
Modern enterprise landscapes are currently defined by a frantic race to acquire massive amounts of computational power through high-end graphics processing units, yet many organizations are discovering that their hardware remains surprisingly underutilized due to insufficient data transfer speeds.

The quiet efficiency with which a single malformed network packet can dismantle the perimeter of a global enterprise has never been more apparent than with the discovery of CVE-2026-0300. This guide serves to illuminate the dangers posed by this critical vulnerability while providing a roadmap for

The delicate balance between allowing users to execute custom scripts and maintaining the impenetrable integrity of a host server has never felt more precarious than it does in today’s interconnected cloud environment. Within the Node.js ecosystem, the vm2 library was once heralded as the
Supply Chain Integrity and the Daemon Tools Incident The modern digital landscape relies heavily on the trust between software developers and their users, a bond that is increasingly exploited through sophisticated supply chain attacks. When Disc Soft, the developer of the ubiquitous disk imaging

The long-standing illusion that a closed-source binary acts as an impenetrable digital vault is finally crumbling under the weight of a single, uncomfortable truth: obscurity is no longer a defense when an algorithm can read what humans cannot. For decades, proprietary vendors operated under the

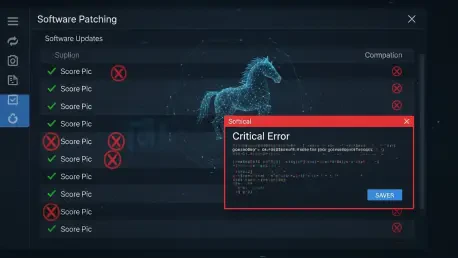
When mission-critical data preservation strategies rely on the seamless execution of background processes, a sudden interruption caused by operating system security updates can disrupt entire business continuities without any immediate warning to the IT administrators responsible for maintenance.