The digital infrastructure of the modern world currently finds itself in the crosshairs of a sophisticated and rapidly maturing cyber threat known as CVE-2025-55182, or more colloquially, React2Shell. What began as a theoretical risk in late 2025 has transitioned into a primary instrument for high-stakes espionage and large-scale automated exploitation, moving well beyond the reach of simple script kiddies. Recent intelligence reports have highlighted the emergence of a specialized toolkit titled “ILovePoop,” which, despite its juvenile naming convention, represents a highly professionalized reconnaissance engine capable of probing tens of millions of IP addresses globally. This tool specifically hunts for exposed React2Shell instances, signaling a shift toward “big game hunting” where the targets are not random individuals but the central pillars of the global economy. The sheer scale of these operations suggests a level of orchestration typically reserved for state-sponsored entities, turning a software flaw into a matter of international security.
Technical Severity and the Challenge of Detection
The Architecture of a Critical Flaw
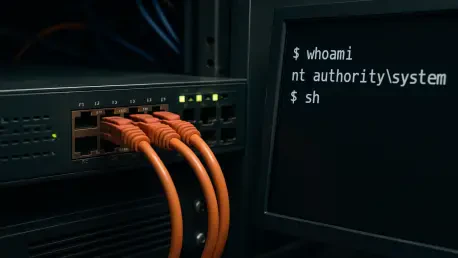
React2Shell represents a critical failure within the React Server Components, earning it a rare and maximum CVSS severity rating of 10.0 due to its extreme ease of exploitation. This vulnerability allows an attacker to achieve full remote code execution and administrative control over a target web server through a single, unauthenticated web request, bypassing traditional security perimeters entirely. Because React has become a foundational framework for hundreds of thousands of enterprise-level websites and applications, the potential attack surface is nearly immeasurable. This ubiquity means that a single successful exploit can grant an adversary a foothold in diverse environments ranging from small business portals to the internal dashboards of multi-national conglomerates. The technical simplicity of the exploit, coupled with the high privileges it grants, makes it one of the most significant threats to web integrity encountered in the current software development lifecycle.
The risk is amplified by the fact that the vulnerability exists at a deep architectural level where data serialization and component rendering intersect. When a server processes a malicious payload disguised as a legitimate component update, it inadvertently executes the attacker’s code with the same permissions as the web server process itself. This lack of isolation in the rendering pipeline means that traditional firewalls and signature-based detection systems often fail to recognize the incoming threat as anything other than standard web traffic. Furthermore, the speed at which an exploitation occurs—often in less than a second—leaves human responders with almost no window to intervene manually. As more organizations adopt server-side rendering to improve user experience, they inadvertently expand the footprint of this specific vulnerability, making the need for deep-seated architectural audits more pressing than ever before in the modern DevOps era.
Hidden Dependencies in Modern Frameworks
A significant hurdle in the current remediation effort involves the way modern development frameworks, specifically Next.js, manage their internal software dependencies. In many contemporary deployments, Next.js does not list React as a standard, transparent dependency in a way that is easily parsed by common security tools; instead, it “vendors” or bundles the package internally. This architectural choice creates a dangerous visibility gap for standard software composition analysis (SCA) tools, which may report a system as secure even when the vulnerable React code is present within the bundled framework. Consequently, IT departments may run their automated compliance scans and receive misleading “clean” results, while the underlying infrastructure remains wide open to the React2Shell exploit. This creates a “hidden” risk profile where the most diligent teams are lulled into a false sense of security by their own tooling.
This phenomenon of bundled vulnerabilities has contributed significantly to what researchers call the “long tail” of unpatched systems currently being harvested by various threat actors. Even when developers are aware of the React2Shell flaw, they may struggle to apply a patch if their deployment pipeline does not provide a direct way to update the vendored components without breaking the entire application. The complexity of these modern build processes often results in organizations running outdated versions of Next.js that contain the flawed React code, simply because the upgrade path is viewed as too risky or resource-intensive. As a result, the vulnerability persists in high-value environments long after a fix has been made available, providing a steady stream of targets for the “ILovePoop” toolkit and other automated scanning engines. This disconnect between patch availability and practical implementation remains one of the greatest challenges for cybersecurity.
The Evolution of Exploitation and Infrastructure
From Simple Botnets to Resilient Espionage
The trajectory of React2Shell exploitation has matured through distinct phases, moving from chaotic, unorganized attacks to highly disciplined and strategic operations. Immediately following the initial public disclosure, the internet experienced a massive “spray-and-pray” phase dominated by automated botnets and opportunists looking to install cryptominers. These early attackers lacked refinement, frequently attempting to run Linux-specific shell commands on Windows servers or using payloads that were easily flagged by basic endpoint detection systems. While disruptive, these initial waves were relatively easy to mitigate for organizations with standard security hygiene. However, the current landscape has shifted toward sophisticated tradecraft where the primary objectives are no longer immediate resource theft, but rather long-term persistence and the quiet infiltration of sensitive corporate and government networks.
The current generation of threat actors utilizing React2Shell displays a level of patience and technical depth that suggests professional or state-sponsored backing. Rather than immediately triggering an alarm by stealing data or encrypting files, these actors focus on establishing “low and slow” footholds within compromised environments. They use the initial RCE to deploy advanced backdoors that can lie dormant for months, waiting for the right moment to pivot deeper into the internal network. This shift in strategy reflects a broader trend in the cyber threat landscape toward intelligence gathering and strategic positioning, where the initial vulnerability is merely the key that opens the door. By the time an organization realizes they have been breached, the attackers have often already mapped out the entire network, identified key personnel, and secured multiple redundant access points that are difficult to fully eradicate.
PeerBlight: The Rise of Survivable Infrastructure
One of the most alarming developments in the post-exploitation phase of React2Shell is the widespread adoption of “PeerBlight,” a resilient communication technique. This method leverages the BitTorrent Distributed Hash Table (DHT) for command-and-control (C2) operations, allowing attackers to manage compromised servers through a decentralized peer-to-peer network. Unlike traditional C2 setups that rely on a single domain or a static IP address—which can be easily blocked or taken down by law enforcement—PeerBlight makes the attacker’s infrastructure nearly impossible to dismantle. Because the communication is distributed across thousands of legitimate peer-to-peer nodes, defense teams cannot simply “pull the plug” on the connection without affecting broad swaths of the internet’s normal traffic. This shift toward “survivable” infrastructure marks a transition into a more permanent and dangerous era of cyber warfare.
The use of PeerBlight demonstrates a commitment to long-term operational security that is rarely seen in common criminal activities. By hiding their control signals within the background noise of standard P2P traffic, attackers can maintain a constant link to their victims while remaining invisible to most network monitoring tools. This technique also allows for the dynamic updating of malicious payloads; if a specific malware strain is detected and removed, the decentralized network can simply push a new, modified version to the compromised host. For defenders, this creates a “whack-a-mole” scenario where traditional perimeter defenses are rendered obsolete. The integration of such resilient communication methods with a high-severity flaw like React2Shell has created a potent combination that ensures the vulnerability will remain a significant threat for years to come, even as patching efforts continue.
Global Impact and Defensive Hurdles
Targeting Critical Infrastructure: A Prelude to Action
Network telemetry and threat intelligence have revealed that the current scanning campaigns are far from random, showing a clear and calculated interest in high-value infrastructure. Probes from the “ILovePoop” toolkit have successfully touched more than 37,000 distinct networks, including those belonging to the Department of Defense, the Defense Information Systems Agency, and several state-level governments. Furthermore, major financial institutions such as JPMorgan Chase, Goldman Sachs, and PayPal have also been flagged as targets of interest. This systematic mapping of the dependencies within the Western economic and military apparatus suggests that these reconnaissance efforts are not merely academic exercises but are the necessary groundwork for future coordinated attacks. The data indicates a significant lag time between the initial “ping” and the actual exploit, suggesting that actors are building a comprehensive database of targets.
The involvement of suspected state-sponsored actors from regions such as China, Iran, and North Korea adds a geopolitical dimension to the React2Shell crisis. These actors are not just looking for financial gain; they are seeking strategic advantages by identifying vulnerabilities in critical energy utilities, industrial sectors, and major tech firms like Salesforce and Disney. The pattern of behavior observed by security analysts suggests a “preparation of the battlefield” mentality, where the vulnerabilities are documented and held in reserve for use during periods of heightened international tension. By the time a conflict reaches a tipping point, these actors could potentially disable critical services or compromise sensitive communications simultaneously, leveraging the access they are securing today. This long-term strategic planning makes the React2Shell scanning campaign one of the most significant precursors to potential large-scale cyber disruption.
Overcoming False Security and Remediation Barriers
Despite the widespread availability of security patches and technical advisories, several practical barriers continue to hinder the total eradication of React2Shell exposure. Beyond the complexities of bundled dependencies in frameworks like Next.js, modern cloud-native environments—often characterized by hundreds of microservices and ephemeral containers—make it difficult to ensure that every single instance of an application is running the latest code. Many organizations struggle with “shadow IT,” where legacy servers or abandoned testing environments remain connected to the internet without the knowledge of the central IT department. These forgotten assets provide easy entry points for attackers, who can use a single unpatched legacy server as a jumping-off point to move laterally into more secure and critical parts of the organization’s network.
Furthermore, the early days following the React2Shell disclosure were characterized by a flood of misinformation, including fake or non-functional proof-of-concept (PoC) exploits. This noise in the security community led some IT professionals to believe that the vulnerability was either overhyped or too difficult to weaponize effectively in a real-world scenario. This skepticism created a dangerous delay in the patching cycle, giving threat actors the window they needed to refine their tools and begin their mass-scanning operations. In reality, the genuine exploit is remarkably stable and requires no specialized knowledge of the target’s internal state, making it a “perfect” weapon for both automated botnets and precision-strike espionage groups. The combination of technical debt, complex deployment pipelines, and early misinformation has ensured that React2Shell remains a potent threat long after it should have been neutralized.
Moving forward, the mitigation of React2Shell requires a fundamental shift from surface-level scanning to deep, manual verification of software components. Organizations must adopt a proactive stance by decommissioning legacy systems that no longer serve a business purpose and implementing strict network segmentation to limit the potential for lateral movement if a breach occurs. It is no longer sufficient to rely on automated tools that may overlook bundled dependencies; instead, security teams should conduct thorough audits of their build pipelines and demand greater transparency from framework maintainers regarding internal packages. Furthermore, the adoption of zero-trust architectures can help neutralize the impact of a successful React2Shell exploit by ensuring that even a compromised server cannot access sensitive internal resources without additional, robust authentication. The window for easy remediation has passed, and the current landscape demands a disciplined, multi-layered approach to defense to prevent becoming the next entry in a state-sponsored target list.