
The deceptive simplicity of legacy protocols often creates the most profound vulnerabilities in modern operating systems, as demonstrated by the persistent survival of Web-based Distributed Authoring and Versioning (WebDAV) within Windows environments. Although Microsoft officially deprecated
The seemingly impenetrable veil of online pseudonymity is rapidly dissolving as advanced language models transform fragmented digital breadcrumbs into comprehensive personal dossiers. This evolution represents a fundamental transition in the cybersecurity landscape, where the sheer volume of
The assumption that a technical professional can simply complete a hardware ticket and leave a secure facility was shattered when a routine field assignment escalated into a full-scale physical detention. A field engineer, identified as Kent, was dispatched to a high-security private datacenter to

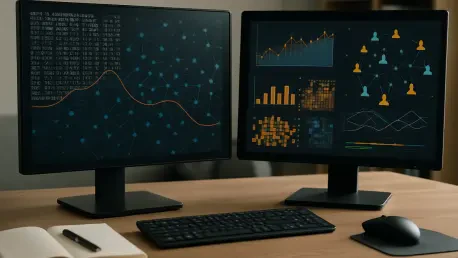
Modern professionals no longer find themselves searching for digital assistance because the tools they use have begun to anticipate their every move before a single click is even made. This transition from passive software to proactive, automated assistants represents a fundamental shift in how

The intricate world of the Linux kernel has always been a sanctuary for cold logic and binary certainty, yet a prominent architect has recently shattered this technical peace with a claim that defies conventional engineering. Kent Overstreet, the primary force behind the high-performance bcachefs
Rupert Marais is a veteran security specialist with an extensive background in securing network management planes and endpoint infrastructure. With years spent hardening large-scale enterprise environments, he provides a critical perspective on the recent warnings issued by the Five Eyes