The sophisticated mechanics of modern software delivery have unintentionally birthed a new era of digital vulnerability where the very tools meant to accelerate innovation are now being weaponized against the global supply chain. Modern software development has reached a point where the speed of code delivery often outpaces the human capacity to verify its safety, creating a vast and permeable surface for attackers. In this high-stakes environment, the introduction of Chainguard Factory 2.0 represents a significant shift toward a self-sustaining defense model. This platform leverages the intersection of artificial intelligence and automated orchestration to protect the critical artifacts that power today’s digital infrastructure.
The End of Brittle Scripts and the Rise of Self-Healing Security
The traditional approach to securing software pipelines has long relied on a collection of fragile, manual scripts that tend to crumble the moment an upstream environment undergoes even a minor change. This brittle automation creates a significant amount of security debt where defenses are only as strong as the most recent manual update, leaving vast windows of opportunity for exploitation. By transitioning toward a more durable architecture, developers are now embracing a self-healing model that prioritizes persistent defense over temporary, manual fixes. This evolution marks a departure from “throwaway” code that fails under pressure, replacing it with resilient systems designed for long-term stability.
A fundamental shift occurs when organizations adopt a controller and reconciler model, similar to the architecture used in high-scale orchestration systems. This system does not just perform a single task; it continuously monitors the state of software artifacts to ensure they align with a desired, secure baseline. This persistent security posture effectively automates the process of hardening container images, driving toward a reality where zero-CVE environments are a standard expectation rather than a rare luxury. As these systems identify discrepancies in real-time, they automatically apply patches, ensuring that the software remains protected without requiring constant human intervention.
Why the CI/CD Pipeline Has Become the Ultimate Prize for Hackers
For contemporary cybercriminals, the CI/CD pipeline represents the ultimate prize because it serves as the central nervous system for code deployment, holding high-level credentials and secrets. Attackers have increasingly shifted their focus from targeting finished products to hijacking the development tools themselves, such as popular GitHub Actions or marketplace extensions. By compromising a single widely-used action, a bad actor can gain lateral access to thousands of private repositories, effectively turning a company’s own infrastructure against its developers. This trend highlights a critical vulnerability in the modern workflow where the “keys to the kingdom” are often left exposed through unverified automation.
This threat is further compounded by the hidden dangers of unverified third-party code that populates modern development workflows. As engineering teams pull libraries and actions from public registries, they often bypass rigorous security vetting in favor of speed, leaving their pipelines vulnerable to malicious injections. Furthermore, the rise of AI-driven development introduces agentic risks, where malicious instruction sets—often called “skills”—can trick automated assistants into installing data-stealing malware. The complexity of these attacks means that standard perimeter defenses are no longer sufficient to protect the integrity of the software supply chain.
Inside Factory 2.0: AI Agents and Hardened Infrastructure
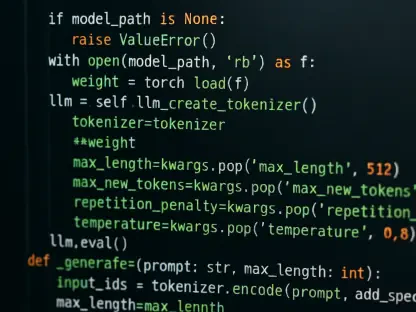
At the heart of this defensive evolution is the DriftlessAF framework, an agentic reconciliation system designed to identify and patch security gaps in real-time. This framework employs intelligent bots that scan for “drift,” which is the discrepancy between a secure, approved version of a tool and its current state. By automating this reconciliation, the infrastructure remains in a state of constant compliance, reducing the window of time that a vulnerability exists before being remediated. This framework allows security teams to manage thousands of artifacts simultaneously, ensuring that every component of the build process remains verified and up to date.
Complementing this framework is a curated catalog of hardened GitHub workflows known as Chainguard Actions, which replace unverified marketplace tools with vetted alternatives. To further secure the AI lifecycle, the system utilizes modular instruction sets that have been audited for malicious commands or unintended behaviors. Additionally, the Chainguard Guardener serves as a sophisticated automation bridge, helping teams migrate legacy Dockerfiles into secure, minimal container images without requiring massive manual intervention. These tools work in tandem to create a hardened ecosystem that protects the software lifecycle from the initial line of code to the final deployment.
Expert Perspectives on Overcoming the Manual Security Bottleneck
Industry experts, including seasoned CISO Adeel Saeed, emphasize that the primary failure of modern security often lies in the bottleneck created by manual artifact management. When security teams are forced to manually download, scan, and re-upload images to internal registries, they inevitably fall behind the pace of rapid development cycles. The solution requires a fundamental shift toward security at scale, where defenses are fully integrated into the existing Git workflows rather than being treated as an external oversight process. This integration ensures that security becomes a foundational element of the development process rather than a secondary consideration.
The goal of this transition is to achieve a delicate balance between developer velocity and the necessity for rigorous security verification. By treating security as a continuous process rather than a final gate, organizations can remove the friction that often leads developers to cut corners or bypass protocols. This unified defense strategy treats every piece of the supply chain—from the code repository to the final deployment—as part of a singular, verifiable ecosystem that resists tampering by design. Ultimately, this approach empowers developers to move quickly while maintaining the highest standards of software integrity and safety.
Frameworks for Implementing AI-Enabled Supply Chain Defense
Implementing an AI-enabled supply chain defense requires a strategic approach to integrating hardened actions into existing CI/CD pipelines. Organizations should begin by identifying high-risk third-party dependencies and replacing them with verified, minimal images that lack the unnecessary bloat where vulnerabilities often hide. This transition is not merely a technical swap; it involves establishing a secure-by-default culture where every automated process is subject to continuous reconciliation. By focusing on the most critical components of the pipeline first, teams can significantly reduce their attack surface while building a roadmap for broader automation.
Moreover, leveraging AI agents to automate the remediation of vulnerabilities allows security teams to move from reactive patching to proactive prevention. Best practices suggest that teams should monitor for drift in all open-source artifacts and utilize agentic frameworks to apply updates the moment a patch is available. By adopting these modular and automated defense frameworks, enterprises can build a resilient development environment that remains secure even as the underlying threat landscape continues to evolve. The realization that traditional security measures were insufficient led to a profound transformation in how organizations approached software integrity. Leaders shifted their focus from static defenses to dynamic, self-healing systems that leveraged AI to outpace potential threats. This transition simplified the complexities of supply chain management and established a new standard where automated verification became the cornerstone of every successful development project.