
An official-looking email from the tax department lands in an inbox, complete with logos and formal language, yet it conceals a sophisticated cyber weapon designed to dismantle digital defenses from within. This research summary analyzes a sophisticated cyber espionage campaign targeting Indian

The immense popularity of everyday software utilities creates a landscape of trust that cybercriminals are increasingly adept at exploiting through highly convincing fraudulent websites and sophisticated malware. A newly uncovered campaign is leveraging the trusted name of the WinRAR file archiver

Introduction The very tools designed to protect a network's integrity can sometimes become the most significant points of failure, creating unforeseen pathways for malicious actors to exploit. In a recent development, Trend Micro has moved to address such a risk by releasing crucial security

A recent and comprehensive security disclosure has cast a harsh spotlight on the inherent risks of self-hosted infrastructure, revealing that the popular open-source platform Coolify contains a staggering 11 critical vulnerabilities that could allow attackers to achieve a full compromise of the
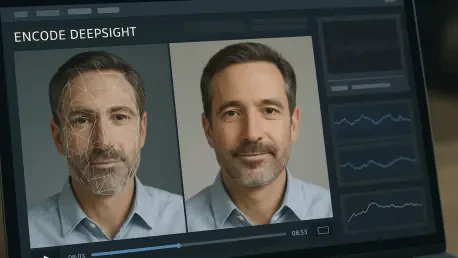
The rapid sophistication of deepfake technology has transformed what was once a social media novelty into a critical security vulnerability for businesses that depend on digital identity verification for their core operations. As synthetic media becomes more accessible and convincing, conventional

In a bustling digital landscape where viral content can shape opinions in mere hours, a chilling scenario emerges: a video of a political leader making a shocking statement spreads across social media, only to be revealed as a fabrication. Yet, the damage is done—public trust erodes, and chaos