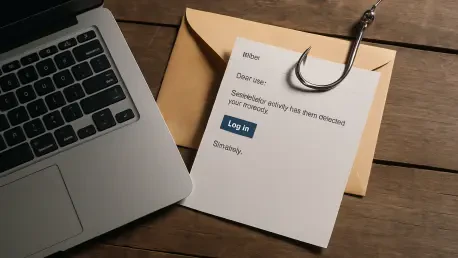
Senior-level professionals across the global technology sector are facing an increasingly sophisticated threat as cybercriminals refine their social engineering tactics to impersonate high-profile recruiters from Palo Alto Networks. This particular campaign, which has been meticulously tracked by the Unit 42 research division, represents a significant departure from standard phishing attempts that typically aim to deploy malicious software or steal login credentials for immediate network access. Instead, these attackers are executing a multi-stage financial fraud scheme that preys upon the professional aspirations and career trajectories of high-ranking executives who are often less susceptible to traditional, less refined lures. By integrating highly specific data points collected from public professional profiles, the threat actors create a convincing facade of a legitimate high-stakes recruitment process. This evolution in cybercrime emphasizes a strategic shift toward high-value targets, where the ultimate objective is not merely data exfiltration but the direct extraction of funds through a series of carefully orchestrated psychological manipulations.
Social Engineering and the Lure of Flattery
The success of this fraudulent operation hinges on a concept known as hyper-personalization, which allows the attackers to bypass the initial skepticism that most modern professionals maintain toward unsolicited outreach. By conducting exhaustive research on platforms like LinkedIn, the scammers are able to reference specific career milestones, past employment history, and even niche professional achievements that would only be known to someone truly invested in the candidate’s field. This level of detail provides a veneer of authenticity that makes the initial contact seem like a genuine inquiry from a top-tier executive search firm. Furthermore, the attackers utilize the exact corporate language and branding expected from a cybersecurity leader, ensuring that every interaction feels consistent with the professional standards of the industry. This meticulous preparation ensures that the victim feels seen and valued as a unique talent, rather than just another name in a massive database, effectively lowering their defensive guard for the subsequent stages of the scam.
Beyond the technical accuracy of the impersonation, the threat actors employ deep psychological flattery to establish a strong rapport with their targets from the very first communication. The language used in these recruitment pitches is often described as being exceptionally complimentary, focusing on the candidate’s supposed influence within the industry and their suitability for a high-impact leadership role. This creates a powerful emotional hook, as the prospect of a career-defining move at a major firm like Palo Alto Networks can occasionally cloud the judgment of even the most cautious individuals. The attackers maintain this professional persona throughout several rounds of dialogue, often using realistic email signature blocks and authentic-looking company logos to reinforce the illusion. By the time the conversation moves toward more sensitive topics, the candidate has typically invested significant time and mental energy into the process, making them more likely to trust the recruiter’s guidance even when the requests start to deviate from standard hiring practices.
The Mechanics of the ATS Alignment Fraud
Once the initial rapport is established and the candidate is fully engaged in the prospect of a new role, the attackers introduce a synthetic bureaucratic barrier designed to trigger professional anxiety. They claim that the candidate’s curriculum vitae or resume has unexpectedly failed to pass the internal Applicant Tracking System (ATS) used by the company’s HR department. In the modern job market, where automated filtering is a standard and often frustrating reality for job seekers, this claim feels entirely plausible and creates an immediate sense of urgency to resolve the issue. The threat actors explain that while the hiring managers are genuinely interested in the candidate’s profile, the system’s automated parameters are preventing the application from moving forward to the final review stage. This manufactured crisis serves as a critical pivot point in the fraud chain, successfully transitioning the interaction from a professional recruitment discussion into a problem-solving scenario that requires the candidate to take immediate, outside action.
To facilitate the financial aspect of the scam, the fake recruiter refers the candidate to an external, third-party service provider who supposedly specializes in optimizing resumes for high-level executive placement. These experts offer a range of tiered service packages that are priced specifically to align with executive-level budgets, ranging from a basic $400 restructuring to a comprehensive $800 overhaul of all professional branding materials. To ensure the victim pays without hesitation, the scammers implement a sense of artificial urgency by claiming that the executive review panel is scheduled to meet within hours and that the updated documents must be submitted immediately to avoid losing the opportunity. The combination of the high-stakes career advancement and the relatively small fee compared to the potential salary increase makes many targets susceptible to the demand. This phase of the operation is where the actual theft occurs, as the payments are funneled through untraceable or fraudulent channels, leaving the victim with nothing but a worthless document and a ghosted recruiter.
Broader Impact on the Hiring Landscape
This campaign highlights a growing vulnerability within the contemporary recruitment landscape, where the increasing digitization of the hiring process has created a significant blind spot for both candidates and employers. The physical and digital distance between internal corporate recruiters and prospective talent allows cybercriminals to inhabit the intermediary spaces without being easily detected. Unlike state-sponsored threat groups that often use job-themed lures for long-term espionage or intelligence gathering, these specific actors are driven by the immediate gratification of direct financial gain. This indicates a broader trend in the threat landscape where traditional criminal organizations are adopting the sophisticated techniques of advanced persistent threats to carry out more profitable social engineering scams. The reliance on automated tools and third-party consultants in the legitimate hiring world provides the perfect cover for these schemes, as victims have become accustomed to interacting with various platforms and vendors throughout a standard application process.
The ramifications of these impersonation scams extend far beyond the immediate financial losses suffered by individual victims, as they also inflict significant reputational harm on the organizations being used as lures. When a prestigious brand like Palo Alto Networks is associated with fraudulent activity, it can deter high-quality talent from engaging with legitimate recruitment efforts in the future, fearing that they might be walking into a trap. This erosion of trust in the professional ecosystem makes it more difficult for companies to attract the specialized leadership required to navigate today’s complex business environment. Furthermore, the data scraped by these attackers to personalize their messages often remains in their possession, potentially being used for secondary attacks or sold on dark web forums to other criminal entities. This dual-layered damage—financial theft from the individual and brand degradation for the corporation—illustrates why these recruitment-themed phishing campaigns are viewed as a serious and evolving threat to the integrity of the global professional labor market.
Defensive Strategies and Red Flags
As the threat landscape continued to shift throughout the first half of the year, security professionals identified several critical red flags that served as the primary line of defense against these schemes. The most prominent indicator of fraud remained any request for payment during the recruitment cycle, as established global enterprises never required candidates to provide funds for resume optimization or application processing. Security experts observed that legitimate hiring processes were always funded internally by the employer, making any demand for outside financial transactions a definitive sign of criminal intent. Furthermore, researchers noted that recruiters rarely mandated the use of specific third-party consultants to bypass internal software filters. By recognizing these patterns, many targeted professionals were able to identify the deception before any financial loss occurred. These observations emphasized that the core of the recruitment scam relied on the victim’s lack of familiarity with the internal administrative protocols of the impersonated firm, which the attackers exploited with surgical precision.
Successful mitigation of these risks required a proactive approach to digital identity and a healthy skepticism toward unsolicited outreach, even when it appeared highly personalized. Professionals who encountered these suspicious communications took immediate action by breaking off all contact and reporting the fraudulent accounts to the security departments of the impersonated companies. This reporting helped organizations like LinkedIn to identify and disable the malicious infrastructure being used to harvest data and distribute phishing messages. Additionally, individuals secured their professional presence by updating their account passwords and ensuring that multi-factor authentication was consistently applied across all platforms. These steps proved essential in preventing the threat actors from gaining a foothold in the victim’s broader digital life. Ultimately, the industry learned that maintaining clear lines of communication through verified corporate channels was the most effective way to validate the legitimacy of a high-level job offer. This collective vigilance allowed the professional community to stay ahead of the evolving tactics used by sophisticated cybercriminal organizations.