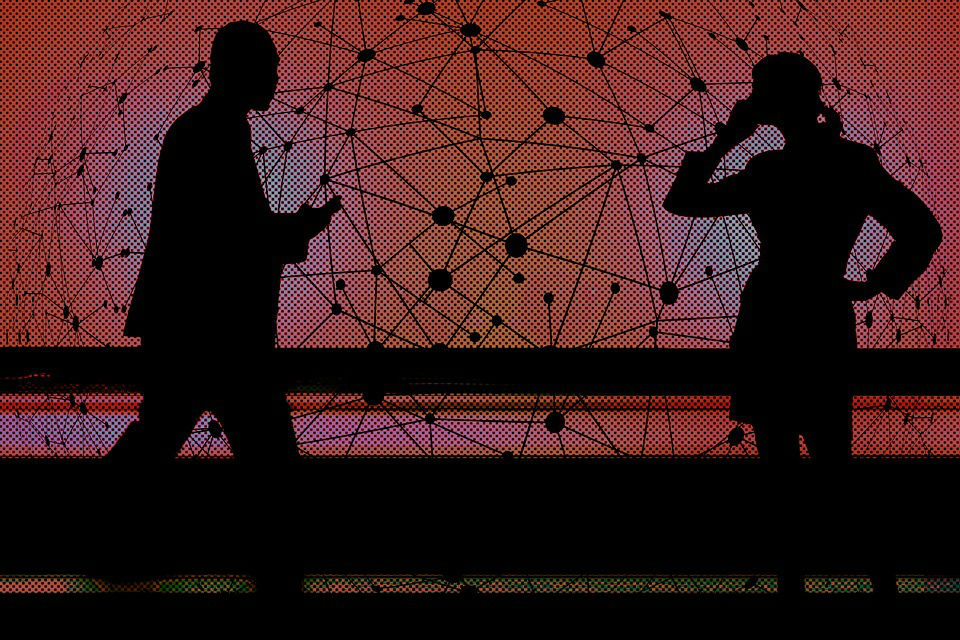
We discussed several times the rule of the SS7 signaling protocol in mobile communications and how to exploit its flaws to track users.
When mobile users travel between countries, their mobile devices connect to the infrastructure of a local operator that communicates with their operator back home. The SS7 protocol allows to implement roaming, but as explained it is also affected by many vulnerabilities that could be exploited for: