Cybersecurity experts have recently identified a devastating vulnerability chain within Progress ShareFile that grants unauthenticated attackers complete administrative control over local server environments. The digital landscape faced a severe disruption as researchers uncovered this multi-stage attack path, specifically targeting customer-managed Storage Zones Controller deployments. Enterprises often utilize these specialized controllers to maintain strict data sovereignty and regulatory compliance while still benefiting from the convenience of a cloud-based management interface. This hybrid architecture, however, created a significant blind spot when roughly 30,000 internet-facing instances were found to be susceptible to a complete server takeover by unauthenticated threat actors. These systems represent high-value targets because they act as repositories for sensitive corporate intellectual property and personally identifiable information. The discovered flaws, tracked as CVE-2026-2699 and CVE-2026-2701, essentially dismantled the security perimeter intended to protect on-premises storage. For organizations operating within highly regulated sectors, the existence of such a direct path to the core data infrastructure necessitated an immediate shift in their defensive posture to prevent large-scale exfiltration or ransomware deployment.
The Architecture of Vulnerability: Bypassing Administrative Controls
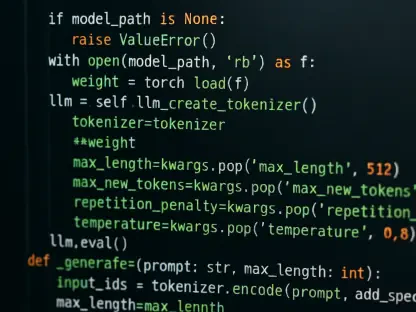
The primary catalyst for this security failure is a critical authentication bypass identified as CVE-2026-2699, which carries a CVSS score of 9.8. This vulnerability arises from a specific programming oversight known as an Execution After Redirect condition located within the Admin.aspx configuration page. Under normal operations, the application is designed to identify unauthenticated requests and issue a 302 redirect command to send the user back to a secure login screen. However, while the client-side browser follows this redirect, the server-side logic continues to execute the remaining code in the background without verifying credentials. This technical glitch allows an attacker to interact with administrative functions that should be strictly gated. By intercepting or ignoring the redirect response, a malicious actor could modify sensitive zone settings, including the manipulation of storage paths and the alteration of encryption passphrases. This failure effectively neutralized the first line of defense for the entire storage controller.
Once the authentication layer was compromised, attackers could transition to the second phase of the exploit, documented as CVE-2026-2701. This flaw facilitates remote code execution by exploiting the way the server handles file uploads and archive extractions within web-accessible directories. By leveraging the unauthorized administrative access gained in the first step, an attacker could upload a malicious ZIP archive containing an ASPX webshell. The system’s failure to properly sanitize the extraction process allowed this shell to be placed directly into the ShareFile webroot, providing a persistent backdoor for arbitrary command execution. Research demonstrations proved that this chain required no prior knowledge of valid credentials, making it an extremely low-friction path for sophisticated ransomware groups looking for an entry point. The ability to execute code at the system level meant that the entire underlying server infrastructure, not just the ShareFile application, was now under the potential control of the adversary, leading to total environment compromise.
Strategic Response: Remediation and Forensic Auditing
Addressing these vulnerabilities required a swift and coordinated response from both the vendor and the affected enterprise administrators. Progress moved to resolve the issues by releasing Storage Zones Controller version 5.12.4, which specifically closed the EAR loophole and hardened the file handling logic. For many organizations, the most effective long-term strategy involved migrating to the 6.x release branch, as these newer versions were built on a modernized framework inherently resistant to the specific flaws found in the 5.x series. The timeline for these updates was tight, with private disclosures occurring early in the quarter to allow for development and testing before the public was alerted. This proactive patching cycle was vital for maintaining the integrity of the global supply chain, especially as automated scanning tools began looking for unpatched systems. Organizations that prioritized these updates successfully insulated their data repositories from the emerging threat, ensuring that their migration to current software standards served as a definitive barrier against exploitation.
Beyond the simple application of software patches, the remediation process demanded a thorough forensic investigation of existing server environments to identify any signs of prior compromise. Security teams conducted deep audits of web-facing directories, searching for unauthorized ASPX files or randomized filenames that typically indicated the presence of a persistent webshell. They also scrutinized the server configuration logs for unexpected changes to storage paths or administrative user roles that occurred before the security updates were finalized. This retrospective analysis was a critical step in confirming that no dormant threats remained within the network architecture. Furthermore, administrators reviewed their perimeter firewall rules to ensure that storage controllers were not unnecessarily exposed to the public internet, moving them behind more robust access gateways or VPNs. These concerted actions not only neutralized the immediate danger posed by the identified vulnerabilities but also strengthened the overall resilience of the enterprise data infrastructure against future sophisticated attacks.