
In an era where digital communication underpins nearly every aspect of business, email continues to be a prime target for cybercriminals, presenting a formidable challenge for organizations across the globe. Cisco, a leader in technology and cybersecurity, processes over 326 million inbound emails

In an era where cyber threats evolve at an unprecedented pace, organizations are under immense pressure to safeguard their digital environments while ensuring that every investment yields tangible value, especially as budgets are often stretched thin and the complexity of attacks continues to

I'm thrilled to sit down with Rupert Marais, our in-house security specialist with deep expertise in endpoint and device security, cybersecurity strategies, and network management. Today, we’re diving into a pressing issue affecting many Windows users—the recent Windows 11 August 2025 Security

What if a seemingly harmless image file could silently compromise an iPhone, iPad, or Mac without any action on the user's part? This chilling possibility became a reality with a recently discovered zero-day vulnerability in Apple's systems, prompting an urgent security patch. In an era where
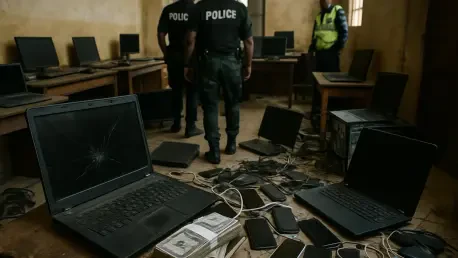
Imagine a digital landscape where nearly 88,000 individuals across Africa fall victim to cybercrime, losing close to $485 million in just a few months, prompting a groundbreaking response through Operation Serengeti 2.0, an Interpol-led initiative that has captured global attention. Conducted over

Imagine a sprawling 70,000-square-meter venue packed with tens of thousands of attendees, over 800 enterprises, and cutting-edge AI innovations—all seamlessly connected in real-time. This was the reality at a major global AI conference in Shanghai this year, where the 5G-A private network emerged