
In today’s digitally driven business landscape, data has become a valuable asset that organizations leverage to elevate decision-making and innovation—and ultimately unlock a greater competitive edge. However, with the increasing volume and complexity of data, the risk of breaches and security

Amidst the dynamic nature of modern work environments, characterized by the adoption of hybrid models, the conventional boundaries of office spaces are becoming history. This shift presents new possibilities for collaboration and heightened work efficiency, but it also brings unprecedented
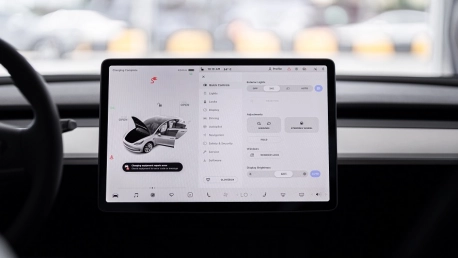
As with every other industry, the automotive sector has seen a massive uptick in cyberthreats since its digital transformation started to pick up pace. The incorporation of Internet of Things (IoT) devices, infotainment systems, autonomous driving, and other connected technologies has opened up new

In the tapestry of the digital age, data security has evolved from a mere necessity to an indispensable pillar of modern society. The rapid proliferation of technology and the exponential growth of interconnected systems have ushered in an era of unparalleled convenience and productivity. Yet, this

The integration of artificial intelligence (AI) in third-party risk management (TPRM) processes has opened up a realm of transformative possibilities. In today’s increasingly interconnected business landscape, where organizations heavily rely on third-party vendors to meet their operational needs,

Whether you’re a profitable enterprise or startup venture, data has become an invaluable asset for most thriving establishments. From customer information to proprietary technology, data is at the core of decision-making, innovation, and gaining a competitive advantage. However, as reliance on data