
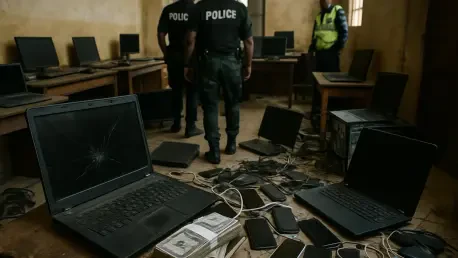
Imagine a digital landscape where nearly 88,000 individuals across Africa fall victim to cybercrime, losing close to $485 million in just a few months, prompting a groundbreaking response through Operation Serengeti 2.0, an Interpol-led initiative that has captured global attention. Conducted over

What happens when a biopharmaceutical giant like AbbVie, entrusted with safeguarding sensitive patient data and groundbreaking research, faces an unrelenting wave of cyber threats? In an era where a single breach can cost millions and shatter trust, the answer lies in artificial intelligence (AI)—a
I'm thrilled to sit down with Rupert Marais, our in-house security specialist with deep expertise in endpoint and device security, cybersecurity strategies, and network management. Today, we’re diving into the exciting advancements in AI-driven security solutions, inspired by recent innovations in

In an era where digital landscapes shape much of childhood experience, a startling revelation has emerged from the UK: a survey of young adults aged 16 to 21 disclosed that over a quarter had stumbled upon explicit content online by the tender age of 11, with a staggering 70% encountering it before

What happens when the technology driving innovation also becomes a gateway for catastrophic cyberattacks? Artificial intelligence (AI) is reshaping industries with unparalleled efficiency, yet a single breach in an AI system could expose sensitive data or disrupt critical operations on a massive

I'm thrilled to sit down with Rupert Marais, our in-house security specialist with deep expertise in endpoint and device security, cybersecurity strategies, and network management. Today, we’re diving into the fascinating world of securing high-stakes tech events like Black Hat USA, where Rupert

Unveiling the Human Factor in Cybersecurity Threats Imagine a scenario where a seemingly harmless email from a trusted colleague requests urgent access to sensitive data, only to reveal later that it was a meticulously crafted deception designed to exploit trust. This is the reality of social

What happens when businesses struggle to protect users from escalating cyber threats while also chasing sustainable revenue? In today’s digital battleground, where data breaches impact millions annually, a staggering 60% of companies report financial strain from balancing security and

Imagine a world where every private conversation, every sensitive business deal, and every personal message could be intercepted without your knowledge, leaving you vulnerable to unseen threats. In an era of escalating cyber threats and data breaches, end-to-end encryption (E2EE) stands as a

Introduction Welcome to an insightful conversation on the latest cybersecurity threats targeting web protocols. Today, I'm joined by Rupert Marais, our in-house security specialist with extensive expertise in endpoint and device security, cybersecurity strategies, and network management. With the
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy