The security perimeter that once defined the digital enterprise has effectively dissolved, leaving modern organizations to grapple with a landscape where trust is no longer a given but a verified exception. For years, the industry treated Zero Trust as a lofty ideal—a goal that lived primarily in white papers and high-level strategy meetings. Today, that abstraction has been replaced by a rigorous focus on granular defense and the practicalities of securing hybrid environments. This shift reflects a collective realization that protecting data requires more than just a strong front door; it demands a continuous, data-driven validation of every single interaction within the network.
As organizations move into a new phase of maturity, the focus has pivoted from discussing “what” Zero Trust is to “how” it can be maintained under the pressure of real-world operations. This transition is significant because it marks the end of the honeymoon phase for cybersecurity marketing and the beginning of a disciplined era of risk reduction. The following exploration delves into how industry leaders are bridging the gap between strategic intent and the stubborn realities of legacy infrastructure, policy sprawl, and the persistent threat of lateral movement.
The Shift From Conceptual Vision to Granular Defense
The transition toward a functional Zero Trust model is driven by the undeniable complexity of contemporary IT ecosystems. Businesses are no longer operating within the neat boundaries of a single data center; instead, they manage a sprawling web of cloud services, remote endpoints, and on-premises hardware. Because the old methods of “trusting” anything inside the corporate network have proven disastrous, the industry has embraced a more skeptical posture. This evolution ensures that security is no longer a static wall but a dynamic, intelligent layer that follows the user and the application regardless of location.
Modern practitioners are now focusing on the essential background of their digital traffic, moving beyond broad connectivity to a state where every request is scrutinized. This significance cannot be overstated, as it represents the difference between a minor incident and a catastrophic breach. By emphasizing granular control, organizations are finally addressing the root cause of many high-profile failures: the inherent over-privileged nature of legacy networks. This article will examine the specific shifts in governance, the role of automation, and the strategies used to shrink the internal attack surface.
Moving Beyond the “Conference Version” of Cybersecurity
Abandoning the Universal Panacea for Pragmatic Localized Solutions
For a long time, the “conference version” of Zero Trust was sold as a transformative big idea that would instantly render traditional tools like VPNs obsolete and solve all security woes in one sweep. However, current data suggests that the most successful organizations have abandoned this search for a universal panacea. Instead, they are adopting a “small and specific” mindset, applying rigorous verification to localized challenges rather than attempting a total network overhaul overnight. This pragmatic approach focuses on mundane but critical questions regarding user identity and resource necessity.
The debate now centers on whether the initial grand promises of Zero Trust actually hindered progress by making the goal seem unattainable. Some analysts argue that by chasing an all-encompassing solution, many firms ignored the fundamental work of securing individual access points. Real-world applications now favor a model where progress is measured by the number of services moved to a “never trust” footing rather than the adoption of a single vendor platform. This change in perspective helps teams avoid the paralysis that often comes with trying to re-architect an entire enterprise at once.
The Consolidation Imperative and the Rise of Unified Control Planes
The rise of the consolidation imperative is perhaps the most visible industry shift, as security teams move away from a chaotic sprawl of “best-of-breed” tools. Fragmentation has been identified as a primary reason why Zero Trust progress stalls; managing policies across several disparate systems creates blind spots that attackers are quick to exploit. To counter this, there is a strategic push toward establishing a unified control plane. By funneling traffic through integrated frameworks like Secure Access Service Edge, organizations can maintain a consistent security posture across their entire footprint.
This movement toward a streamlined security stack is driven by survival rather than just budgetary preference. When a security team can manage their entire hybrid network from a single interface, they reduce the risk of inconsistent “allow” rules and human error. However, this trend also introduces the risk of vendor lock-in and creates a high-stakes central point of failure. Despite these risks, the consensus among experts is that the benefits of visibility and simplified policy management far outweigh the challenges of managing a fragmented collection of niche security products.
AI Integration and the Ongoing Struggle with Architectural Hygiene
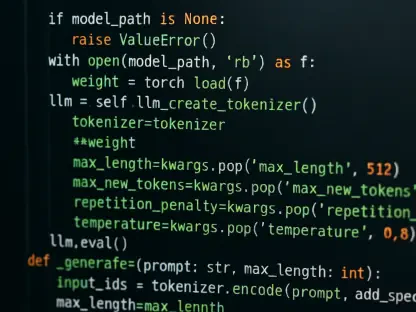
Artificial intelligence has become a major accelerant in the quest for Zero Trust, with a significant majority of organizations modifying their strategies to incorporate automated analytics. These tools are being used to detect policy drift, analyze network flows, and streamline the approval of security changes at speeds humans cannot match. Innovative applications of AI allow for real-time adjustments to access privileges based on shifting risk signals. Yet, a critical irony persists: much of this sophisticated intelligence is being layered on top of architectures that are fundamentally cluttered.
Industry dynamics suggest that while AI provides a necessary layer of intelligence for modern scale, it cannot substitute for sound architectural hygiene. The ongoing struggle involves cleaning up “excess access” and legacy segments that were never designed for a Zero Trust world. Experts warn that automating a flawed policy only results in faster, more widespread mistakes. Therefore, the most successful implementations are those where AI is used specifically to identify and remediate technical debt, rather than merely acting as a superficial wrapper for old habits.
Shrinking the Blast Radius Through East-West Traffic Governance
The true measure of an operational Zero Trust environment lies in its ability to limit the “blast radius” of a potential breach. This requires a shift in focus from defending the perimeter to governing east-west traffic, which refers to the communication between servers and applications inside the network. Historically, once an attacker gained entry, they could move laterally with ease. Today, the priority has shifted toward ensuring that even if a credential is stolen, the intruder finds themselves trapped in a tiny, isolated segment with no way to navigate the broader system.
Comparative analysis of recent security incidents shows that organizations prioritizing application-level access over raw network reach recover significantly faster. By restricting users to specific applications rather than giving them access to entire subnets, the internal attack surface is dramatically reduced. Future directions in this area involve context-based policies that consider device posture and real-time behavioral signals. This level of depth ensures that identity is not just a static password but a continuous stream of verifiable evidence that justifies access to sensitive resources.
Strategies for Bridging the Gap Between Policy and Execution
Closing the gap between high-level policy and daily execution requires a disciplined approach to eliminating long-lived privileges. One of the most effective best practices is the transition to “just-in-time” access, where permissions are granted only for the duration of a specific task. This prevents the accumulation of dormant accounts that are prime targets for exploitation. Moreover, security leaders must work closely with application owners to ensure that re-architecting trust boundaries does not disrupt the flow of business, treating security as an enabler rather than a roadblock.
Another actionable recommendation is to prioritize the monitoring of internal communication paths that have traditionally been ignored. By implementing rigorous logging and data-driven verification for every internal service, a business can create a transparent trail of all digital interactions. This transparency is vital for proving that Zero Trust is actually working. Practically, this means moving away from broad “trusted” segments and replacing them with small, well-defined communication paths that are governed by the principle of least privilege.
The New Era of Disciplined Risk Reduction
The transition from theory to practice has clarified that Zero Trust is not a destination to be reached but a continuous discipline of risk reduction. The narrative has successfully shifted away from abstract concepts, landing firmly in the realm of operational reality where success is measured in logs, verified identities, and contained incidents. Organizations that recognized the importance of simplification over complexity were the ones that made the most significant gains. They realized that the value of the framework was not in its novelty, but in its ability to impose order on a chaotic digital environment through consistent, granular control.
Cybersecurity teams moved toward a model where every internal service was required to verify its identity, effectively neutralizing the threat of lateral movement. This maturation process highlighted that technical debt and legacy systems were the largest hurdles to progress, requiring a steady, long-term commitment to architectural cleanup. By embracing automation to manage policy drift and focusing on shrinking the internal attack surface, the industry began to turn the tide against increasingly sophisticated adversaries. Ultimately, the successful deployment of these principles provided a resilient foundation that allowed businesses to operate with confidence in an inherently untrustworthy digital world.