
Introduction to Nevada's Ransomware Crisis Imagine waking up to find that essential government services, from renewing a driver's license to accessing unemployment benefits, are suddenly unavailable due to a malicious cyberattack. This scenario became a harsh reality for Nevada residents when a

I'm thrilled to sit down with Rupert Marais, our in-house security specialist with deep expertise in endpoint and device security, cybersecurity strategies, and network management. Today, we're diving into a critical issue in the realm of software supply chain security—a recently discovered flaw in

I'm thrilled to sit down with Rupert Marais, our in-house security specialist with deep expertise in endpoint and device security, cybersecurity strategies, and network management. With the rapid advancements in AI technology and its increasing accessibility, there are growing concerns about its

In an era where cyber threats evolve at an unprecedented pace, Palo Alto Networks, a globally recognized leader in cybersecurity, has introduced a transformative suite of solutions to confront the dual challenges of quantum computing risks and the intricacies of multi-cloud environments. This
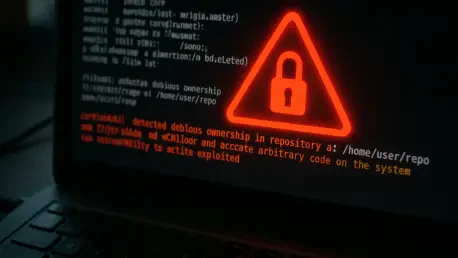
In a deeply alarming development for the tech community, a critical vulnerability in Git, identified as CVE-2025-48384, has emerged as a prime target for attackers, with active exploitation already underway, posing a severe risk to developers and organizations worldwide. This flaw, embedded in the

Imagine a scenario where a trusted colleague calls with an urgent request for sensitive data, only to later discover it was a hacker in disguise. This chilling reality struck Workday, a leading AI-driven platform for HR and payroll management used by over 11,000 organizations globally, including