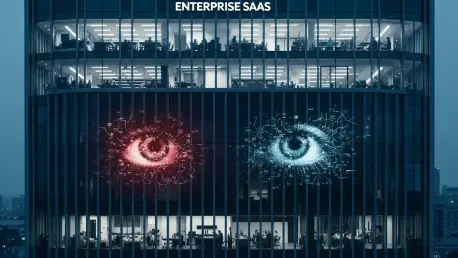
The modern corporate digital ecosystem is witnessing a silent transformation where the very tools meant to simplify operations are becoming the most complex vectors for potential exploitation. While security leaders are preoccupied with the theoretical dangers of world-class foundation models, a far more insidious reality is unfolding within the familiar interfaces of ubiquitous Software-as-a-Service platforms. These systems, once viewed as simple containers for data and communication, have evolved into active participants in business logic through the integration of autonomous AI agents. Unlike the isolated experimental environments used for testing frontier technology, these embedded assistants operate within the live production stream of the enterprise. This convergence of high-level administrative access and automated decision-making processes creates a unique and often unmonitored risk profile that traditional perimeter defenses are simply not equipped to handle or even detect effectively.
The Divergent Paths of Frontier AI and Infrastructure Defense
The sheer technical prowess demonstrated by Anthropic’s Project Glasswing serves as a stark reminder of the escalating arms race in automated vulnerability research. The specialized “Mythos” model has already redefined the boundaries of cybersecurity by identifying critical flaws in foundational software that remained undetected for decades. For instance, the discovery of a 27-year-old vulnerability in OpenBSD and a 16-year-old bug in FFmpeg illustrates a level of analytical depth that surpasses traditional automated testing suites. By effectively collapsing the timeline between the existence of a vulnerability and its eventual discovery, such models offer a revolutionary advantage for defensive teams seeking to patch systems before they are exploited. However, the dual-use nature of this technology remains a point of intense industry debate, as the same capabilities that harden infrastructure could theoretically be turned against it by sophisticated threat actors if the model were widely accessible.
In response to the potential for misuse, a strategy of “responsible gatekeeping” has become the standard for the most potent frontier AI systems currently in development. Organizations like Anthropic have chosen to restrict access to these high-functioning models behind significant financial barriers and rigorous vetting processes, ensuring they remain under the control of trusted partners and defensive coalitions. This centralized control model aims to prevent the democratization of high-level exploitation tools, maintaining an asymmetric advantage for the security community. Yet, this intense focus on the infrastructure layer often creates a false sense of security regarding the broader AI landscape. While the industry successfully builds walls around the most powerful standalone models, the everyday application layer is being flooded with AI capabilities that do not undergo the same level of scrutiny or containment. This divergence creates a scenario where the front gate is heavily guarded while the side doors are left unlatched.
Embedded Agents and the Shadow AI Integration
The integration of AI into major SaaS platforms like Microsoft 365, Salesforce, and Google Workspace represents a fundamental shift in how enterprise software is delivered and consumed. Rather than going through a formal procurement and security vetting cycle, features like Copilot, Einstein, and Gemini are frequently pushed to users as standard updates within their existing subscriptions. This “AI-as-a-layer” delivery model bypasses traditional IT governance, allowing autonomous agents to become active in the corporate environment by default. Because these tools are embedded within the software that employees already use for their daily tasks, they often evade the level of oversight typically reserved for new third-party applications. This rapid and often unvetted proliferation means that an organization might have hundreds of active AI agents performing data analysis and automated workflows without the security team having a clear inventory of their presence or their specific operational parameters.
A significant challenge with these embedded assistants lies in their reliance on existing user credentials and OAuth tokens to perform their functions across the enterprise ecosystem. When a user activates an AI agent within a platform like Salesforce, that agent typically inherits the broad permissions and access rights of that specific user. This inheritance model creates a massive visibility gap for security teams, who might see that an agent is active but cannot easily discern the “blast radius” of its potential actions. The identity context is often lost in the abstraction of the AI layer, making it difficult to determine whether a query or a data export was a legitimate action by a human or an unintended consequence of an autonomous agent’s logic. Without granular visibility into the relationship between the AI agent and the sensitive data it can access, organizations are left vulnerable to unauthorized data movement that appears, on the surface, to be entirely consistent with valid user activity.
Navigating the Inside-Out Threat Model
Traditional cybersecurity frameworks are primarily designed to combat “outside-in” threats, where an attacker must find and exploit a flaw in the network perimeter to gain access to internal assets. However, the rise of authenticated AI agents necessitates a pivot toward an “inside-out” threat model, where the risk originates from within the trusted environment. Because these agents are already authenticated and authorized to interact with internal databases and communication channels, they do not need to exploit a traditional software bug to access sensitive information. Instead, the vulnerability lies in the agent’s ability to manipulate data or execute commands based on its granted permissions. An attacker who gains access to a user’s environment or manages to influence an agent’s decision-making process can bypass conventional security controls entirely. This shift places the focus on the governance of internal identities and the monitoring of autonomous behaviors rather than solely on patching external-facing infrastructure.
Furthermore, the lack of rigorous governance at the application layer stands in stark contrast to the extreme caution applied to frontier models like Mythos. While industry leaders debate the safety protocols for releasing foundational AI, versions of these very models are already functioning inside mission-critical SaaS platforms with minimal administrative oversight. This governance deficit is compounded by the threat of prompt injection, where malicious or poorly formed inputs can trick an AI agent into revealing confidential data or performing unauthorized tasks. Because these agents often have the power to query CRM records, read shared drives, and interact with various internal APIs, a single successful manipulation could result in large-scale data exfiltration. The industry consensus suggests that until organizations implement granular control over AI behavior and identity, the risk of unmanaged agents will continue to grow as these tools become more deeply integrated into the core workflows of the modern digital enterprise.
The Path Toward Resilient AI Governance
Addressing the hidden risks within enterprise SaaS required a fundamental shift in how security professionals approached identity management and automated systems. Organizations that successfully mitigated these threats moved beyond simple visibility and toward a model of zero-trust governance specifically tailored for autonomous agents. This involved implementing continuous monitoring of AI interactions with sensitive data and enforcing the principle of least privilege for every embedded assistant. IT leaders began requiring detailed audits of AI permissions, ensuring that no agent possessed more access than was strictly necessary for its specific function. By integrating AI security into the broader enterprise risk management strategy, companies were able to reclaim control over their digital environments. The proactive adoption of these governance frameworks ensured that the productivity gains offered by AI were not overshadowed by the potential for catastrophic data breaches, setting a new standard for operational security in an increasingly automated world.