Rupert Marais is a veteran security specialist who has spent years at the intersection of endpoint protection and network management. His expertise lies in dissecting how modern attackers bypass traditional defenses by targeting the trust relationships between software vendors and their users. In this discussion, we explore the mechanics of the CPUID breach, where a backend API compromise turned a reputable utility download site into a malware distribution hub, and what this means for the future of software supply chain integrity.
When a secondary backend API is hijacked to swap download links while leaving the original software builds untouched, what specific vulnerabilities are typically exploited? How can security teams better monitor these “side” components to prevent a six-hour exposure window?
In scenarios like the CPUID breach, attackers often exploit broken authentication or insecure direct object references within the administrative interface of the API. These “side” components are frequently less scrutinized than the core software builds, allowing an attacker who gains access to redirect traffic by simply updating a database entry or a configuration file. To prevent a six-hour exposure window, teams must implement real-time integrity monitoring for their web manifests and download metadata, ensuring that any change to a URL triggers an immediate alert. You should also be running automated hash-consistency checks every few minutes to compare the live download link against the known-good hash of the signed binary. By treating the API as a high-value target and applying strict rate limiting and multi-factor authentication to its management endpoints, organizations can shrink that window of vulnerability significantly.
The use of a fake CRYPTBASE.dll to inject payloads into memory via PowerShell presents significant challenges for traditional antivirus tools. What are the primary indicators of compromise for fileless malware that stays off-disk, and what step-by-step process should a user follow if they suspect a malicious process injection?
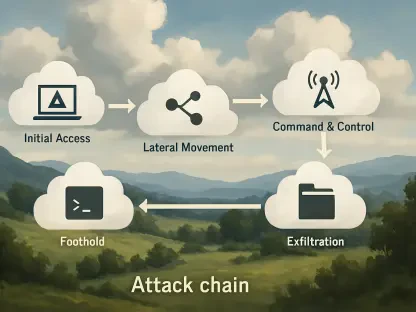
Fileless malware is particularly insidious because it hides in plain sight, but you can still find its fingerprints in system memory and command-line logs. Primary indicators include unusual PowerShell execution strings—especially those containing “EncodedCommand” or “IEX”—and unexpected network connections originating from legitimate Windows processes like svchost.exe or explorer.exe. If you suspect an injection, the first step is to isolate the machine from the network to kill the command-and-control communication. Next, use a tool like Process Explorer to look for threads with “RWX” (Read, Write, Execute) permissions that lack a corresponding file on disk, which is a classic sign of injected code. Finally, perform a cold reboot and conduct a forensic scan of your boot sectors and scheduled tasks to ensure the malware hasn’t established a persistence mechanism that survives a restart.
Threat actors are increasingly targeting the Google Chrome IElevation COM interface to decrypt and steal stored credentials. How does this specific exploitation path bypass standard browser protections, and what are the practical trade-offs of relying on browser-based password managers versus dedicated, encrypted third-party solutions?
The IElevation COM interface is targeted because it allows an application to request elevated privileges to perform certain tasks, which the malware exploits to trick the browser into handing over the encryption keys for the local login data. This bypasses the standard sandbox protections because the request appears to come from a legitimate internal process rather than an external threat. Relying on browser-based managers is convenient, but it places all your eggs in one basket that is constantly being poked by every piece of malware on your system. Dedicated third-party solutions usually offer a more robust security posture by using independent encryption schemas and requiring master passwords that aren’t cached in the same way, though they do introduce an extra layer of friction for the average user.
When the infrastructure used in a hijacking mirrors patterns seen in previous campaigns against tools like FileZilla, what does this reveal about the threat actor’s playbook? How can organizations use these historical connections to harden their delivery mechanisms and anticipate future targets?
This pattern shows us that we are dealing with a disciplined threat actor who treats cybercrime like a professional operation, reusing infrastructure and scripts because they have a proven track record of success. It reveals a preference for targeting “developer-adjacent” tools—software that system administrators and power users trust—because compromising one such tool provides a gateway into thousands of high-value corporate networks. Organizations can use these historical connections to proactively block known malicious IP ranges and domain naming patterns associated with previous campaigns like the FileZilla incident. By studying these playbooks, security teams can anticipate that the next target will likely be a similar utility, allowing them to harden those specific delivery mechanisms with stricter CDN controls and more frequent external audits before an attack occurs.
What is your forecast for the security of software utility distribution platforms?
I expect we will see a significant shift toward mandatory cryptographic signing of the entire delivery chain, not just the binaries themselves. As attackers continue to target the “links in between” like APIs and CDNs, platforms will have to adopt technologies like Transparency Logs—similar to what we see with SSL certificates—so that any change to a download path is publicly auditable and immutable. We are moving toward a “Zero Trust” model for software distribution where the website itself is no longer trusted; instead, the client-side installer will verify the entire path from the vendor’s private key to the local machine before any execution happens. It will be a difficult transition for smaller utility developers, but it is the only way to restore trust in an ecosystem where even a signed file can be wrapped in a malicious cloak.