The sudden weaponization of a trusted security pillar like Trivy proves that even the most fortified digital gateways can be turned into trojan horses for the very environments they were designed to protect. The Trivy Supply Chain Attack represents a significant advancement in the cloud-native threat landscape, shifting the conversation from simple data leaks to systemic infrastructure sabotage. This review will explore the evolution of the technology, its key features, performance metrics, and the impact it has had on various applications. The purpose of this review is to provide a thorough understanding of the technology, its current capabilities, and its potential future development.
Evolution of the Trivy Ecosystem Breach
The Trivy supply chain attack, orchestrated by the threat actor group TeamPCP, emerged as a sophisticated multi-stage campaign targeting one of the industry’s most trusted vulnerability scanners. Unlike previous incidents that focused on peripheral dependencies, this campaign struck at the core of the DevOps security stack. Built on the core principles of exploiting CI/CD pipelines, the attack evolved from simple credential harvesting to a complex distribution network involving Docker Hub and GitHub Actions. This progression indicates a maturing adversary capable of navigating the intricate overlaps between public open-source development and private corporate infrastructure.
The significance of this evolution lies in the choice of target; by compromising a vulnerability scanner, the attackers ensured their payload would be executed in high-privilege environments where security checks are often bypassed for the sake of the tool itself. This incident highlights a critical shift in the broader technological landscape, where security tools themselves are weaponized to facilitate systemic failures in software integrity. The breach proves that the perimeter is no longer a physical or network boundary but a series of interconnected trust relationships that can be shattered by a single compromised token.
Anatomy of the TeamPCP Exploitation Framework
Credential Harvesting and Account Bridging
The primary component of the attack was the compromise of the “Argon-DevOps-Mgt” service account, a discovery that revealed a massive architectural blind spot in modern DevOps management. This account functioned as a technical bridge between Aqua Security’s public open-source repositories and their proprietary internal systems. This bridging allowed the threat actors to move laterally from a public-facing contribution environment into the heart of a private development lab. By securing this single point of failure, attackers gained administrative control, demonstrating how a single compromised token can bypass traditional perimeter defenses and render layered security strategies moot.
What makes this implementation unique is the exploitation of the “God-mode” access often granted to automation bots. Because these service accounts are designed to handle mundane tasks across multiple repositories, they often possess permissions that far exceed their actual needs. This over-provisioning allowed TeamPCP to not only read source code but to actively modify the release mechanisms of the scanner. It serves as a stark reminder that the digital identity of a bot is just as critical—and often more vulnerable—than that of a human developer.
Trojanized Container Images and Action Manipulation
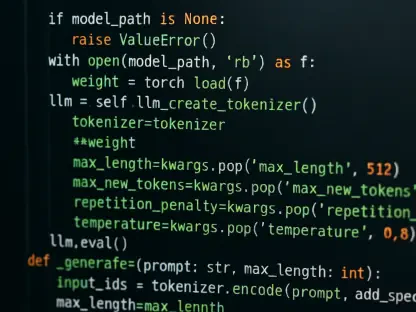
The attackers successfully injected malicious payloads into Trivy versions 0.69.4 through 0.69.6, marking a masterful execution of a versioning exploit. This component of the attack involved pushing malicious tags to Docker Hub without corresponding source code updates on GitHub, creating a discrepancy that most automated scanners are not programmed to detect. Simultaneously, GitHub Actions such as trivy-action were modified to execute malicious entry points, ensuring that any pipeline referencing these tags would automatically deploy the TeamPCP infostealer. This allowed the malware to blend in with legitimate traffic, as the “update” appeared to be a routine patch coming from a verified source.
The subtlety of this manipulation is what differentiates it from more primitive attacks. By altering the entrypoint.sh or the container’s metadata, the attackers ensured that the malicious code ran before the actual scanning engine even initialized. Consequently, the tool meant to detect vulnerabilities would actually exfiltrate the environment’s secrets—such as API keys and cloud credentials—before it could report any issues. This creates a paradox where the act of scanning for security risks becomes the primary security risk itself.
The CanisterWorm and Kamikaze Wiper
A standout technical feature of this campaign was the deployment of the CanisterWorm, a self-propagating mechanism used to distribute the “kamikaze” wiper. This malware evaluates the host environment for specific geo-political markers, such as IP address ranges or language settings, before choosing its course of action. In targeted Kubernetes clusters, it deploys privileged DaemonSets to perform a total environmental wipe, while non-targeted systems are fitted with a persistent backdoor for long-term data exfiltration. This dual-purpose payload allows the attackers to maximize utility: they can either destroy the target’s infrastructure or maintain a silent presence for future intelligence gathering.
The “kamikaze” wiper is particularly lethal because it leverages the orchestration power of Kubernetes against the cluster itself. By utilizing DaemonSets, the malware ensures that its destructive script runs on every single node, including the control plane. This is not just a simple file deletion; it is an architectural demolition that can render a cloud environment unrecoverable within minutes. The implementation of such a destructive tool within a software supply chain attack signals a departure from purely financial motives toward more aggressive, state-aligned or nihilistic objectives.
Emerging Trends in Software Supply Chain Threats
The industry is currently witnessing a shift toward more destructive and geo-politically motivated payloads. In the recent past, the majority of supply chain compromises were aimed at silent resource theft, such as installing hidden cryptocurrency miners that drained CPU cycles without alerting the victim. However, recent developments indicate a trend toward infrastructure annihilation, where the goal is to cause maximum downtime and data loss. This shift reflects a more hostile digital environment where the objective is no longer just profit, but strategic disruption and the total erasure of a competitor’s or adversary’s operational capacity.
Furthermore, the “long tail” of credential vulnerability suggests that dormant tokens are increasingly being weaponized months after the initial breach. This trend necessitates a shift in how organizations monitor long-lived service accounts, moving away from static password rotations toward dynamic, short-lived identity tokens. The Trivy incident highlighted that a token stolen today might not be used for weeks, waiting for the perfect moment when a specific version release can be targeted to maximize the blast radius. This patience on the part of attackers makes traditional, point-in-time security audits less effective.
Real-World Impact Across the DevOps Lifecycle
This technology has been deployed with devastating effects across various sectors that rely on cloud-native infrastructure, proving that no industry is immune to supply chain subversion.
- CI/CD Pipeline Compromise: Global developer environments were used as execution platforms for the infostealer, leading to the leak of proprietary source code. The breach was so seamless that many organizations did not realize their secrets were being harvested until their internal repositories began appearing on public forums.
- Kubernetes Cluster Destruction: The “kamikaze” wiper has been utilized to target specific infrastructure, demonstrating the vulnerability of container orchestration layers to privileged DaemonSet exploits. This resulted in significant downtime for services that were caught in the crosshairs, requiring a total rebuild of the affected cloud environments from off-site backups.
- Repository Defacement: The rapid, scripted renaming of internal repositories serves as a notable implementation of automated supply chain defacement. While less destructive than a wiper, this tactic ruins brand reputation and causes internal chaos, as developers lose access to the resources they need to remediate the primary breach.
Challenges and Mitigation Strategies in Pipeline Security
The widespread adoption of this attack methodology faces several hurdles as the security community develops countermeasures. A significant technical hurdle is the industry-wide reliance on mutable tags, such as @v1 or @latest, which can be reassigned by attackers without leaving a trace in the version history. This practice is inherently insecure because it trusts the repository maintainer’s account security implicitly. Transitioning away from this “convenience-first” approach is difficult, as it requires developers to manually update hashes and manage a much more complex dependency tree.
Regulatory and technical challenges remain in enforcing the principle of least privilege for “bridge” accounts that span across public and private organizations. Many companies find that their automation tools require broad permissions to function correctly, making it difficult to lock them down without breaking established workflows. Ongoing development efforts are focused on utilizing GitHub’s Events API to identify anomalous, high-velocity repository modifications. By using machine learning to baseline normal bot behavior, security teams hope to flag the scripted bursts of activity that characterize a token takeover before the damage becomes irreversible.
Future Trajectory of Cloud-Native Exploits
Looking ahead, the technology behind supply chain attacks is expected to become even more automated and targeted. Potential breakthroughs may include the use of AI to identify the weakest links in dependency trees more efficiently, allowing attackers to find the one obscure library that can bring down a major enterprise. This “precision strike” capability would make it impossible for even well-resourced teams to secure every possible entry point. In the long term, this will likely force a total industry transition toward immutable references, such as SHA-256 pinning, as the only viable defense against version manipulation.
The movement toward zero-trust architectures within the CI/CD pipeline itself will likely become the standard. Instead of trusting a tool because it is “official,” future systems will likely require every action to be signed and verified by multiple independent entities. This would mean that even if a service account is compromised, the attacker would not have the necessary keys to sign a malicious release. While this adds significant friction to the development process, the alternative—a total collapse of the digital supply chain—is increasingly viewed as an unacceptable risk.
Assessment of the Current Security Landscape
The Trivy incident functioned as a harsh wake-up call for an industry that had become overly reliant on the perceived safety of open-source security tools. It highlighted that the very mechanisms used to verify the integrity of our software are themselves susceptible to the same vulnerabilities they aim to solve. The transition from data theft to infrastructure wiping demonstrated that the stakes of supply chain security moved from financial loss to total operational collapse. This review showed that the vulnerability was not in the code of the scanner itself, but in the trust models governing its distribution and management.
To move forward, the security community adopted a more cynical approach to automation, favoring cryptographic certainty over the convenience of mutable version tags. Organizations began auditing their “bridge” accounts with the same scrutiny reserved for high-level executive access, recognizing that a bot can do more damage in seconds than a human can in a day. The shift toward immutable SHA-256 pinning became the industry standard, effectively neutralizing the threat of tag-hijacking. Ultimately, the breach forced a maturation of the DevOps lifecycle, resulting in a more resilient, if more complex, global technology sector.