
The digital landscape has transformed into a high-stakes battlefield where the traditional leverage held by cybercriminals is rapidly eroding as organizations refuse to be intimidated by extortion. Recent data reveals a startling divergence in the cybercrime economy: while the total number of

Rupert Marais is a leading authority in the field of endpoint security and cybersecurity strategy, currently serving as an in-house specialist focused on the intersection of human behavior and digital risk. With years of experience managing complex network infrastructures, he has witnessed
Rupert Marais brings a wealth of experience to the table when it comes to the shadowy world of cybercrime infrastructure. As an expert in endpoint security and network management, he has watched the ebb and flow of criminal groups as they navigate law enforcement crackdowns and internal power
Rupert Marais serves as a premier specialist in the high-stakes world of enterprise security, bringing a wealth of experience in endpoint protection, network management, and the architectural nuances of distributed systems. With a career dedicated to defending complex infrastructures, he has

The modern healthcare landscape relies heavily on a complex web of interconnected service providers, yet this interdependence often introduces silent vulnerabilities that can jeopardize the privacy of thousands of patients in a single incident. Recently, Vikor Scientific, a South Carolina-based
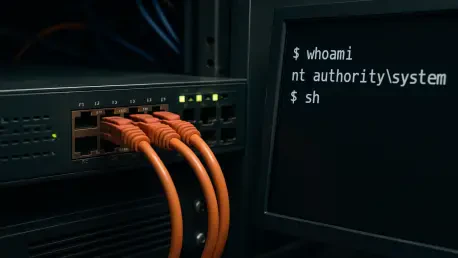
The digital infrastructure of the modern world currently finds itself in the crosshairs of a sophisticated and rapidly maturing cyber threat known as CVE-2025-55182, or more colloquially, React2Shell. What began as a theoretical risk in late 2025 has transitioned into a primary instrument for