
With his deep expertise in endpoint security and cybersecurity strategy, Rupert Marais has a front-row seat to the evolving battleground of application security. He has spent his career navigating the complex intersection of network management and software development, giving him a unique

With the macOS threat landscape evolving at a breakneck pace, we sat down with Rupert Marais, our in-house security specialist, to dissect a new and particularly deceptive malware strain. This new variant of the MacSync stealer highlights a worrying trend where attackers are successfully using

The invisible redirection of a single software update request can serve as the unassuming first step in a protracted cyber espionage operation designed to remain undetected for years. A recent, highly sophisticated campaign by the China-linked APT group Evasive Panda highlights this new era of
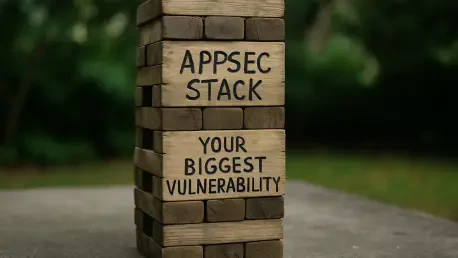
Imagine the moment a critical zero-day vulnerability is announced, sending shockwaves through the industry and your security team into a frantic race against time. As your engineers scramble to patch systems, they reach out to the multiple security vendors whose tools are supposed to be the bedrock

A digital siege is underway in American healthcare, forcing a high-stakes confrontation between federal regulators aiming to fortify defenses and the providers who argue those defenses are operationally unbuildable. The healthcare sector is in a state of high alert, caught between escalating

Today, we're joined by Rupert Marais, our in-house security specialist with deep expertise in endpoint and device security. We'll be delving into the rapidly evolving world of Android malware, exploring a landscape where threat actors are becoming alarmingly sophisticated. Our conversation will