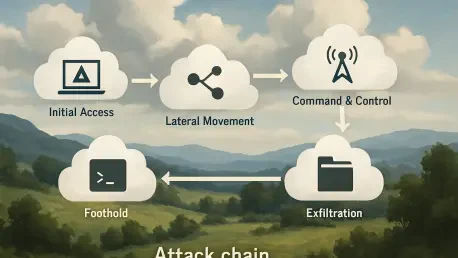
The rapid proliferation of autonomous artificial intelligence agents has outpaced the security frameworks designed to contain them, creating a fertile ground for sophisticated exploits like the Claudy Day attack chain. This specific vulnerability sequence, first identified by researchers at Oasis
The rapid migration of personal health management to digital platforms has created an unprecedented concentration of intimate data that now serves as the primary target for sophisticated global cybercrime syndicates. As telehealth becomes the standard for modern care, the recent compromise of Hims

Rupert Marais is a veteran security specialist who has spent years at the intersection of endpoint protection and network management. His expertise lies in dissecting how modern attackers bypass traditional defenses by targeting the trust relationships between software vendors and their users. In
When a digital security mechanism intended to protect personal data inadvertently becomes the primary obstacle to accessing it, the fundamental promise of mobile reliability begins to unravel. The iOS keyboard software regression represents a critical inflection point in the evolution of mobile

The velocity at which artificial intelligence has transformed from a curious collection of chatbots into the primary engine of global financial markets and logistics management is nothing short of unprecedented in the history of industrial computing. Organizations that once viewed these systems as

Rupert Marais is a veteran in the cybersecurity field, specializing in protecting the very endpoints and networks that global healthcare platforms rely on. With years of experience managing complex digital infrastructures, he offers a unique perspective on the recent breach affecting Healthdaq, a
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90