Rupert Marais is a leading Security Specialist with a deep focus on endpoint protection, device security, and the evolving landscape of network management. His career has been defined by a commitment to deconstructing complex cybersecurity threats and developing robust strategies to protect high-value targets from state-sponsored actors. In this discussion, we explore the alarming tactics of the BlueNoroff hacking group, which has pioneered a “self-reinforcing” deepfake pipeline to compromise the cryptocurrency and blockchain sectors. We will delve into how these attackers use stolen webcam footage, AI-generated avatars, and typo-squatted domains to stage elaborate fake meetings that lead to total system compromise in mere minutes.
High-ranking executives in the cryptocurrency and blockchain sectors are being targeted via legitimate-looking business interactions on Telegram or Calendly. How do attackers build enough trust to lure a CEO into a meeting scheduled months in advance, and what specific psychological triggers make this long-game approach effective?
The attackers are masters of professional mimicry, often initiating contact through compromised Telegram accounts or by creating highly polished personas of venture capital partners, legal heads, or industry peers. By reaching out with a Calendly invite for a “catch-up” meeting scheduled five months into the future—such as an invite sent in late summer for a date in January—they effectively bypass the target’s immediate suspicion. This long-game approach exploits a psychological trigger of perceived legitimacy; a scammer is usually expected to act with urgency, whereas a professional contact is comfortable waiting months for a slot on a busy executive’s calendar. By the time the meeting date arrives, the target has long since forgotten any initial hesitation, and the event appears as a routine, established commitment in their workflow. This concentration on the crypto sector is no accident, as eight out of ten identified victims hold authority over wallet infrastructure or investment decisions, making the payoff for this patience incredibly lucrative.
Threat actors are now harvesting real-time webcam feeds from current victims to populate future fake meetings with authentic participant tiles. How does this “self-reinforcing” pipeline complicate traditional identity verification, and what are the technical challenges in detecting stolen, looped video versus a live stream during a call?
This pipeline represents a terrifying evolution in social engineering because it turns the victims themselves into the bait for the next attack. The group has analyzed more than 950 files from their media hosting servers, which include stolen webcam footage of at least 100 individuals, nearly half of whom are CEOs or co-founders. When a new target joins a fake meeting, they see a realistic interface populated with recognizable industry participants, which might include moving tiles of real people they have met at conferences or seen in the news. The technical challenge is that these aren’t just static images; the attackers use deepfake composite videos that combine AI-generated faces with actual human body motions, creating a convincing sense of “presence.” Because the audio is often intentionally sabotaged, the victim doesn’t realize the participants aren’t responding to them, making it nearly impossible to distinguish between a live stream and a high-quality stolen loop without advanced forensic tools.
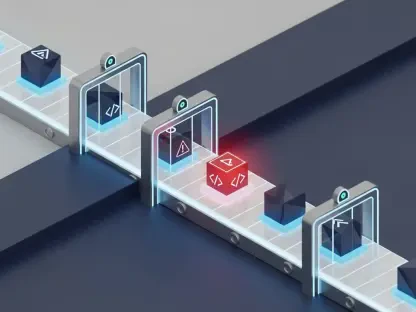
When a user enters a fabricated conference lobby, they often encounter intentional audio malfunctions that prompt a “Zoom SDK update” or similar fix. Can you walk us through the background execution process that allows a single click to install multiple malicious payloads, and why does this method bypass standard browser security?
The trap is set the moment a victim clicks on a typo-squatted Zoom URL and is directed to an HTML page that flawlessly mimics a conference lobby. To resolve the “broken” audio, the victim is presented with a “ClickFix” prompt to update their Zoom SDK, a request that feels entirely logical in the context of a technical glitch. Once that button is clicked, a rapid sequence of background actions is triggered, often involving PowerShell scripts that execute almost instantaneously to install payloads for command-and-control, credential harvesting, and wallet theft. This method is particularly effective at bypassing browser security because the victim has typically already granted microphone and camera permissions to the site, signaling to the browser that the domain is “trusted” by the user. By the time the user realizes the update didn’t fix the audio, the malware has already established persistence and begun siphoning sensitive data from the system.
Complete system compromise can occur in under five minutes, yet attackers often maintain persistence for over two months. What specific actions are taken during those first five minutes to secure long-term access, and what signs should security teams look for to identify dormant threats hiding in wallet infrastructure?
In those initial five minutes, the attackers move with surgical precision to ensure they don’t lose their foothold even if the victim reboots their machine. They prioritize the theft of Telegram sessions and browser-stored credentials, while simultaneously deploying persistence mechanisms that allow them to remain hidden for long periods—in one case, they stayed active for 66 days. During this dormant phase, they aren’t just sitting idle; they are monitoring wallet infrastructure and exchange platforms to wait for the most opportune moment to move funds. Security teams should be hyper-vigilant for subtle indicators like unauthorized clipboard abuse, which is a common tactic for swapping out crypto addresses during a transaction. Additionally, any unusual PowerShell activity or attempts to access credential stores should be treated as a critical red flag, even if the system appears to be functioning normally otherwise.
With dozens of typo-squatted domains being registered continuously, traditional blacklisting often fails to keep pace. What infrastructure monitoring strategies should organizations implement to catch these redirects, and how can they enforce stricter microphone or camera permissions without disrupting genuine business operations?
The sheer volume of this operation is staggering, with over 80 typo-squatted Zoom and Teams domains found registered with just one hosting provider, and new ones appearing constantly. To combat this, organizations must move away from reactive blacklisting and toward proactive infrastructure monitoring that flags any calendar links that deviate from known, legitimate patterns. One effective strategy is to implement an “allow-list” for microphone and camera permissions, where only a handful of verified enterprise domains are permitted to access these peripherals by default. For everything else, the system should require a multi-step approval process that alerts the user to the potential risk of an untrusted domain. Furthermore, employees must be trained to verify any unexpected meeting requests through a secondary channel, such as a direct phone call, to ensure that the person on the other end of the invite is who they claim to be.
What is your forecast for the evolution of AI-driven social engineering?
I anticipate that we are moving toward a period where “interactive” deepfakes will become the standard, moving beyond the silent lobbies we see today to full-voice, real-time AI clones. As the attackers refine their “self-reinforcing pipeline,” they will be able to generate entire panels of AI-driven experts who can answer questions and conduct complex business negotiations, making the detection of these scams nearly impossible for the average employee. We will likely see these tactics spread from the crypto sector into broader corporate finance and legal departments, where the stakes are equally high. Eventually, the only way to guarantee the identity of a participant in a digital meeting will be through cryptographically signed video streams and hardware-based identity verification. The era of trusting a face on a screen simply because it looks and moves like a person we know is rapidly coming to an end.