
Unveiling the Mobile Banking Threat Landscape In today's digital economy, where mobile banking transactions are skyrocketing, a staggering statistic emerges: millions of Android users worldwide are at risk from a sophisticated wave of malware exploiting near-field communication (NFC) technology,
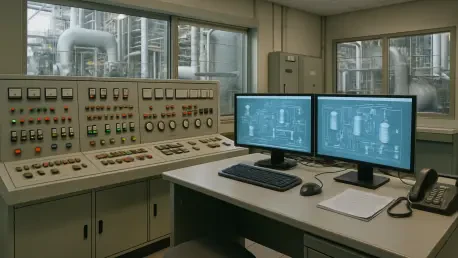
In a world increasingly reliant on interconnected industrial systems, the security of Industrial Control Systems (ICS) and Operational Technology (OT) environments has never been more critical, especially as cyber threats grow in sophistication and impact, posing significant risks to global

Imagine a sprawling digital fortress, housing an organization’s most sensitive data and critical operations, yet harboring hidden cracks that could collapse its defenses in an instant. This is the reality for many businesses relying on Salesforce, a platform that has transformed from a simple CRM

What if a stranger could slip into your car, start the engine, and track your every move with nothing more than your name? This isn’t a plot from a thriller—it’s a real vulnerability uncovered in the digital systems of a major automaker, affecting over 1,000 dealerships across the US. At the DEF

Imagine a seemingly harmless webcam perched on your desk, silently recording your every move, only to transform into a relentless cyber weapon capable of reinfecting your system no matter how many times you wipe it clean. This chilling scenario became a focal point at this year's DEF CON hacker
What happens when a tool as commonplace as WinRAR, relied upon by millions to zip and unzip files, becomes a secret weapon for espionage? In a chilling revelation this year, Russian hackers have been caught exploiting a critical flaw in this widely used software to spy on organizations across