The myth of the untraceable ghost in the machine has been shattered by German investigators who recently pierced through the layers of encryption shielding the world’s most notorious cyber-extortionists. The Federal Criminal Police Office (BKA) stripped away the masks of “UNKN” and his associates. This move signals a shift in the battle for digital accountability, proving that the digital realm offers no permanent sanctuary for elite criminals.
Decoding the Identities Behind the Digital Shadows
The goal was linking the digital alias “UNKN” to Daniil Maksimovich Shchukin and identifying Anatoly Sergeevitsch Kravchuk. Investigators aimed to pierce the anonymity of the Ransomware-as-a-Service model to establish legal accountability. Dismantling these barriers demonstrated that physical identity can be recovered despite sophisticated technical shielding.
The Rise and Menace of the REvil Syndicate
REvil evolved from the GandCrab malware to become a dominant force in global extortion. The syndicate utilized a professionalized business structure to target critical infrastructure and global corporations. This investigation became vital due to the group’s role in transforming cybercrime into a high-stakes corporate enterprise with devastating economic consequences.
Research Methodology, Findings, and Implications
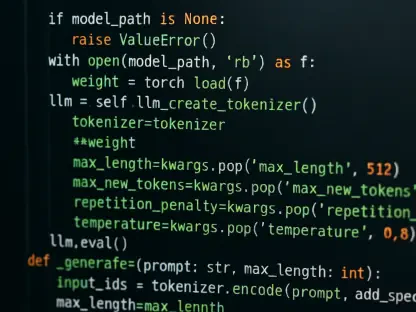
Methodology
Methodology involved forensic analysis of digital infrastructure and tracking ransom flows across decentralized networks. The BKA coordinated international intelligence sharing to synchronize data across global partners. Furthermore, analyzing psychological profiles helped bridge the gap between digital activity and physical identity.
Findings
Investigators identified Daniil Maksimovich Shchukin as the leader and Anatoly Sergeevitsch Kravchuk as the technical developer. In Germany, the group caused over €35.4 million in damages through 130 targeted attacks. Evidence also linked REvil leadership to high-profile incidents like the JBS and Kaseya attacks.
Implications
These revelations shifted the perception of cybercriminals from digitally invincible to legally vulnerable. Disruption of the RaaS ecosystem undermined the trust affiliates once placed in their leaders’ anonymity. The operation proved that multi-national cooperation is the most effective tool for dismantling complex criminal organizations.
Reflection and Future Directions
Reflection
Investigating actors across borders remains difficult due to limited extradition cooperation in certain jurisdictions. The group’s recruitment narrative provided a behavioral trail for forensic investigators. Balancing server disruption with the long-term goal of physical arrests is now a primary focus for law enforcement.
Future Directions
Future strategies involve tracking the migration of former affiliates into new ransomware syndicates. Public unmasking will be expanded as a psychological deterrent against emerging groups. Additionally, refined legal frameworks are needed to prosecute criminals operating from safe-haven countries.
A Turning Point in the Fight Against Cyber-Extortion
The unmasking of REvil’s core leadership represented a breakthrough that established a precedent for ransomware investigations. This operation proved that sophisticated syndicates left traces leading back to their physical origins. Law enforcement successfully eroded the anonymity fueling the cybercrime economy, ensuring actionable next steps toward international justice.