When a digital security mechanism intended to protect personal data inadvertently becomes the primary obstacle to accessing it, the fundamental promise of mobile reliability begins to unravel. The iOS keyboard software regression represents a critical inflection point in the evolution of mobile interface management, where a minor update to localized character mapping has effectively locked users out of their encrypted lives. This phenomenon is not merely a glitch but a profound example of how subtle shifts in proprietary software ecosystems can lead to catastrophic data loss. As mobile operating systems become increasingly complex, the intersection of security protocols and user interface design requires a level of precision that even industry leaders occasionally fail to maintain.
The significance of this regression lies in its demonstration of the fragility of modern digital identities. In the broader technological landscape, the shift toward biometric authentication and high-level encryption has marginalized traditional input methods, making them more susceptible to overlooked errors during system updates. When a specific diacritic or character used in a passcode is modified or removed from the lock screen, the physical device becomes an impenetrable brick, highlighting the precarious balance between security and accessibility.
Evolution of iOS Input Systems and Security Protocols
The trajectory of Apple’s input systems has historically moved toward greater localization and inclusive character support, aiming to provide a seamless experience for a global user base. Core principles of this technology involve a dynamic mapping layer that adapts the on-screen keyboard based on regional settings and the specific state of the device, such as the lock screen versus the unlocked home screen. This context is vital because it determines how the operating system interprets every tap as a secure credential or a standard text entry.
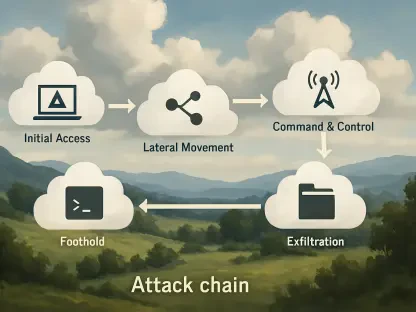
However, as these systems evolved, the focus shifted heavily toward biometrics like Face ID, often leaving the manual alphanumeric interface as a secondary consideration in the development cycle. This shift matters because it created a blind spot in regression testing; while the primary interface might function perfectly, the “Before First Unlock” (BFU) environment—the high-security state after a restart—operates under a more restricted set of rules. The relevance of this evolution is found in the clash between sophisticated user-defined security and the rigid, automated updates of a closed ecosystem.
Technical Architecture of the Lock Screen Interface
Character Mapping and Localization Logic
The underlying logic of the Czech keyboard layout illustrates the complexity of character mapping within the iOS framework. Every key on the virtual board is tied to a specific Unicode value, and in localized versions, these values must account for diacritics like the caron or háček. The technology functions by layering these specific symbols over a standard alphanumeric grid, allowing users to input complex credentials that are significantly harder to crack than simple numeric PINs.
In the current regression, the performance of this mapping logic has failed specifically within the lock screen’s restricted environment. While the general UI might still recognize the character, the security layer responsible for passcode entry has decoupled from the visual keyboard representation. This significance cannot be overstated; the system effectively presents a visual “key” that no longer triggers the corresponding software command, rendering the correct passcode invalid by omission.
The Alphanumeric Passcode Security Layer
The alphanumeric passcode layer is designed to offer the highest level of protection by combining the length of a password with the convenience of a mobile device. This component operates on a deep architectural level, interacting directly with the Secure Enclave to verify credentials without exposing them to the main processor. In real-world usage, this provides a defense against both brute-force attacks and physical coercion, as it does not rely on biological data that can be scanned against a user’s will.
Despite its robust design, this layer’s performance is entirely dependent on the fidelity of the input mechanism. The unique implementation of Apple’s security architecture prevents the use of external peripherals, like USB keyboards, until the device has been unlocked at least once. This creates a technical hurdle where the software failure in the UI layer cannot be bypassed by hardware alternatives, illustrating a rigid design philosophy that prioritizes security at the expense of recovery options.
Current Trends in UI/UX Regression and Testing
Recent developments in mobile software indicate a trend toward rapid, automated deployment cycles that prioritize new features over the stability of legacy input methods. This shift in industry behavior often results in “UI regression,” where updates intended to streamline the interface inadvertently break existing functionalities for specific subsets of users. The trajectory of this technology suggests that as AI-driven testing becomes more prevalent, edge cases involving obscure regional characters are increasingly likely to be overlooked by automated scripts that prioritize common languages.
Moreover, the move toward “universal” codebases across different device tiers sometimes leads to the homogenization of keyboard layouts, which can erase the nuanced diacritics required for localized security. The industry is currently grappling with the trade-off between a unified global design and the specific needs of regional markets. This trend is influencing how manufacturers approach software patches, often favoring broad fixes that may not address the specific character mapping errors currently plaguing localized users.
Real-World Impact and Data Integrity Scenarios
The real-world application of this regression is most visible in the specialized sector of secure data management, where individuals rely on unique character sets to protect sensitive information. For instance, in legal or journalistic fields where data integrity is paramount, a sophisticated passcode is a standard requirement. However, when an overnight update alters the keyboard, these users find themselves in “data limbo,” where their information exists in an encrypted state but is inaccessible due to a software-induced loss of the “key.”
Notable implementations of this technology in the consumer market have shown that the lack of local backup options exacerbates the impact of such bugs. When users opt out of cloud services like iCloud for privacy reasons, they become entirely dependent on the physical device’s interface. This creates a scenario where the hardware remains functional, but the data becomes functionally extinct. The disconnect between Apple’s “restore” policy—which erases all data—and the user’s need for recovery highlights a significant gap in current mobile support infrastructures.
Critical Challenges and Technical Hurdles
One of the primary challenges facing this technology is the “signing” system that prevents users from downgrading to a previous, functional version of the operating system. This regulatory-like obstacle is intended to ensure that all devices remain on the most secure version of the software, but it effectively traps users in a broken state if the current version contains a regression. Mitigating these limitations requires a more flexible approach to software versioning, allowing for emergency rollbacks when a critical UI bug is identified.
Furthermore, the technical hurdle of the BFU state remains a significant barrier. Because the device will not recognize wired accessories or advanced scanning features until the first passcode is entered, there is no viable workaround for a broken on-screen keyboard. Ongoing development efforts must focus on creating a “safe mode” for input, perhaps through a secondary, simplified character picker that remains constant regardless of UI updates. Without such a safety net, the risk of permanent lockout remains a deterrent for users seeking high-level customization in their security settings.
Future Prospects of Mobile Authentication and Recovery
Looking forward, the industry is likely moving toward a more decentralized model of authentication that could decouple the input method from the operating system’s primary UI. Potential breakthroughs might include the use of secondary “recovery keys” stored on separate hardware or encrypted physical tokens that can bypass the on-screen keyboard entirely during a BFU state. This would provide a necessary failsafe for the rare but devastating instances of software regression seen today.
The long-term impact of these developments will likely be a reevaluation of the “walled garden” philosophy. As users demand more control over their data and the ability to recover from manufacturer errors, we may see a shift toward more open recovery protocols. This could involve industry-wide standards for data extraction in lockout scenarios, ensuring that a software glitch does not equate to a permanent loss of digital history. The evolution of mobile security will eventually have to prioritize the user’s right to their own data over the rigid simplicity of the interface.
Assessment of the Current Software Landscape
The review of the iOS keyboard regression clarified that even the most secure systems are vulnerable to the unintended consequences of minor interface changes. It was observed that the current state of mobile software prioritizes centralized control and biometric convenience over the reliability of manual input methods. This imbalance created a scenario where users who exercised high levels of personal security were the most punished by systemic updates. The analysis showed that the lack of a functional “safe mode” or a method to revert to stable software versions represented a significant flaw in the proprietary ecosystem.
Ultimately, the technology demonstrated a need for more robust localized testing and a reconsidered approach to user recovery. The verdict indicated that while Apple’s security remains industry-leading, its failure to account for edge cases in character mapping led to an unacceptable risk of data loss. Future advancements must address these gaps by providing users with alternative input methods or more flexible software management tools. The landscape of mobile authentication was proved to be in a state of transition, requiring a more nuanced approach to ensure that protection does not inadvertently turn into exclusion.