for the moment, its theft represents a finalized breach with a delayed fuse. For organizations handling sensitive intellectual property or long-term state secrets, the realization that their current defenses are essentially providing a “time-capsule” for future exploitation is a jarring wake-up call. The security of the present is being undermined by the mathematical inevitability of the future, making the transition to quantum-resistant standards an immediate necessity rather than a distant goal.
The Invisible Threat: Harvest-Now, Decrypt-Later Attacks
Modern data centers are currently facing a threat that thrives on patience rather than immediate penetration. Cybercriminals and state-sponsored actors are actively intercepting encrypted communications, from financial records to proprietary research, with the intent of archiving this data for future use. Because they recognize that quantum computing will eventually render today’s most robust encryption algorithms obsolete, they are treating every bit of encrypted data as a valuable asset for the coming decade. This silent heist means that data stolen today will be fully readable the moment a cryptographically relevant quantum computer is switched on.
The danger of this archival strategy lies in the false sense of security it provides to modern enterprises. Since no immediate damage is detected, many organizations remain unaware that their most sensitive assets have already left their control. However, the value of certain data, such as national security intelligence or long-term pharmaceutical formulas, does not diminish over time. Consequently, the breach is already complete; the only missing component is the computational power required to view the stolen contents. This reality shifts the defensive focus from preventing current access to ensuring that data remains unreadable even in a post-quantum environment.
The Quantum Countdown: Erosion of Traditional Security
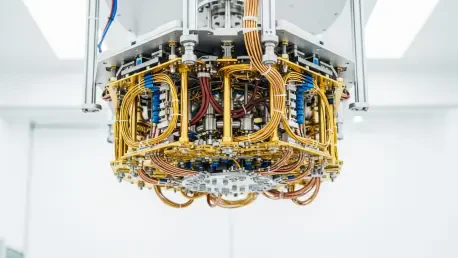
The shift from classical to quantum computing represents a fundamental change in how information is processed, making traditional RSA and Elliptic Curve Cryptography (ECC) essentially useless. Classical computers rely on the difficulty of factoring massive numbers, a process that would take trillions of years for current hardware to solve. Quantum computers, however, utilize Shor’s algorithm to bypass these mathematical hurdles in mere minutes. As the threshold of quantum utility draws closer, the window for protecting long-term data is closing, leaving organizations with a narrow timeframe to overhaul their entire cryptographic infrastructure.
For many enterprises, the shelf life of their most valuable data already exceeds the estimated time remaining before quantum supremacy becomes a tool for malicious actors. Information such as lifetime medical records, architectural blueprints, and trade secrets must remain confidential for thirty to fifty years. If a quantum computer capable of breaking current encryption arrives within the next decade, any data protected by today’s standards will be exposed long before its sensitivity expires. Therefore, the countdown toward quantum capability is not just a technological race but a fight to preserve the integrity of the global digital economy.
Assessing Data Longevity: Identifying Systemic Vulnerabilities
To mount an effective defense, organizations must begin by categorizing their information based on its secrecy lifespan and current level of exposure. Not all data requires the same level of protection; a one-time password used for a single transaction has a secrecy lifespan of seconds, whereas merger and acquisition plans might remain sensitive for years. Conducting a comprehensive audit allows security teams to map out where high-value assets reside and which legacy systems are most vulnerable to future decryption. This systematic review is the first step in moving toward a posture that prioritizes the most at-risk information.
Identifying “crypto-dependencies” across different departments is also essential to ensure that no part of the supply chain remains an open door. Many organizations rely on third-party software and hardware that may not yet support post-quantum standards, creating weak links in an otherwise secure network. Furthermore, evaluating the computational demands of quantum-resistant algorithms is necessary, as these new protocols often require significantly more processing power and larger key sizes. Understanding these technical requirements early prevents performance bottlenecks and ensures that the transition to new standards does not disrupt essential business operations.
The Reality of Global Unpreparedness: High Stakes of Inaction
Despite the clear warnings from the scientific and intelligence communities, a significant gap remains between the perceived threat and actual organizational readiness. Current industry data suggests that only 14% of enterprises have an IT infrastructure capable of supporting post-quantum cryptography today. Even more concerning is the fact that nearly half of all organizations surveyed have taken no defensive action at all, likely under the mistaken belief that the threat is too far in the future to warrant current budget allocations. This widespread inertia creates a target-rich environment for those currently harvesting data.
Expert consensus, including guidance from leaders at Unisys, indicates that waiting for a “perfect” solution is a dangerous gamble. Those who fail to begin the migration process now will eventually be forced into a chaotic, crisis-mode transition that is both expensive and prone to error. A rushed migration often leads to misconfigurations, system outages, and overlooked vulnerabilities, all of which could be avoided through a gradual and planned implementation. The high stakes of inaction involve not only the loss of intellectual property but also the potential for catastrophic legal liabilities and a total erosion of public trust.
A Strategic Framework: Implementing Quantum-Resistant Protocols
Securing the digital future requires a phased and agile approach to cryptographic migration that balances security with operational stability. Organizations should start by launching controlled pilot programs using algorithms currently being standardized by the National Institute of Standards and Technology (NIST). By testing these quantum-resistant protocols in non-critical environments, IT teams can monitor performance and identify any integration issues without risking the primary business functions. These pilots provide the necessary data to scale the protection across the entire enterprise more effectively.
Deploying hybrid encryption models serves as a critical safety net during the transition period. These models layer classical encryption with post-quantum protections, ensuring that even if one layer is compromised, the data remains shielded by the other. Moreover, establishing a culture of “crypto-agility” is vital for long-term resilience. This means designing systems that allow for the rapid replacement of cryptographic primitives as new vulnerabilities are discovered or as quantum threats evolve. By building this flexibility into the core architecture, organizations ensured that they were never tied to a single, potentially breakable standard.
The path toward a quantum-resistant future necessitated a fundamental shift in how organizations viewed their digital legacy. Security leaders recognized that the migration was not a single event but a continuous process of adaptation and vigilance. They prioritized the identification of long-term assets and implemented hybrid protections to mitigate the risks of silent data harvesting. By adopting NIST-approved standards and fostering crypto-agility, these organizations protected their reputations and their most sensitive information. Ultimately, the move toward post-quantum cryptography proved to be the most significant defensive evolution of the decade, safeguarding the global economy against the looming quantum shadow.