Rupert Marais has spent years at the forefront of digital defense, specializing in the intricate layers of endpoint security and the strategic management of complex networks. As a security specialist, he has witnessed the transition of cybercrime from disorganized mischief to a highly professionalized, billion-dollar industry. His expertise lies in understanding not just the code behind a breach, but the behavioral patterns of the actors who execute them. In this discussion, we explore the shifting dynamics of the ransomware landscape, where attackers are trading their signature tools for the very administrative utilities that IT teams use every day, forcing a total rethink of modern defense-in-depth strategies.
Ransomware payment rates have reached record lows, yet average payment amounts are spiking due to a few high-impact incidents. How are organizations successfully avoiding these payments, and what specific recovery strategies allow them to bypass the pressure of “name and shame” tactics on the Dark Web?
We are seeing a massive shift in the power dynamic between attackers and victims, evidenced by the fact that ransomware payment frequency has plummeted to an all-time low of just 20%. Organizations have finally realized that paying a ransom provides no actual guarantee of data deletion or system stability, so they are investing heavily in resilient, offline backup architectures that make the encryption phase of an attack much less of a “death blow.” By focusing on rapid restoration and immutable storage, companies can effectively ignore the extortion demands, even as “name and shame” posts on the Dark Web reach record highs. While it is true that average payment amounts are spiking, these are outliers driven by a handful of catastrophic breaches rather than a market-wide trend. The reality on the ground is that better incident response planning and cooperation with law enforcement have made it possible for many to weather the storm without handing over a single cent.
Data theft now occurs in over three-quarters of attacks, frequently targeting virtualization infrastructure. What specific vulnerabilities in virtual environments are being exploited, and how should security teams reconfigure their data protection protocols to prevent large-scale exfiltration before encryption even begins?
The shift toward targeting virtualization is a calculated move by threat actors, with intrusions into these environments jumping from 29% to 43% in just a single year. Attackers are drawn to virtualization because it represents the “keys to the kingdom,” allowing them to access hundreds of servers simultaneously from a single point of entry. Because suspected data theft is now present in approximately 77% of all attacks, security teams must move away from focusing solely on the encryption event and start looking at the movements leading up to it. This means implementing strict micro-segmentation within the virtual layer and ensuring that any movement of large data volumes triggers an immediate, automated lockout. We have to treat the virtualization host as the highest-risk asset in the building, applying the same level of scrutiny to it that we would to a primary domain controller.
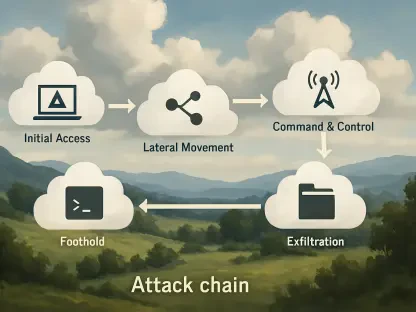
Vulnerabilities in VPNs and firewalls account for a third of initial access cases, while stolen credentials remain a primary foothold. What are the most effective steps for hardening these edge devices, and how can internal identity controls be tightened to stop lateral movement after a breach?
It is a sobering reality that one-third of all successful intrusions start with an exploit on an edge device like a VPN or a firewall—tools that are supposed to be the frontline of our defense. To harden these points, organizations need to move beyond simple patching and adopt a Zero Trust posture where the edge device is no longer the sole arbiter of trust. We see stolen credentials being used in 21% of initial access cases, but more importantly, they are used consistently to maintain a foothold and move laterally through the network. To stop this, identity controls must be granular; we need to implement phishing-resistant multi-factor authentication and strictly limit the privileges of administrative accounts so they cannot be used to jump from a remote access point to the heart of the data center. It is about creating “speed bumps” at every identity junction to ensure that a single compromised set of credentials doesn’t lead to a total environment takeover.
Attackers are moving away from external tools like Cobalt Strike in favor of native utilities like PowerShell and RDP to achieve “evasion through normalcy.” How can defenders distinguish between legitimate administrative tasks and malicious reconnaissance, and what behavioral baselines are most critical to establish?
The decline of “classic” offensive tools is one of the most significant trends we’ve observed, with Cobalt Strike Beacon usage dropping from a staggering 60% in 2021 to a mere 2% last year. Attackers have realized that purpose-built malware is too easy for modern EDR systems to signature and block, so they are opting for “evasion through normalcy” by using the tools already present on the system. Distinguishing between a legitimate admin and a threat actor requires a deep understanding of behavioral context—for example, why is a specific user account suddenly using PowerShell to query Active Directory objects for network shares at 3:00 AM? We also see Remote Desktop Protocol (RDP) being used in a whopping 85% of attacks for lateral movement, which should be a clear signal to defenders. Establishing a baseline of who should be using RDP, from which devices, and at what times is the only way to flag the subtle deviations that indicate a live intruder is roaming your halls.
With the decline of traditional malware, threat actors are increasingly leveraging internal Windows utilities like ipconfig and netstat for reconnaissance. What specific monitoring techniques should be implemented to flag this “living off the land” behavior, and how can automation help teams respond at scale?
When threat actors “live off the land,” they use basic commands like ipconfig, netstat, and nltest to map out the network without ever triggering a traditional virus alarm. These are legitimate tools, but their use in rapid succession or by non-admin accounts is a massive red flag that requires immediate investigation. To catch this, monitoring techniques must shift from signature-based detection to sequence-based analysis, where an automated system flags “reconnaissance chains” of commands that suggest a malicious presence. Automation is the only way to handle this at scale, as it can correlate these low-level alerts with other indicators, like a sudden increase in PowerShell Get-ADUser queries, to isolate a compromised workstation before the attacker can escalate. By the time an attacker starts using these native utilities, they are already inside, so your response must be measured in seconds, not hours, to prevent the 77% data theft rate we are currently seeing across the industry.
What is your forecast for the ransomware ecosystem?
I expect the ransomware landscape to become increasingly bifurcated, where we see a high volume of failed or low-value attacks alongside a small number of extremely sophisticated, high-impact breaches targeting critical infrastructure. As payment rates continue to hover at historic lows, threat actors will likely move further away from mass-encryption and lean even harder into pure data extortion and the exploitation of virtualization layers. We will also see a continued “war of attrition” regarding built-in tooling, as attackers refine their ability to hide within legitimate administrative traffic to bypass maturing endpoint defenses. Ultimately, the survivors in this ecosystem will be the organizations that stop trying to keep the attackers out entirely and instead focus on becoming so resilient and difficult to navigate that the “cost of attack” for the criminal exceeds the potential payout.