
Background and Context for Wireless Attack Surfaces in EV Micromobility How Bluetooth Pairing Works on Electric Motorcycles and Why It Matters Bluetooth on electric motorcycles links a rider’s phone or service tablet to the bike for diagnostics, configuration, and firmware updates. On affected Zero
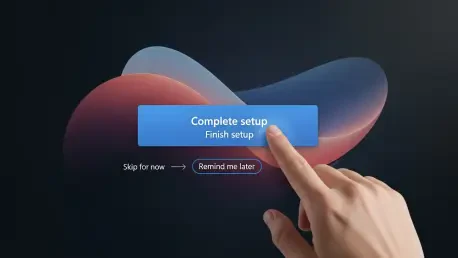
Lead: The Surprise Setup That Wouldn’t Stay Finished Few phrases on a corporate PC triggered more anxiety than a chipper banner announcing “You’re almost done setting up your PC,” surfacing months after the actual setup had been completed and right when a user needed to get work done. The timing

Beneath the servers, switches, and safety controllers that define digital operations, a quiet layer now decides uptime, stability, and even human safety by shaping the voltage and timing that every system consumes, yet it often sits outside the field of view for modern security tools. As DC power

Back-to-back meetings blur into a single rush when a trusted name on Telegram insists a quick Terminal paste will rescue a failing call, nudging macOS users to trade caution for speed at the exact moment a thief needs only one click. That is the opening the ClickFix technique exploits: it turns the

Home internet once felt as simple as plugging in a router, but overnight the buying rules changed when the nation’s top telecom regulator widened a ban to devices most people consider pocket essentials. The Federal Communications Commission has clarified that its month‑old prohibition on new

Why Passwords Finally Lost Their Last Safe Harbor Passwords are still the soft underbelly of enterprise access, bleeding breaches through reuse, phishing, and silent credential theft on unmanaged Windows PCs, and the lingering dependence on text secrets has turned shared and personal devices into