The rapid migration of personal health management to digital platforms has created an unprecedented concentration of intimate data that now serves as the primary target for sophisticated global cybercrime syndicates. As telehealth becomes the standard for modern care, the recent compromise of Hims & Hers Health, Inc. provides a harrowing blueprint of the risks inherent in the digital wellness economy. This incident did not just expose basic identifying information; it laid bare the private medical inquiries of thousands, illustrating a growing tension between the convenience of on-demand prescriptions and the absolute necessity of medical-grade data protection.
This market analysis explores how a decentralized support infrastructure became the Achilles’ heel for a multi-billion dollar platform. By examining the mechanics of the breach and the subsequent industry response, we can identify a significant shift in the risk profile of the digital health sector. The focus now moves beyond simple financial fraud toward a more predatory era of digital extortion, where the perceived “social cost” of exposed medical conditions becomes the primary currency for threat actors.
Assessing the Fallout: Telehealth Security in the Spotlight
The expansion of the telehealth sector has permanently altered the healthcare landscape, moving sensitive consultations from the privacy of a doctor’s office to the cloud. However, this transition has introduced significant security gaps that traditional medical institutions spent decades fortifying. The Hims breach serves as a case study in how rapid scaling and a focus on user acquisition can sometimes outpace the implementation of rigorous security protocols. When a platform manages conditions like mental health or sexual wellness, the data it holds becomes exponentially more valuable on the dark web compared to standard retail information.
Moreover, the fallout from this incident has forced a re-evaluation of how digital health brands are valued. Investors and consumers alike are beginning to look past the user-friendly interface and focus instead on the resilience of the back-end infrastructure. As the market matures, the ability to prove total data sovereignty is becoming a competitive advantage rather than just a regulatory checkbox. The industry is currently facing a reckoning where the trust gap created by such breaches could slow the adoption of newer, even more personal digital health services.
From Growth to Vulnerability: The Rise of Digital Health Platforms
Telehealth platforms initially gained traction by promising a frictionless experience, removing the “embarrassment factor” and wait times associated with physical clinics. Hims & Hers leveraged this by building a brand that felt more like a lifestyle choice than a medical provider. This marketing-heavy approach allowed for massive growth, but it also required a complex web of third-party tools to manage the influx of customer queries and prescriptions. The historical shift toward using external customer service stacks created a fragmented data environment that proved difficult to defend against focused external threats.
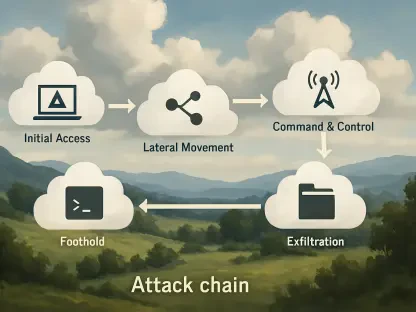
The reliance on these external vendors for core operations is now recognized as a systemic vulnerability across the entire digital economy. While the primary medical records might be siloed and encrypted, the support tickets—which often contain the same level of sensitive detail—were managed in a more accessible environment. This structural imbalance between “hardened” core databases and “soft” peripheral support systems is exactly what threat actors are currently exploiting to bypass traditional security perimeters.
The Breach Mechanics and the Third-Party Risk Factor
Unauthorized Access via Customer Support Infrastructure
The specific failure point in the Hims incident was a third-party platform used to manage support interactions, highlighting the dangers of the modern “integrated stack.” Unauthorized actors gained entry in early February and were able to monitor and exfiltrate support tickets for several days. This demonstrates that even if a company maintains perfect internal security, its data is only as safe as the weakest link in its vendor chain. The breach confirms that support logs are now viewed as a secondary medical record by hackers, one that often lacks the same level of oversight and encryption.
The Sensitivity of Protected Health Information
Protected Health Information (PHI) is inherently different from financial data because it has no expiration date. If a credit card is stolen, it can be cancelled; if medical history is exposed, that information remains true forever. In the context of Hims, the stolen data included descriptions of highly personal medical concerns, creating a digital footprint that patients never intended to be public. This permanence makes PHI the most valuable asset in the cybercrime economy, as it allows for long-term profiling and targeting of individuals based on their most private health struggles.
The Threat of Extortion and the Embarrassment Factor
The involvement of the group ShinyHunters introduces a predatory element to the breach, as they specialize in using stolen data for direct extortion. For Hims customers, the danger is not just identity theft but the threat of their medical history being used as leverage for blackmail. This “embarrassment factor” is a psychological weapon that cybercriminals use to increase their success rates. By holding a mirror to a user’s most private insecurities, attackers can demand high ransoms, knowing that many victims would pay significant sums to keep their medical records from being leaked to family, employers, or the public.
Looking Ahead: Regulatory Shifts and Technological Safeguards
In the coming years, we can expect a dramatic tightening of regulations surrounding how telehealth companies handle non-medical data like support logs and marketing profiles. Regulators are likely to mandate that any system containing patient-linked information must adhere to the same HIPAA-level standards as a primary electronic health record. This will necessitate a move toward “zero-trust” architectures where even third-party customer service bots have no persistent access to identifying information. Furthermore, the industry is projected to adopt more aggressive data-purging policies to ensure that sensitive transcripts are deleted the moment a query is resolved.
Technological shifts will also likely include the integration of localized processing, where sensitive data never leaves the patient’s device in an unencrypted state. This “privacy-by-design” approach will be essential for platforms to remain viable in an increasingly skeptical market. As we move from 2026 toward 2028, the firms that prioritize these high-cost, high-security infrastructures will likely consolidate the market, while those relying on cheaper, legacy third-party tools will find themselves uninsurable and unable to maintain consumer trust.
Strategies for Recovery and Enhanced Data Stewardship
For organizations currently operating in this space, the path to recovery involves a total audit of the “data supply chain.” It is no longer sufficient to secure the front door; companies must account for every transcript, email, and chat log that passes through an external server. Best practices now include implementing mandatory end-to-end encryption for all support channels and requiring vendors to undergo frequent, unannounced security audits. Transparency has also emerged as a vital tool; companies that disclose breaches quickly and provide comprehensive remediation are seeing much faster trust recovery than those that attempt to minimize the event.
Consumers are also becoming more savvy, learning to demand “security tiers” from their providers. This shift in behavior is forcing telehealth companies to view security not as a cost center, but as a primary feature of the product itself. Moving forward, the most successful platforms will be those that provide granular control to the user, allowing them to choose exactly how long their data is stored and who is allowed to access it. This democratization of data stewardship is the only way to build a sustainable model for digital health in an era of constant cyber threats.
Rebuilding Trust in a Post-Breach Environment
The Hims & Hers incident effectively demonstrated that the “growth-at-all-costs” era of telehealth has reached its limit. As medical services continue to decentralize, the responsibility of providers to act as impenetrable digital fortresses was made undeniably clear. The industry realized that a single point of failure in a third-party support tool could unravel years of brand-building and customer loyalty. Consequently, the focus was redirected toward building unified security environments that treat every interaction as a clinical record.
Ultimately, the sector began to move away from fragmented customer service models toward integrated, in-house solutions that offer superior oversight. Investors shifted their capital toward platforms that demonstrated a “privacy-first” architecture, recognizing that long-term viability was impossible without it. The lessons learned from the exposure of sensitive inquiries prompted a fundamental redesign of how digital health companies interact with their users, ensuring that the convenience of a screen never again compromised the sanctity of the patient-doctor relationship.