The sophisticated image of a hooded hacker typing furiously to exploit a deep software flaw has been replaced by a much more mundane reality: an intruder simply typing a valid username and password into a standard login portal. In this current landscape, the most dangerous weapon in a digital arsenal is no longer a complex piece of malware, but a legitimate set of employee credentials. This fundamental pivot marks a transition toward the “path of least resistance,” where the human identity has replaced the software vulnerability as the most sought-after entry point into corporate networks. Organizations are finding that while their expensive firewalls remain unbreached, their internal environments are being compromised by users who appear, at first glance, to be legitimate staff members.
This shift represents more than just a change in tactics; it signifies the total erosion of the traditional security perimeter. For decades, defensive strategies were built around “hardening the shell” of an organization, focusing on barriers like antivirus software and network gateways. However, the current reality of cloud computing, remote work, and deep third-party integrations has effectively dissolved these boundaries. Identity is now the only remaining perimeter. When a single set of compromised credentials can provide a “master key” to vast ecosystems of interconnected data and vendors, the stakes of identity management become existential. As organizations become more decentralized, the risk of “identity sprawl”—the proliferation of unmonitored service accounts and third-party access points—creates a massive, often invisible, surface for attackers to exploit.
The Login ErWhy Today’s Intruders No Longer Need to Break In
The evolution of cybercrime has reached a point where engineering a sophisticated zero-day exploit is often considered an inefficient use of resources. Attackers have realized that the human element is almost always the weakest link in the security chain, leading to a surge in social engineering and credential harvesting. By masquerading as a trusted colleague or service provider, an adversary can bypass layers of technical security that cost millions to implement. This approach allows them to operate in the shadows, using the very tools designed for productivity to facilitate their theft.
Internal networks are now frequently accessed by “ghost” users who navigate folders and databases with the same permissions as the employees they are impersonating. Because these actors are using valid credentials, traditional signature-based detection systems often fail to flag their presence. The challenge for modern defenders is no longer just keeping people out, but determining whether the person already “inside” is who they claim to be. This requires a transition from a gatekeeper mentality to one of constant, vigilant observation of behavioral patterns.
The Erosion of the Perimeter: Identity as the New Attack Surface
The historical concept of the network as a fortified castle is essentially dead, as the modern enterprise now functions more like a sprawling, open-air market. Every SaaS platform, every remote device, and every API connection represents a potential doorway that relies entirely on identity for protection. This decentralization has made the traditional firewall a secondary defense. If an attacker can secure a single identity, they can often pivot through integrated systems, moving from a marketing tool to a financial database without ever triggering a perimeter alarm.
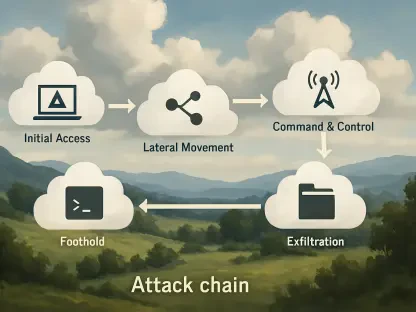
Furthermore, the rise of “identity sprawl” complicates the defensive landscape. Many organizations harbor hundreds of service accounts—automated profiles used for system-to-system communication—that are frequently overlooked during security audits. These accounts often possess high-level privileges and lack multi-factor authentication, making them prime targets for lateral movement. When identity is the new surface, every unmonitored account is a dormant vulnerability waiting to be discovered by a patient adversary.
The Industrialization of Theft: Dark Web Markets and the AI-Powered Force Multiplier
The modern threat landscape is no longer driven by solitary actors, but by a professionalized and collaborative criminal ecosystem. Initial access brokers now specialize in harvesting and validating credentials to sell to the highest bidder on Dark Web forums, allowing ransomware groups to bypass the difficult initial phases of an intrusion. This industrial supply chain is further accelerated by Artificial Intelligence, which has stripped away technical barriers for low-level criminals. AI now enables the creation of linguistically perfect phishing campaigns that lack the grammatical errors of the past.
Beyond simple phishing, AI-driven behavioral mimicry allows attackers to blend in with legitimate user traffic by imitating work hours and file access patterns. These tools can analyze how a specific employee interacts with a network and replicate those actions to avoid triggering anomaly alerts. This automation has turned credential theft into a high-volume, low-effort enterprise. For the price of a small subscription on the dark web, even an unskilled actor can launch a sophisticated campaign that once required a team of elite hackers.
Analyzing the Surge: Real-World Evidence of Identity-Based Exploitation
Recent research highlights a staggering 84% surge in information-stealing malware over the last year, a metric that underscores the high demand for valid login data. Expert analysis suggests that the battle is currently being lost because defenders remain siloed while attackers operate as a unified, professional enterprise. Case studies indicate that nation-state actors are increasingly purchasing access from common cybercrime brokers to mask their activities, complicating geopolitical attribution and response. The consensus among intelligence professionals is that the reliance on “binary” authentication is a critical failure point.
The data suggests that once an attacker secures a login, they stay within the network for an average of several weeks before being detected. During this time, they quietly exfiltrate data, map the network, and prepare for a final “loud” phase, such as a ransomware deployment. This delay in detection is a direct result of security teams focusing on external threats while ignoring the potential for internal actors to be compromised. The current intelligence points to a need for a radical shift in how trust is managed within the digital environment.
Hardening the Enterprise: A Practical Framework for Identity-Centric Security
To combat the rise of credential-based threats, organizations must move away from static security models and treat identity as a continuous, high-priority signal. This involves integrating dark web intelligence directly into security workflows to identify and rotate compromised credentials before they are used in an attack. Transitioning away from SMS and push notifications toward phish-resistant MFA, such as FIDO2-compliant hardware keys, is another essential step to prevent “adversary-in-the-middle” interceptions that bypass traditional second factors.
Furthermore, deploying continuous adaptive trust systems allows for the re-evaluation of user risk in real-time based on behavioral signals, such as “impossible travel” scenarios. It was equally vital to audit identity sprawl by regularly reviewing service accounts and enforcing the principle of least privilege. Hardening the IT help desk with mandatory video verification helped protect against AI-generated voice cloning. By treating every valid login with the same level of scrutiny as a malware detection, security teams successfully closed the gaps that threat actors previously exploited with devastating efficiency. These steps ensured that identity became a proactive shield rather than a passive vulnerability.