
Understanding the Cyber-Physical Threat to Financial Institutions The modern era of financial crime has shifted from the brute force of sledgehammers to the silent precision of laptops, as criminals now manipulate the very software governing cash withdrawals. The financial sector is currently
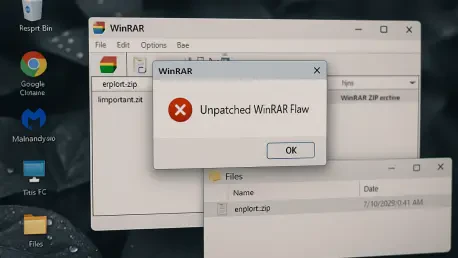
With us today is Rupert Marais, our in-house security specialist, whose expertise in endpoint security and cybersecurity strategies offers a critical perspective on today’s threats. We’re delving into a widespread vulnerability in a piece of software that many of us have used for decades: WinRAR.

The trust placed in a simple software update notification can become a gateway for sophisticated espionage, a reality recently underscored by a targeted attack that turned a trusted developer tool into a weapon. Secure software update mechanisms represent a critical line of defense in the
We're joined today by Rupert Marais, our in-house security specialist, to discuss a deeply concerning development in the mobile threat landscape. A new firmware backdoor, Keenadu, has been discovered embedded in Android devices, delivered through legitimate-looking system updates. This malware

An elusive and financially motivated threat actor, identified as GS7, is currently orchestrating a large-scale, sophisticated phishing campaign that meticulously weaponizes the brands of Fortune 500 companies against their own customers and employees. This operation, codenamed "Operation

Today we’re speaking with Rupert Marais, our in-house security specialist, about a series of newly disclosed techniques that turn the humble Windows shortcut, or LNK file, into a surprisingly potent tool for cyberattacks. We'll be exploring the technical nuances of how these shortcuts can be