The traditional paradigm of digital defense is rapidly eroding as sophisticated adversaries abandon the pursuit of “impossible” breaches in favor of exploiting the subtle discrepancies between perceived and actual security. In the current landscape, the most effective weapons are not necessarily the most complex, but rather those that hide in plain sight within the tools and services that corporate users rely on for daily productivity. This shift signifies a fundamental change in attacker psychology, where the goal is no longer just to break the lock, but to inherit the key through the manipulation of “trust gaps.” These gaps exist in the overlooked corners of cloud configurations, abandoned digital assets, and the implicit permissions granted to browser extensions. As these vulnerabilities are increasingly paired with the velocity of artificial intelligence and the industrial scale of cloud-native botnets, the challenge for modern organizations has moved from preventing intrusion to managing a state of perpetual, high-speed conflict.
The Mechanics of Modern Exploitation
Growth Trends: Asset Hijacking and Rapid Vulnerability Cycles
Recent empirical data reveals a disturbing surge in the exploitation of abandoned digital assets, a trend that turns the legacy of the internet against its current users. Attackers have begun to systematically identify expired domains and neglected APIs that were once associated with legitimate software plugins or organizational subdomains. When these assets are allowed to lapse, they do not simply vanish; instead, they become “ghost infrastructure” that can be seized by threat actors to host malicious payloads or intercept data traffic. This method is particularly effective because the underlying software—often still installed on thousands of user machines—continues to attempt to communicate with these now-compromised endpoints. The result is a seamless transition from a trusted connection to a direct line for credential harvesting or malware delivery, often bypassing traditional perimeter defenses that recognize the original domain as a known-safe entity.
Furthermore, the window between the public disclosure of a vulnerability and its active exploitation has effectively vanished. Statistics from recent months show a drastic compression in the “scanning-to-exploitation” cycle, where critical flaws are leveraged in the wild within hours of a Proof of Concept being released. This phenomenon was notably observed with products from vendors like BeyondTrust, where automated global scanners identified unpatched instances across the internet almost instantaneously. The speed of this transition suggests that threat actors are now operating with a high degree of automation, utilizing cloud-scale infrastructure to perform reconnaissance at a pace that human-centric IT teams cannot hope to match. This rapid-fire exploitation model forces a re-evaluation of the standard patch management lifecycle, as the traditional 30-day window for remediation is now dangerously obsolete.
Real-World Applications: Trust Gap Weaponization
The practical application of these trends was starkly illustrated by the hijacking of the “AgreeTo” Outlook add-in, a tool distributed through the official Microsoft Store. This incident proved that even highly regulated marketplaces are not immune to the risks of abandoned infrastructure. Once the developers ceased maintenance and allowed their domain to expire, attackers moved in to reclaim the asset, transforming a helpful scheduling tool into a potent phishing engine. Because the add-in held extensive permissions to read and modify communications—privileges granted by users who trusted the Microsoft Store’s vetting process—the attackers were able to harvest over 4,000 corporate credentials without triggering typical security alerts. This case study serves as a foundational example of how trust is being leveraged as a vector, turning a user’s confidence in a brand into a vulnerability that provides deep, surreptitious access to sensitive environments.
At the same time, the broader ecosystem remains under siege from sophisticated memory manipulation attacks that target the core components of modern operating systems. High-profile zero-day responses from industry leaders like Google and Apple highlight the persistence of memory corruption and “use-after-free” bugs. These vulnerabilities, such as those found in the Chrome browser’s CSS engine or the macOS Dynamic Link Editor, allow attackers to execute arbitrary code with minimal user interaction. By targeting these low-level processes, adversaries can compromise a device before a user even realizes a malicious page has been loaded. These attacks are not merely academic; they are being actively utilized in targeted campaigns against high-value individuals and enterprises, demonstrating that the technical barrier for entry into a system remains a moving target that requires constant, low-level vigilance.
Cloud-native botnets like TeamPCP are further refining this trend by applying it to the very infrastructure that powers modern business. Rather than targeting individual workstations, these groups scan the global internet for misconfigured Docker APIs, Kubernetes clusters, and Redis servers. Their objective is to convert legitimate, high-performance computing resources into distributed launchpads for broader cybercrime activities. By gaining a foothold in these environments, they can deploy scripts that maintain persistent access and hide their activity within the noise of normal container orchestration. This transformation of legitimate infrastructure into a “cybercrime-as-a-service” platform allows for a scalable impact that was previously impossible, as a single compromised cluster can provide more raw power and anonymity than thousands of traditional infected PCs.
Industry Perspectives: The Evolving Threat Landscape
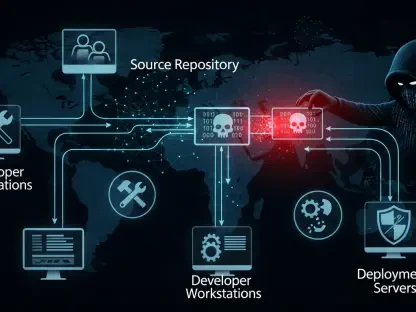
Supply Chain Risk: The Oversight of Small Plugins
Security researchers and practitioners are sounding the alarm that the definition of “supply chain risk” must be expanded to include the granular level of browser extensions and productivity plugins. These small tools often carry permissions that far exceed their stated functions, creating a massive, invisible attack surface within the enterprise. Because these tools are frequently developed by small teams or individuals who may lack the resources for long-term security maintenance, they represent a weak link in the defensive chain. Intelligence experts point out that the ease with which these assets can be hijacked or bought by malicious actors creates a marketplace for “pre-approved” access. The industry perspective is shifting toward a realization that a single, overlooked plugin can effectively nullify millions of dollars spent on firewalls and identity management systems.
Moreover, the strategic objective of nation-state actors has undergone a quiet but significant evolution. There is a discernible move away from simple, high-frequency data exfiltration toward a strategy of “strategic pre-positioning” within the Defense Industrial Base. In this context, contractor servers and edge devices are no longer just targets for theft; they are treated as the new physical front line. By establishing a dormant presence within these networks, state-sponsored groups ensure they have the capability to disrupt critical infrastructure or intercept sensitive communications during periods of future geopolitical instability. This shift suggests that the modern threat is no longer just about what an attacker takes today, but where they are positioned for tomorrow, necessitating a defense strategy that prioritizes long-term integrity over mere incident response.
The AI Integration: Code on Demand and Evasion Tactics
Thought leaders in the field of artificial intelligence safety are expressing growing concern over the “code-on-demand” model of malware development. This technique involves malware that uses LLM APIs to generate and execute benign-looking code snippets directly in system memory. Because the code is generated in real-time and never touches the disk in a recognizable form, it successfully bypasses traditional signature-based detection mechanisms that rely on identifying known malicious patterns. This approach effectively turns the power of generative AI into an obfuscation layer, allowing even relatively simple malware to behave in a polymorphic and highly evasive manner. The concern is that as AI models become more capable at understanding and writing code, the difficulty of distinguishing between legitimate administrative scripts and malicious AI-generated payloads will become nearly insurmountable for traditional security tools.
The professionalization of the “cartel” model among Ransomware-as-a-Service providers further complicates the landscape. Groups like DragonForce have demonstrated that cybercrime is now a highly organized, corporate-style endeavor, complete with affiliate programs, specialized “pentesters,” and sophisticated infrastructure for negotiating ransoms. These organizations do not operate in isolation; instead, they share resources, payloads, and intelligence on targets, creating a force multiplier effect that allows them to scale their operations with terrifying efficiency. This industrialization of cybercrime means that a single vulnerability discovered by one group can be quickly weaponized and deployed across a global network of affiliates, ensuring that any gap in a target’s defense is exploited by the most capable actor available in the market.
Human and Ethical Dimensions of Digital Vulnerability
The human element remains the most unpredictable variable in the cybersecurity equation, as evidenced by the recruitment of “money mules” within high-security environments. When individuals with legitimate access to sensitive systems are manipulated or coerced into assisting criminal networks, the entire structure of internal trust collapses. This intersection of social engineering and financial crime highlights that technical controls are only as effective as the people who operate them. Furthermore, the rise of cryptocurrency flows to services linked to human rights abuses in Southeast Asia underscores the ethical gravity of digital security. The same vulnerabilities that lead to a corporate data breach are often the same ones that facilitate the financing of scam compounds and illicit networks, making the fight for cybersecurity a core component of global humanitarian efforts.
Privacy-preserving technologies are also facing a period of intense scrutiny as new de-anonymization techniques emerge. The discovery of “Adbleed” research showed that even users protected by VPNs can be identified through subtle fingerprinting techniques that probe for country-specific adblock filters. This revelation undermines the core promise of anonymity that many individuals and organizations rely on for sensitive operations. Simultaneously, legal frameworks are beginning to catch up with these technological realities, as seen in the significant fines levied against major corporations for confusing or deceptive privacy practices. The evolving regulatory environment suggests that businesses can no longer treat privacy as a secondary concern; it is becoming a primary legal and operational requirement that carries substantial financial and reputational risks.
Future Outlook: Strategic Implications
The Transition Toward Continuous Verification
The future of cybersecurity is predicated on a decisive move away from the “patch-and-forget” mentality that has dominated the industry for decades. Organizations are finding that the only viable path forward is the adoption of a Zero Trust architecture that applies not only to internal users but to every third-party integration and digital asset associated with the brand. This model requires a shift toward continuous verification, where every connection, API call, and plugin execution is validated in real-time. By assuming that the network is always compromised and that no asset is inherently trustworthy, defenders can create a more resilient environment that is capable of withstanding the rapid-fire exploitation cycles that define the current era. This transition will require a significant overhaul of legacy systems and a cultural shift in how IT teams view their role in the security ecosystem.
Potential developments in the near future include the widespread adoption of AI-specific benchmarks designed to evaluate how autonomous agents handle sensitive information. Frameworks such as the Security Comprehension Awareness Measure (SCAM) are becoming essential for organizations looking to integrate AI into their daily workflows without introducing catastrophic vulnerabilities. These benchmarks allow for a standardized way to test whether an AI agent can recognize a phishing attempt or a malicious prompt before it is given access to corporate data. As AI becomes more deeply embedded in administrative and creative processes, the ability to measure and mitigate the “trust gap” inherent in human-AI interaction will be a critical differentiator for secure organizations.
Addressing the Burden of Security Debt
A major challenge that continues to persist is the management of “security debt”—the accumulation of vulnerabilities in legacy codebases that have been grandfathered into modern environments. The recent discovery of a 20-year-old flaw in authentication services used in high-performance computing clusters serves as a warning that age does not equate to security. Many of the systems that power critical infrastructure and high-level research are built on foundations that were laid before the current threat landscape even existed. Addressing this debt will require a massive, industry-wide effort to audit and modernize legacy infrastructure, often at a significant cost in terms of time and resources. However, failing to do so leaves the door open for attackers to exploit well-known, foundational weaknesses that have been overlooked for decades.
The broader implication for all industries is an escalating need for rigorous auditing of abandoned or neglected digital infrastructure. Every domain, every API key, and every third-party account must be tracked and decommissioned when it is no longer in use to prevent it from becoming a weapon in the hands of an adversary. This level of digital hygiene is no longer a luxury but a fundamental requirement for maintaining national and corporate security. Furthermore, the implementation of strict, phishing-resistant Multi-Factor Authentication (MFA) remains one of the most effective defenses against the credential theft that fuels the Ransomware-as-a-Service ecosystem. As the “cartel” model of cybercrime continues to professionalize, the baseline for security must rise accordingly, making robust identity management the cornerstone of any defensive strategy.
The Role of Visualization and Attribution in Defense
As the volume and complexity of threat intelligence continue to grow, the industry is turning toward more advanced methods of visualization and attribution to make sense of the noise. Tools that can transform thousands of disparate data points—IP addresses, malware hashes, and actor profiles—into interactive, visual maps are becoming vital for security analysts. These tools allow for the identification of patterns and attack paths that would be impossible to see in a standard spreadsheet or report. By visualizing the connections between different threat clusters, defenders can better predict the next moves of an adversary and allocate their resources more effectively. This shift toward a more data-driven, visual approach to intelligence will be essential for staying ahead of the automated and AI-accelerated threats of the coming years.
Standardized threat attribution frameworks are also gaining traction as a way to reduce bias and improve the accuracy of how we categorize adversaries. By moving toward a common language and scoring system for evidence, the security community can share information more effectively and build a more comprehensive picture of the global threat landscape. This collaborative approach is necessary because no single organization has the visibility to track a sophisticated actor across the entire digital frontier. Improved attribution not only helps in the immediate response to an incident but also plays a role in the broader geopolitical and legal efforts to hold threat actors accountable for their actions.
Conclusion
The analysis of current trends in the cybersecurity landscape demonstrated that the exploitation of complexity and trust emerged as the primary driver of modern digital threats. It was observed that from the hijacking of abandoned Outlook add-ins to the rapid-fire deployment of zero-day exploits, the objective of the adversary remained focused on achieving quiet access and scalable impact through the manipulation of everyday digital tools. The evidence indicated that as organizations increased their reliance on cloud-native infrastructure and artificial intelligence, the attack surface expanded in ways that traditional, reactive defense models were unable to effectively manage. This situation placed a premium on the ability of defenders to move faster than automated scanners and to anticipate the creative ways in which AI-assisted actors could bypass existing security controls.
The strategic response to these challenges required a fundamental shift in how trust was managed within the digital ecosystem. Organizations that successfully navigated this period of transition were those that adopted a model of continuous verification and prioritized the elimination of “security debt” within their legacy systems. It was concluded that the professionalization of cybercrime into a cartel-like structure necessitated a similarly organized and collaborative approach to defense, where intelligence was shared and standardized across industry lines. The path forward involved not only the deployment of advanced technical controls, such as phishing-resistant MFA and AI-specific security benchmarks, but also a renewed commitment to basic digital hygiene and the rigorous auditing of all third-party integrations. Vigilance and the elimination of trust gaps ceased to be optional considerations and instead became the only viable strategies for maintaining security in an interconnected and increasingly automated world. (17,458 characters)