Modern cyber warfare has moved beyond the confines of suspicious emails and entered the intimate space of our daily conversations, turning trusted messaging notifications into silent harbingers of digital compromise. As employees increasingly blend professional and personal communication on their desktop devices, threat actors have found a fertile hunting ground within the Windows versions of mobile-first applications. This shift represents a fundamental change in the threat landscape, where the primary entry point is no longer a corporate firewall but a social engineering lure delivered through a platform billions of people use for casual chat.
Analyzing the Mechanics of Sophisticated Social Engineering on Messaging Platforms
The transition toward utilizing personal messaging applications as primary vectors for enterprise-level intrusions highlights a significant evolution in attacker psychology. By moving away from traditional email, which is often heavily scrutinized by automated filters, attackers exploit the inherent trust users place in their instant messaging contacts. This approach bypasses several layers of perimeter defense, as many organizations do not apply the same level of inspection to encrypted messaging traffic that they do to standard web or email protocols.
Moreover, identifying these intrusions is complicated by the adoption of “living off the land” (LotL) tactics. Instead of deploying custom, easily identifiable malware, these campaigns repurpose legitimate Windows system utilities to perform malicious actions. This methodology allows threat actors to hide in plain sight, as the tools they utilize are the same ones used by system administrators for routine maintenance. The challenge for security teams lies in distinguishing between a legitimate administrative task and a disguised attempt to hijack system resources.
The Escalation of Messaging-Based Intrusions and System Vulnerability
In the current landscape, researchers have documented a multi-stage campaign that weaponizes WhatsApp to deliver malicious Visual Basic Scripts (VBS) directly to Windows environments. These scripts serve as the initial infection point, designed to run quietly in the background without alerting the user. The significance of this research lies in its exposure of how threat actors are successfully exploiting the gap between mobile security expectations and the robust architecture of desktop operating systems.
The danger of this campaign is amplified by the use of trusted cloud infrastructure. By hosting secondary payloads on reputable services, attackers ensure that the connection between the victim’s computer and the malicious source looks entirely legitimate to network monitoring tools. This strategy effectively erodes the concept of a secure perimeter, as security protocols often default to trusting traffic originating from major cloud providers, creating a blind spot that allows the intrusion to escalate into a full-scale compromise.
Research Methodology, Findings, and Implications
Methodology: Deconstructing the Attack Chain
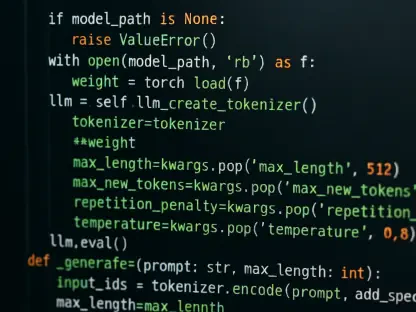
The investigation into this malware involved a comprehensive behavioral analysis of VBS files and the subsequent creation of hidden directories within sensitive system folders like C:\ProgramData. By monitoring the execution flow, researchers were able to observe the malware’s attempts to establish a permanent presence on the host machine. This process revealed a sophisticated sequence of events where the initial script acts as a scout, preparing the environment for more destructive payloads.
Furthermore, the study tracked the misuse of standard Windows binaries such as curl.exe and bitsadmin.exe. These tools, normally used for file transfers and system updates, were intercepted to fetch malicious data streams from external servers. By correlating network traffic with specific process calls, the research team identified how reputable cloud services were being co-opted to deliver the next phase of the attack, making the malicious activity indistinguishable from routine software updates at a glance.
Findings: Techniques of Deception and Evasion
One of the most striking findings of this research was the detection of file-masking techniques where legitimate tools were renamed to appear as system libraries, such as netapi.dll. This simple yet effective tactic is designed to evade signature-based detection systems that primarily look for known malicious file names. However, the researchers discovered a critical flaw in this approach: the metadata within the files, specifically the OriginalFileName attribute, did not match the external label, providing a clear signal of infection for metadata-aware security tools.
The campaign also utilized unsigned Microsoft Installer (MSI) packages to complete the infection process. These packages were cleverly disguised as popular productivity software like WinRAR or remote support tools like AnyDesk. By tricking users into installing these “updates,” the attackers gained a reliable method for remote management and persistent access. The discovery of these unsigned packages highlighted a persistent vulnerability in how Windows handles installer files that lack a verified digital certificate from the developer.
Implications: The Erosion of the Trusted Perimeter
The implications of these findings are severe, as they point toward an increased risk of full system compromise and unauthorized data exfiltration. When attackers successfully deploy remote management tools under the guise of legitimate software, they gain the ability to monitor user activity, steal credentials, and spread laterally through an organization’s network. This level of access essentially grants the threat actor the same privileges as a local administrator, making it incredibly difficult to remove the infection once it has taken hold.
Additionally, the success of these campaigns marks a significant shift in the reliability of “trusted cloud” communications. As attackers successfully mask their traffic within enterprise service streams, the traditional reliance on IP reputation and domain whitelisting becomes less effective. Organizations must now face the reality that malicious traffic can originate from the very same servers they use for their legitimate business operations, necessitating a move toward more granular and behavior-based monitoring protocols.
Reflection and Future Directions
Reflection: The Effectiveness of Current Defenses
Reflecting on the current state of cybersecurity reveals a troubling gap between the speed of social engineering evolution and the implementation of technical safeguards. Current defensive perimeters are often ill-equipped to handle unsigned payloads that utilize disguised binaries, as these threats do not trigger traditional alarm bells. The balance between user convenience and security remains precarious, especially when users are conditioned to accept attachments and updates as part of their daily workflow without question.
The difficulty in detecting these activities stems from how perfectly they mimic routine system administration tasks. When a malicious script uses a standard Windows tool to download a file, it generates logs that look identical to those of a legitimate software update. This mimicry forces defenders to look beyond the surface of the activity and analyze the intent and context of every process, a task that is increasingly difficult in complex, high-traffic corporate environments.
Future Directions: Advancing Behavioral and Privacy Protocols
To stay ahead of these evolving threats, the focus must shift toward AI-driven behavioral modeling that can flag anomalous uses of renamed tools in real-time. By training systems to recognize the specific patterns of metadata discrepancies and unusual binary calls, organizations can automate the detection of “living off the land” tactics before the final payload is delivered. This proactive approach would reduce the reliance on human intervention and provide a faster response to emerging campaigns.
Additionally, there is a clear path forward in enhancing the privacy and security features of messaging platforms themselves. Features such as stricter account settings and the disabling of link previews for unrecognized contacts can significantly reduce the success rate of initial social engineering attempts. Moving forward, a cross-platform security strategy will be essential, ensuring that the protection of a Windows PC is not undermined by the inherent openness of the messaging applications that residents use to bridge their personal and professional lives.
Strengthening Windows Defenses Against Modern Malware Campaigns
The investigation into the WhatsApp-based malware campaign illustrated a complex, multi-stage progression that began with a simple script and ended with total system control. By utilizing renamed binaries and trusted cloud hosts, the attackers successfully bypassed traditional detection methods, highlighting a critical need for metadata-focused defense strategies. The technical indicators of compromise identified during the research provided a roadmap for IT administrators to better secure their environments against similar intrusions in the coming years.
Ultimately, the study showed that technical filtering alone is no longer sufficient; comprehensive user education must be integrated into the security posture of every modern organization. The research concluded that a proactive approach, combining stricter monitoring of system binaries with enhanced messaging privacy settings, offered the most effective defense. By addressing both the technical vulnerabilities of the Windows operating system and the psychological vulnerabilities of its users, organizations could better navigate the complexities of the modern digital threat landscape.