

I'm thrilled to sit down with Rupert Marais, our in-house security specialist with deep expertise in endpoint and device security, cybersecurity strategies, and network management. With the rapid advancements in AI technology and its increasing accessibility, there are growing concerns about its

Imagine a digital ecosystem trusted by millions, including over 70 percent of Fortune 500 companies, suddenly becoming a gateway for a sophisticated cyberattack that shakes the foundation of software security. This scenario unfolded with Nx, a cornerstone of the NPM ecosystem, which faced a

In an era where technology evolves at a breakneck pace, the cybersecurity landscape faces a chilling new threat with the emergence of an unprecedented type of ransomware that leverages artificial intelligence to amplify its destructive potential. Known as PromptLock, this malware marks a

In a cybersecurity landscape where identity breaches have become one of the most common entry points for attackers, a major deal has just reshaped the industry. Palo Alto Networks, a heavyweight in network security and next-generation firewalls, has announced the acquisition of CyberArk, a leader

I'm thrilled to sit down with Rupert Marais, our in-house security specialist with a wealth of experience in endpoint and device security, cybersecurity strategies, and network management. Today, we’re diving into a recent, alarming data theft campaign targeting hundreds of Salesforce customers,
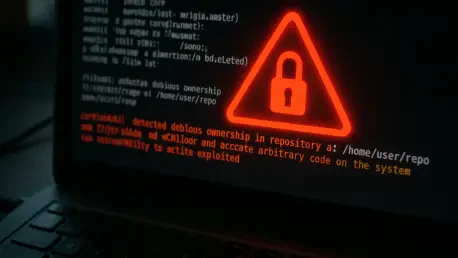
In a deeply alarming development for the tech community, a critical vulnerability in Git, identified as CVE-2025-48384, has emerged as a prime target for attackers, with active exploitation already underway, posing a severe risk to developers and organizations worldwide. This flaw, embedded in the

In an era where digital security is paramount, the discovery of critical vulnerabilities in widely used software can send shockwaves through the cybersecurity community, exposing potential risks to countless organizations. Privileged access management (PAM) solutions are designed to safeguard the

Imagine a scenario where a trusted colleague calls with an urgent request for sensitive data, only to later discover it was a hacker in disguise. This chilling reality struck Workday, a leading AI-driven platform for HR and payroll management used by over 11,000 organizations globally, including

What if a seemingly harmless image file could silently compromise an iPhone, iPad, or Mac without any action on the user's part? This chilling possibility became a reality with a recently discovered zero-day vulnerability in Apple's systems, prompting an urgent security patch. In an era where

Setting the Stage: A New Era in Cloud Computing In an era where digital transformation dictates the pace of business innovation, container management has become the backbone of scalable, efficient IT infrastructure. With enterprises worldwide handling billions of containerized workloads annually,
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy