

Rupert Marais is a leading security specialist at the forefront of endpoint protection and network management, bringing years of tactical experience to the evolving landscape of AI-driven defense. As the industry grapples with the emergence of autonomous offensive models, Rupert’s expertise
The traditional rhythm of software security has been shattered by an unprecedented acceleration in the speed at which vulnerabilities are identified and exploited by sophisticated automated systems. The National Cyber Security Centre (NCSC) warns that the global community is no longer facing a

The current evolution of the global cyber threat landscape is characterized by a rapid dissolution of the traditional barriers that once separated standard enterprise system intrusions from specialized cryptocurrency theft operations. Historically, the digital underground was largely divided into
The digital landscape remains highly susceptible to infrastructure instability, as evidenced by a recent ten-hour disruption that left thousands of professionals unable to access their primary communication tools. This incident, which occurred on April 27, manifested as a significant service

As a veteran in endpoint security and network management, Rupert Marais has spent years navigating the intersection of emerging technology and rigid regulatory frameworks. With the Australian Prudential Regulation Authority recently flagging significant gaps in how financial giants manage

The era of the isolated software developer meticulously hand-writing thousands of lines of code is rapidly giving way to a new paradigm where high-level architectural oversight and systemic vision are the primary drivers of technological innovation. At the recent AI Dev 26 x SF conference, industry

The rapid evolution of high-capability neural networks has fundamentally altered the paradigm of digital warfare, transforming once-theoretical risks into immediate national security imperatives. Frontier AI represents the vanguard of this shift, where high-parameter models are no longer just

Market Context and Why It Matters Mailbox storms no longer signal mere annoyance; they now mask credential raids staged through cloud trust, browser add-ons, and scripts that look benign until they quietly seize the keys to the company. The surge in collaboration platforms and sanctioned cloud
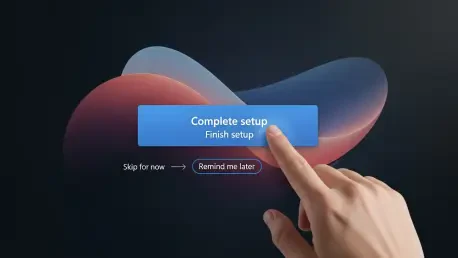
Lead: The Surprise Setup That Wouldn’t Stay Finished Few phrases on a corporate PC triggered more anxiety than a chipper banner announcing “You’re almost done setting up your PC,” surfacing months after the actual setup had been completed and right when a user needed to get work done. The timing

Home internet once felt as simple as plugging in a router, but overnight the buying rules changed when the nation’s top telecom regulator widened a ban to devices most people consider pocket essentials. The Federal Communications Commission has clarified that its month‑old prohibition on new
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy