Security operations centers are witnessing the complete evaporation of the traditional “grace period” once afforded to IT teams during the window between a vulnerability disclosure and its active exploitation by hostile entities. In the current landscape, the luxury of a multi-week patching cycle has become a dangerous liability. Ransomware groups have refined their internal processes to such a degree that the time between a patch release and a full-scale network encryption event is now measured in hours rather than days. This acceleration is not merely a technical adjustment but a fundamental shift in how digital extortion operates, forcing a total reconsideration of defensive priorities.
The 24-Hour Countdown: Why Traditional Security Is Failing
The concept of a “buffer period” has effectively died as adversaries increasingly automate their scanning and exploitation workflows. Historically, organizations assumed they had a window of at least several days to test and deploy patches for critical vulnerabilities. However, the emergence of Storm-1175, a highly disciplined threat actor, has rewritten the ransomware playbook by demonstrating sub-24-hour deployment capabilities. This extreme operational tempo means that by the time a security advisory is read and digested, the initial intrusion may have already occurred, leaving defenders perpetually playing catch-up in a race they cannot win with legacy processes.
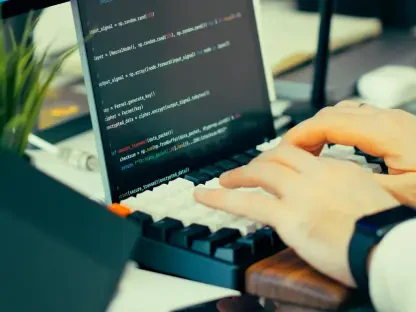
The psychological pressure of this environment on IT departments is immense and often debilitating. When the window for remediation shrinks to a single day, the standard change-management procedures that ensure system stability become obstacles to survival. Staff members face a constant state of high-alert fatigue, knowing that a single missed update during a weekend or a holiday could result in a catastrophic breach. This relentless pace shifts the focus from long-term security posture to a desperate, reactive sprint, often leading to burnout and oversight in complex enterprise environments.
The Evolution of Tempo: Understanding the Storm-1175 Threat
Financial motivations drive the high-velocity nature of these campaigns, as speed directly correlates with a higher success rate and reduced operational costs for the attacker. Storm-1175 operates with a corporate level of efficiency, viewing each vulnerability as a time-sensitive asset that depreciates as more organizations apply patches. By striking quickly, they maximize their return on investment before the majority of the market can close the door. This professionalization of cybercrime ensures that the attackers are always incentivized to find even faster ways to move from an initial exploit to a final ransom demand.
The group specifically weaponizes what researchers call the “Sweet Spot” strategy, which involves targeting N-day vulnerabilities during the first patch cycle. This strategy exploits the reality that even though a patch exists, the logistical hurdle of deploying it across thousands of endpoints takes time. High-value, uptime-critical sectors such as healthcare and finance are the primary targets because their operational dependencies make them more likely to favor availability over immediate patching. For these industries, the cost of a few hours of downtime for a patch often seems higher than the theoretical risk of a breach, a calculation that Storm-1175 exploits with devastating precision.
Anatomy of a Rapid Breach: The Medusa Ransomware Lifecycle
A rapid breach usually begins at the perimeter, where the group exploits vulnerabilities in internet-facing software such as BeyondTrust, CrushFTP, or TeamCity. These tools are essential for remote work and development, yet they often serve as the primary entry point for high-velocity actors. By focusing on these specific gates, attackers can bypass the need for phishing or social engineering, moving straight to technical exploitation. The speed at which these flaws are integrated into the Medusa arsenal suggests a sophisticated exploit development pipeline that mirrors the release cycles of the software companies themselves.
Beyond known vulnerabilities, the group has shown a recurring ability to utilize zero-day exploits, providing them with an invisible advantage over even the most diligent defenders. Once inside, the attackers do not linger; they immediately use remote monitoring and management tools alongside Impacket to move laterally toward sensitive data. To ensure an invisible execution, they perform tactical tampering with Microsoft Defender, adjusting registry keys to exclude critical drives from being scanned. This surgical removal of security hurdles allows the Medusa ransomware payload to run without interference, while double extortion tactics involving data exfiltration via Rclone provide secondary leverage for the final ransom demand.
Expert Perspectives on the “Tempo-Driven” Threat Landscape
Microsoft Threat Intelligence insights suggest that standard monthly patching schedules are now obsolete in the face of such rapid intrusion cycles. Security experts emphasize that the threat is no longer defined by the complexity of the malware itself, but by the speed of the delivery mechanism. The consensus among researchers is that organizations must shift from a reactive mindset to a proactive stance that prioritizes immediate remediation of edge-facing assets. Documented impacts in the United States, United Kingdom, and Australia show that no region is immune to this surge in operational tempo, as the attackers follow the path of least resistance across global networks.
The transition toward high-velocity attacks has forced a re-evaluation of how risk is calculated within the boardroom. Experts argue that the old model of “acceptable risk” is failing because it does not account for the sheer speed of modern exploit weaponization. Case studies of recent intrusions reveal that organizations with robust but slow security protocols were hit just as hard as those with weaker defenses, simply because they could not move fast enough. This realization is driving a move toward automated security orchestration, where the human element is augmented by systems capable of responding at machine speed to match the pace of the adversary.
Hardening the Perimeter: Strategic Defenses Against High-Velocity Attacks
Effective defense against Medusa requires prioritizing the edge through an accelerated patching framework that focuses exclusively on internet-facing assets. Rather than attempting to patch every system at once, organizations should isolate public-facing servers and apply updates within hours of their release. Enforcing Tamper Protection is equally critical, as it prevents unauthorized modifications to antivirus settings and registry keys that attackers use to clear their path. By locking down the security software itself, defenders can ensure that even if an initial breach occurs, the subsequent stages of the attack are flagged and blocked.
Credential safeguarding and infrastructure isolation provide the final layers of a resilient defense. Implementing Windows Credential Guard blocks memory-based dumping, effectively neutralizing tools like Impacket that facilitate lateral movement. Furthermore, the principle of least privilege should be strictly enforced by using configurations such as “DisableLocalAdminMerge” to prevent administrative hijacks. Leveraging Web Application Firewalls and placing legacy systems within a DMZ further shields vulnerable assets from direct exposure. This multi-layered approach does not just stop an attack; it creates enough friction to slow the attacker down, reclaiming the time that high-velocity ransomware seeks to steal.
The landscape of digital extortion underwent a permanent change when the window of opportunity for defenders moved from weeks to hours. Organizations that successfully navigated this transition replaced their rigid, calendar-based maintenance with fluid, risk-based responses that prioritized the perimeter. The focus shifted toward a hardened architecture where tamper-resistant security settings and isolated credentials served as the primary deterrents. By acknowledging that speed was the most potent weapon in the Medusa arsenal, security leaders successfully mitigated the threat through the adoption of automated remediation and aggressive infrastructure shielding. The lessons learned during this period of high-velocity threats provided a blueprint for future resilience, ensuring that the next generation of rapid exploits encountered a defense that was just as fast and disciplined as the attack itself.