

Global tourism has surged to unprecedented heights, turning the digital networks that facilitate millions of daily bookings into a lucrative playground for sophisticated cybercriminal syndicates. As travelers demand seamless, interconnected experiences, the infrastructure supporting these

The silent infiltration of a corporate network often begins not with a sophisticated physical breach but with a single, deceptive click that mirrors a routine digital interaction. This subtle vulnerability was the cornerstone of an expansive illicit empire that facilitated over $20 million in
This transition signifies a fundamental pivot in market dynamics, moving value away from centralized API providers toward local compute optimization. Organizations that spent the last several years perfecting cloud-centric defenses now find themselves blind to the "edge," where inference happens on
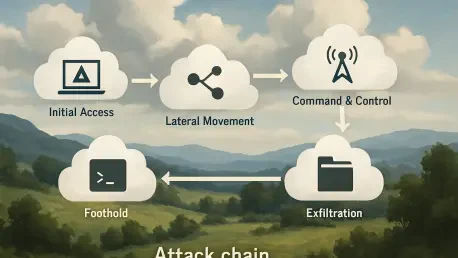
The rapid proliferation of autonomous artificial intelligence agents has outpaced the security frameworks designed to contain them, creating a fertile ground for sophisticated exploits like the Claudy Day attack chain. This specific vulnerability sequence, first identified by researchers at Oasis

Rupert Marais is a veteran security specialist who has spent years at the intersection of endpoint protection and network management. His expertise lies in dissecting how modern attackers bypass traditional defenses by targeting the trust relationships between software vendors and their users. In

The silent hum of a municipal water pump or the steady flicker of a city streetlight represents a fragile peace that is increasingly being tested by invisible digital adversaries. In the current landscape, Iranian state-sponsored cyber operations have transitioned from mere espionage to active

The persistent resilience of cybercriminal organizations has forced a paradigm shift in how digital infrastructure is protected, particularly as macOS environments face increasingly sophisticated intrusion techniques that target user behavior rather than just software flaws. One of the most

The rapid adoption of cloud-native architectures and artificial intelligence has dismantled the traditional, static perimeters that once defined corporate security. In the era of on-premises data centers, infrastructure changed at a glacial pace, allowing security teams to conduct periodic, manual

The rapid integration of generative artificial intelligence into the core of enterprise operations has created a landscape where a single autonomous agent possesses enough permissions to either streamline a global supply chain or inadvertently dismantle a company’s entire security perimeter. AWS

The sudden public release of a highly effective exploit code often forces a frantic race between malicious actors seeking to capitalize on a vulnerability and defenders scrambling to mitigate the risk before catastrophe strikes. This is precisely the scenario created by the "BlueHammer" zero-day
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy