Rupert Marais is a distinguished security specialist with deep expertise in endpoint protection, cybersecurity strategy, and the intricate world of mobile network management. Having spent years dissecting the methods of sophisticated threat actors, he offers a seasoned perspective on the evolution of mobile malware and the shifting landscape of digital asset theft. In this conversation, we explore the resurgence of the SparkCat trojan, its clever concealment within common utility apps, and the technical mechanisms it uses to compromise cryptocurrency security through image analysis.
SparkCat hides in enterprise messengers and food delivery apps. How do these malicious versions successfully bypass official store vetting, and what suspicious behaviors should users monitor when an app requests permission to view their entire photo gallery?
The primary reason these infected apps slip through the cracks of the Apple App Store and Google Play Store is their ability to masquerade as perfectly functional, benign services. By using cross-platform programming languages and multiple layers of obfuscation, developers can hide the malicious payload until the app is already residing on a user’s device. For instance, a food delivery app might function exactly as expected—letting you order a meal and track a driver—while the SparkCat trojan silently runs its reconnaissance in the background. Users must stay vigilant when an app’s requested permissions don’t match its utility; there is no logical reason for a basic messenger or a food app to require deep access to your entire photo library. If you feel your phone growing unusually warm or see a sudden spike in data usage while looking at your gallery, it is a significant red flag that a hidden process is indexing your personal files.
Threat actors are now using optical character recognition to identify recovery phrases in mobile photo libraries. Can you explain the technical workflow of this OCR-based exfiltration and describe the specific network or battery metrics that might signal an active scan is occurring in the background?
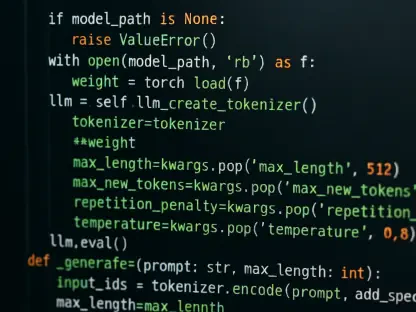
The technical workflow is chillingly efficient: once the malware gains access to the photo gallery, it activates an integrated optical character recognition module to “read” every image on the device. It specifically hunts for high-value text strings, such as the 12 or 24-word mnemonic phrases used to recover cryptocurrency wallets. When the OCR engine identifies these relevant keywords, the malware doesn’t just log the text; it bundles the entire image and exfiltrates it to an attacker-controlled server for manual exploitation. You can often spot this activity by monitoring your battery health, as the intensive CPU cycles required for image processing will drain your percentage much faster than usual. Furthermore, a sudden surge in outbound network traffic, particularly when the phone should be idle, often points to the malware uploading these heavy image files to the threat actor’s infrastructure.
The Android version of this malware uses code virtualization and targets specific Asian languages, while the iOS version focuses on English mnemonics. Why do developers vary their obfuscation techniques by operating system, and what unique risks does this platform-specific tailoring pose to international users?
Developers vary their techniques to exploit the specific architectural weaknesses and user demographics of each platform. On Android, the use of code virtualization creates a complex environment that sidesteps traditional signature-based analysis, making it incredibly difficult for standard security tools to decompile the malicious intent. The focus on Japanese, Korean, and Chinese keywords on Android suggests a highly targeted campaign against the massive crypto-user base in Asia. In contrast, the iOS variant targets English mnemonics, which dramatically broadens the threat’s reach because English is the global standard for the majority of cryptocurrency recovery phrases. This tailoring means that while an Asian user might be targeted via localized Android apps, any iOS user globally is at risk if they have ever screenshotted their recovery keys, making the threat truly borderless.
Recent observations suggest this malware is the work of a Chinese-speaking operator and has transitioned into an actively evolving threat. How has the technical sophistication of the malware’s backend infrastructure changed lately, and what steps should organizations take to defend employee devices against such targeted data theft?
Since SparkCat was first documented in February 2025, we have seen it transition from a relatively simple data stealer into a highly resilient and modular operation. The backend infrastructure now demonstrates a level of sophistication consistent with a dedicated professional group, likely a Chinese-speaking operator, who is constantly refining the code to bypass updated store filters. To defend against this, organizations must move beyond basic MDM policies and implement robust mobile security solutions that can detect anomalous background processes and unauthorized OCR activity. Employees should be strictly educated on the dangers of “credential hygiene,” specifically the risks of storing sensitive wallet phrases as unencrypted images in their galleries. It only takes one compromised device to lead to a total loss of digital assets, so implementing a zero-trust approach to mobile app permissions is no longer optional—it is a necessity.
What is your forecast for SparkCat?
I anticipate that SparkCat will continue to evolve by integrating even more advanced machine learning models to identify a wider variety of sensitive documents, such as passports or bank statements. As long as users continue the habit of taking screenshots of their most sensitive data for convenience, threat actors will find profitable ways to automate the theft of those images. We will likely see this malware expand its language libraries to target more regions, and the obfuscation will become so deep that even advanced sandboxing might struggle to keep up. The battle will move from simply blocking “bad” apps to a more nuanced monitoring of how apps interact with local data in real-time, making proactive mobile security the most critical tool in a user’s arsenal.