The geopolitical landscape of 2026 demonstrates that the silence of heavy artillery on a physical battlefield rarely coincides with a cessation of hostilities within the digital domain. While diplomatic efforts often succeed in brokering temporary truces to halt kinetic violence, the underlying tension between adversaries frequently finds a new outlet through sophisticated network intrusions and data breaches. This disconnect creates a dangerous illusion of peace for the general public, while security professionals remain locked in a high-stakes struggle against state-sponsored actors who view a military pause as an opportunity to recalibrate rather than a reason to stop. Because cyber operations offer a degree of deniability and lack the immediate visual carnage of a missile strike, they serve as a strategic pressure valve, allowing nations to exert influence and maintain leverage without technically violating the restrictive terms of a formal ceasefire.
Strategic Maneuvers and the Role of Hacktivist Fronts
Modern conflict zones are increasingly populated by “false-flag” hacktivist groups that claim to operate independently while actually serving the specific strategic interests of national governments. A prominent example is the group known as Handala, which gained notoriety for its ransomware attacks and high-profile data breaches. During recent diplomatic shifts between the United States and Iran, this group publicly announced a postponement of operations against American targets, citing orders from high-level leadership. However, such declarations are frequently tactical ruses designed to provide a veneer of diplomatic cooperation while the group remains aggressively active against other regional adversaries. This selective aggression proves that cyberwarfare is a highly calibrated tool that can be dialed up or down to suit the specific needs of a nation’s foreign policy at any given moment.
By maintaining these digital front groups, states can project a public image of restraint during a ceasefire while simultaneously keeping their adversaries off-balance. Security researchers have observed that when physical combat operations are suspended, the frequency of “nuisance-level” attacks—such as distributed denial-of-service (DDoS) strikes against government portals or authentication services—often remains steady or even increases. These activities ensure that the digital frontline remains a live environment, forcing the opponent to continue dedicating significant resources to defense even when their soldiers are no longer in the line of fire. Consequently, the declaration of a truce often marks the beginning of a more complex phase of conflict where the battle for information and psychological dominance takes center stage over the struggle for physical territory.
Historical Evidence of Digital Persistence
Looking back at the past few years, the data regarding regional truces highlights a persistent pattern of digital aggression that survives even the most celebrated peace agreements. During the 2021 and 2023 ceasefires in the Middle East, intelligence reports indicated that Hamas-aligned actors did not stand down but instead transitioned into extensive phishing campaigns targeting regional government officials. These groups utilized the kinetic downtime to gather intelligence and map out critical infrastructure, preparing for the inevitable resumption of physical hostilities. Similarly, during de-escalation periods in the ongoing Ukraine-Russia conflict, both sides continued to target energy grids and logistical networks, demonstrating that for many modern militaries, a ceasefire is merely an “in-between” period used to harden positions and gather technical data on enemy vulnerabilities.
This trend of digital persistence is further complicated by the geographic expansion of targets that often occurs when a kinetic conflict reaches a stalemate. When a war remains localized in a physical sense, the digital component tends to broaden, eventually encompassing any nation or organization perceived as supporting the adversary. This regionalization of cyber threats means that during a ceasefire, security teams in North America and Europe often face an elevated risk profile. Threat actors move away from strictly military-level targets and focus their efforts on broader infrastructure, such as water treatment plants or healthcare systems, to exert indirect pressure on the diplomatic process. This expansion of the target list effectively globalizes the conflict, making it impossible for distant allies to remain truly insulated from the consequences of a local war.
The Strategy of Calibration and Nuisance Attacks
While many cyber operations during a ceasefire are intended to be disruptive, they are also meticulously calibrated to avoid triggering a return to open kinetic warfare. Groups like the 313 Team and the Conquerors Electronic Army often engage in lower-threshold activities, such as defacing public websites or disrupting freelancer platforms, which serve as constant reminders of their presence. These attacks are just significant enough to cause frustration and economic loss, yet they usually fall below the level of an “armed attack” that would justify a military response under international law. This careful balancing act allows a state to signal its continued resolve and maintain its negotiating leverage at the bargaining table, effectively using the digital realm as a laboratory for testing the adversary’s limits and response times during a period of supposed peace.
However, historical anomalies show that cyber activity can be completely silenced if the political stakes are high enough to demand total restraint. During the final months of the 2015 Iran nuclear deal negotiations, analysts observed that malicious cyber probes from Iranian sources against U.S. targets dropped to near-zero levels. This rare instance of a genuine digital stand-down suggests that when a state views a diplomatic outcome as existential—such as the permanent removal of major economic sanctions—it can and will exercise total control over its cyber assets to ensure the deal’s success. This proves that while cyber warfare typically persists through minor military truces, it remains a highly disciplined tool of statecraft that can be deactivated when the potential rewards of a peaceful resolution far outweigh the benefits of continued digital harassment.
Future Safeguards for a Continuous Digital Conflict
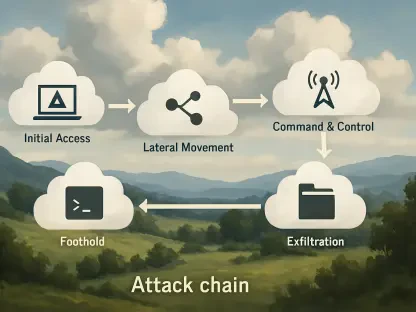
The lessons learned from the volatile landscape of 2026 suggest that organizations must adopt a “constant-conflict” mindset, regardless of the headlines regarding military peace. Since the digital stand-down is largely a myth, security executives should utilize the relative calm of a physical ceasefire to conduct deep-dive audits of their supply chains and critical dependencies. These periods of kinetic de-escalation are the ideal time to implement zero-trust architectures and enhance incident response protocols, as the threat actors are likely using the same time to refine their own intrusion techniques. Waiting for a formal end to hostilities before bolstering defenses is a strategic error, as the most damaging cyber operations often take place during the “quiet” phases of a conflict when vigilance is naturally lower.
Looking forward, the integration of artificial intelligence into both offensive and defensive cyber operations will likely make the distinction between war and peace even more blurred. Moving into the next phase of global security, nations should push for explicit “cyber-clauses” in all future ceasefire agreements, establishing clear red lines for digital conduct that carry the same weight as physical violations. For the private sector, the best defense remains a proactive stance that assumes the network is always under siege, even when the guns are silent. In this era, the true measure of a successful peace treaty will not be the absence of smoke on the battlefield, but the absence of unauthorized persistence within the servers and systems that power modern society. Security protocols had to evolve to meet this reality, ensuring that resilience was built into the very fabric of global infrastructure.