
In an era where digital infrastructure represents the backbone of modern society, the persistent threat of cyber espionage from powerful nation-states like China and Russia has indeed spotlighted the urgent necessity for robust cybersecurity measures. National security entities worldwide have

The alarming rise of crypto phishing scams on Telegram has caught the attention of cybersecurity experts as these attacks have surged by over 2,000% since November 2024, according to the cybersecurity firm Scam Sniffer. This increase marks a significant shift towards sophisticated, malware-driven
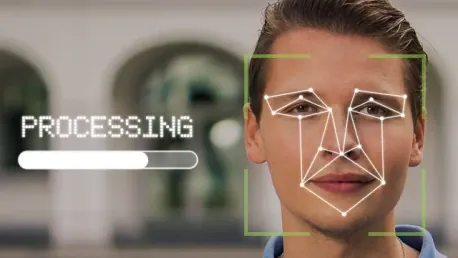
In today's digital age, the rise of deepfake technology poses significant challenges. Deepfakes, which use artificial intelligence to create realistic but fake videos and audio recordings, have become increasingly sophisticated and harder to detect. This article aims to inform readers about how

In an ever-evolving digital landscape fraught with cyber threats, organizations must constantly innovate to stay ahead of potential breaches. Contrast Security's new tool, Application Vulnerability Monitoring (AVM), is poised to significantly enhance how we protect applications in production

Open Source Software (OSS) has become an integral part of modern digital infrastructure, powering nearly 90% of code bases and constituting 70-80% of the material in many applications. However, this widespread adoption has also introduced significant security challenges. As we look ahead to 2025,

In response to an increasing number of sophisticated cyberattacks on U.S. federal agencies, critical infrastructure providers, and high-profile individuals, the Biden administration has released a comprehensive executive order aimed at bolstering cybersecurity across various sectors. Issued on